Public VCF as-a-Service - Creating network components from the Public VCF as-a-Service control panel
This guide can evolve and be updated in the future with the advances of our teams in charge of this product.
Objective
To create, configure and effectively manage your network (IP spaces, Edge gateways and providers, and private network) from the Public VCF as-a-Service control panel.
Requirements
If you are unsure how to log in to your organization's web portal, first refer to the guide: How to log in to Public VCF as-a-Service.
- A web browser (with a preference of chromium based one, and translation enabled in English).
- A Public VCF as-a-Service (Alpha phase) account with sufficient rights.
You need to have read the Public VCF as-a-Service guides:
- Public VCF as-a-Service - Networking - Network concepts Public VCF as-a-Service.
- Public VCF as-a-Service - The fundamentals of Public VCF as-a-Service.
- Public VCF as-a-Service - Connect to your organization.
Instructions
Before creating a network, the main concept to understand with Public VCF as-a-Service is the IP space. For example, consider the default one created with your Public VCF as-a-Service organization:
The internal scope represents the entire IP of your future network, e.g.: 192.168.0.0/24.
- IP ranges are IPs that you can request individually for your services (VMs not using DHCP for example). None here.
- IP prefixes are the IP subnet that you can use in your Edge Gateway, for example.
- IP ranges and IP prefixes cannot overlap and must be within the Internal Scope.
Step 1: Create the IP space (recommended)
You can use a new method of managing your IP space in Public VCF as-a-Service with the new IP space management subsystem.
How to create an IP space with Public VCF as-a-Service?
To connect to your Public VCF as-a-Service environment, follow the guide: How to connect to Public VCF as-a-Service.
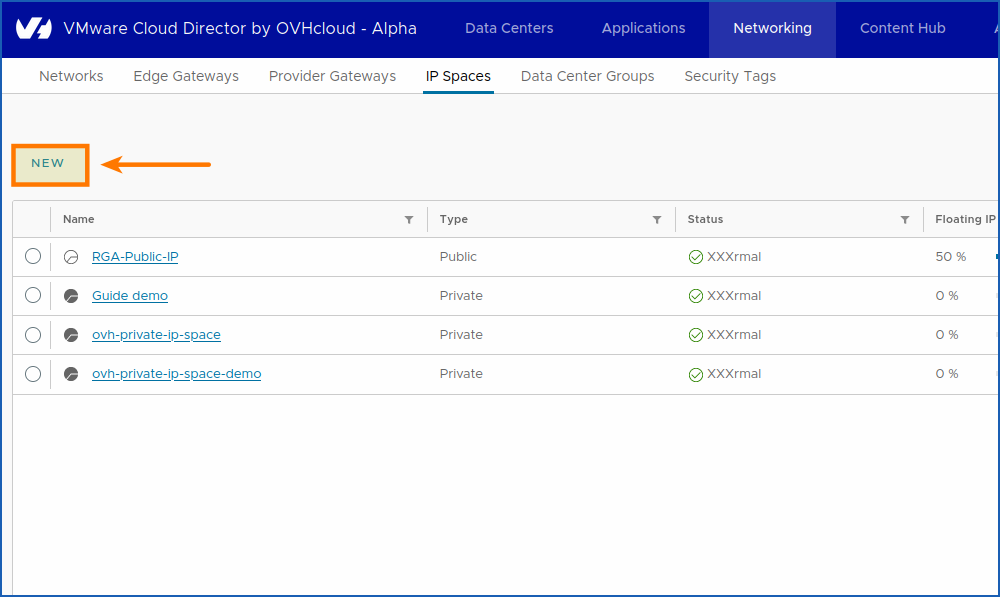
1. Next, click Network > IP Spaces > New.
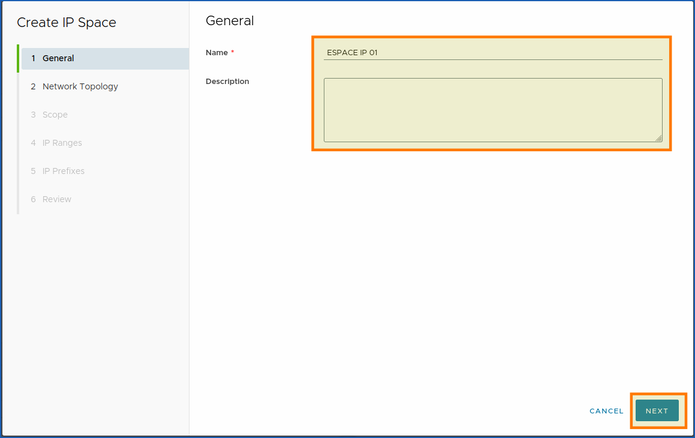
You will find the window for creating an IP space for your network, and choose the name you want:
Example:
- Name:
IP Space 01. - Description:
Private > Public IP Space.
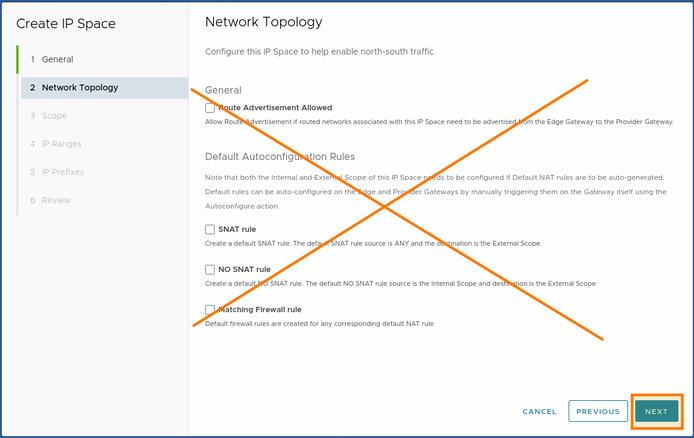
2. Leave the following options disabled for now.
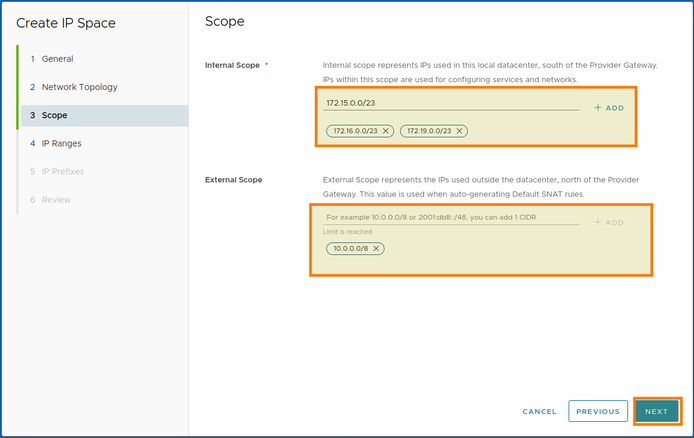
3. Choose the perimeter (ported/extended), (internal/external), with which you want to access your network:
- Internal Scope: Represents the IPs used in this local datacentre, south of Provider Gateway. The IPs in this scope are used to configure services and networks.
- External Scope: Represents IPs used outside the datacentre, north of Provider Gateway. This value is used when automatically generating default SNAT rules.
Then click NEXT.
The IP ranges must correspond to the internal scope of this IP space (the range of IPs you want to make available for your machines).
4. Click ADD.
Example: 172.19.0.2-172.19.0.100.
Then click NEXT.
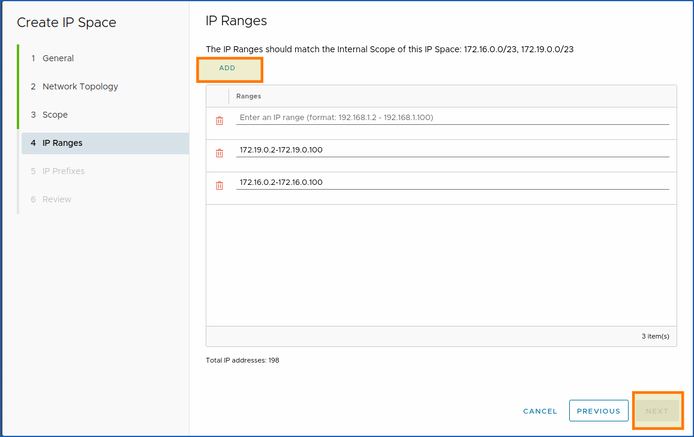
IP prefixes must match the internal scope of this IP space:
5. Click ADD.
Then add your sequences and prefixes.
Example: 10.0.0.0/23 | 1.
You can increase or decrease your number of prefixes with the (up/down) arrow: 
The sequence addition is automatically added as a preview if it is conclusive.
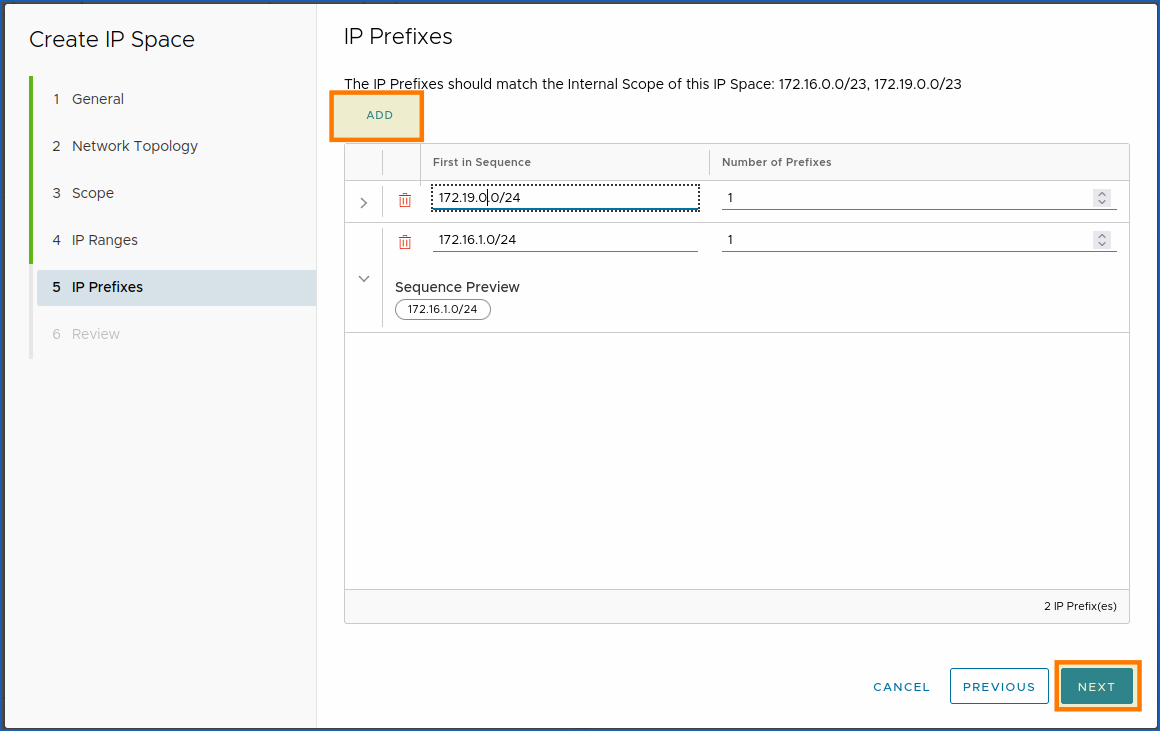
Click NEXT to complete step 5.
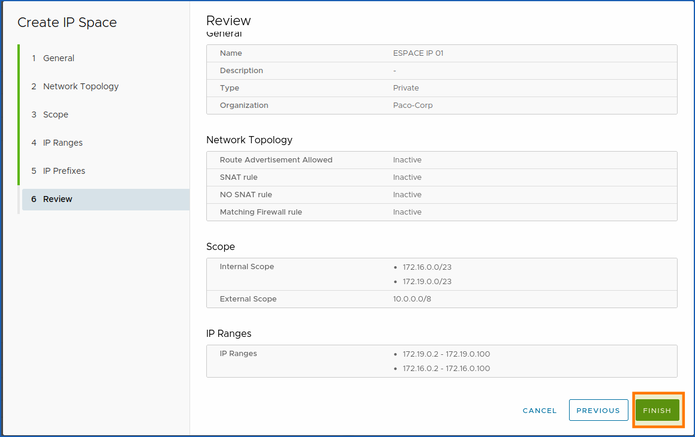
6. The final section is a thorough review of all the settings you have made. You can then check and confirm your choice by clicking on the button FINISH.
Next, we will move on to the Public VCF as-a-Service section VCD > Network > IP Space and/or VCD Network > Network.
Step 2 - Create a datacentre group (optional)
You can use a new method of managing your IP space in Public VCF as-a-Service with the new IP space management subsystem.
How do I create a datacentre group?
Use cases:
This step is optional, but recommended for the vast majority of use cases (e.g. when two VDC networks need to add up).
We will now create a datacentre group to optimize the management of our network with this new Public VCF as-a-Service feature.
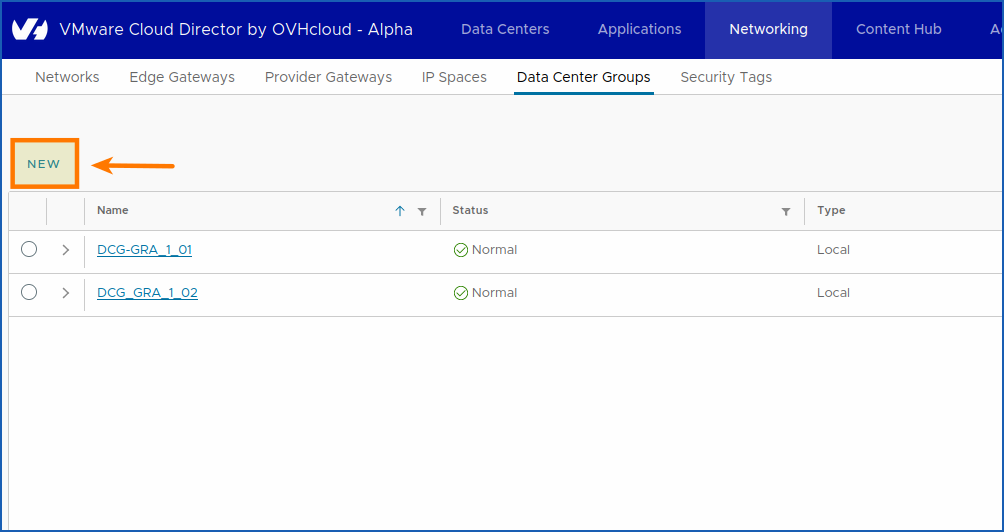
Go to the Networking section by clicking Networking > Data Center Groups.
Then click on NEW.
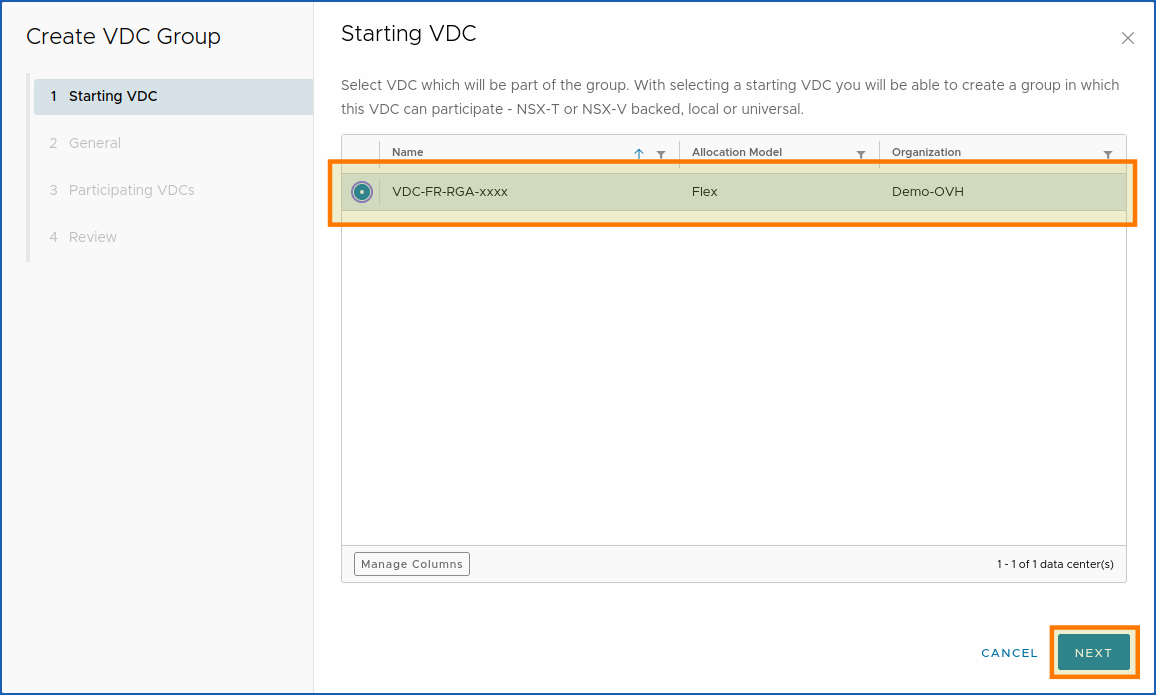
Select a vDC that will be part of the group. When you select a startup vDC, you can create a group in which this vDC can participate.
1. Choose the vDC you want, then click on NEXT.
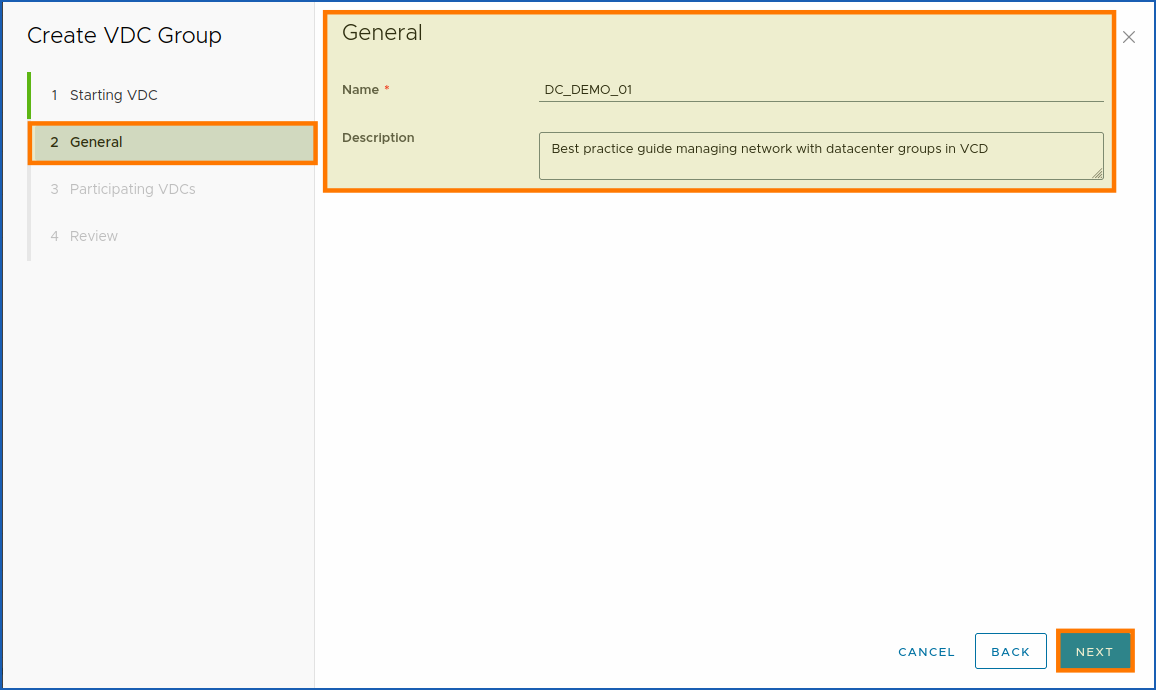
2. In section 2, choose the name of your datacentre group and a short description, then click on NEXT.
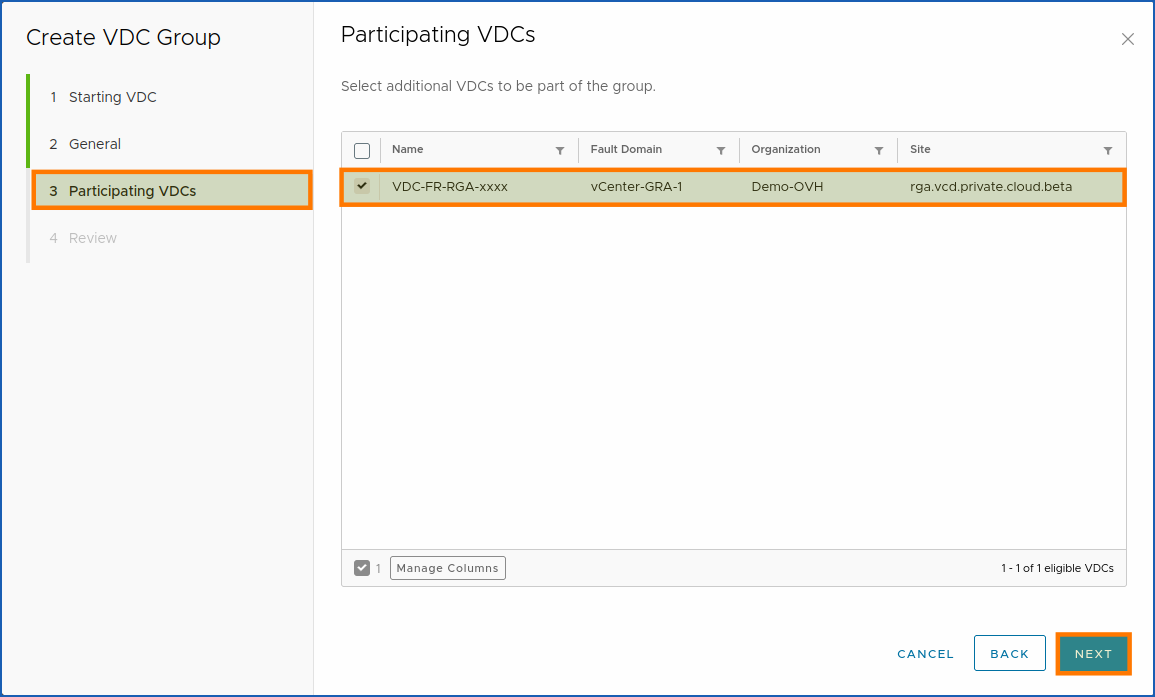
3. Next, select the additional vDCs that you want to be part of the group, then click on NEXT.
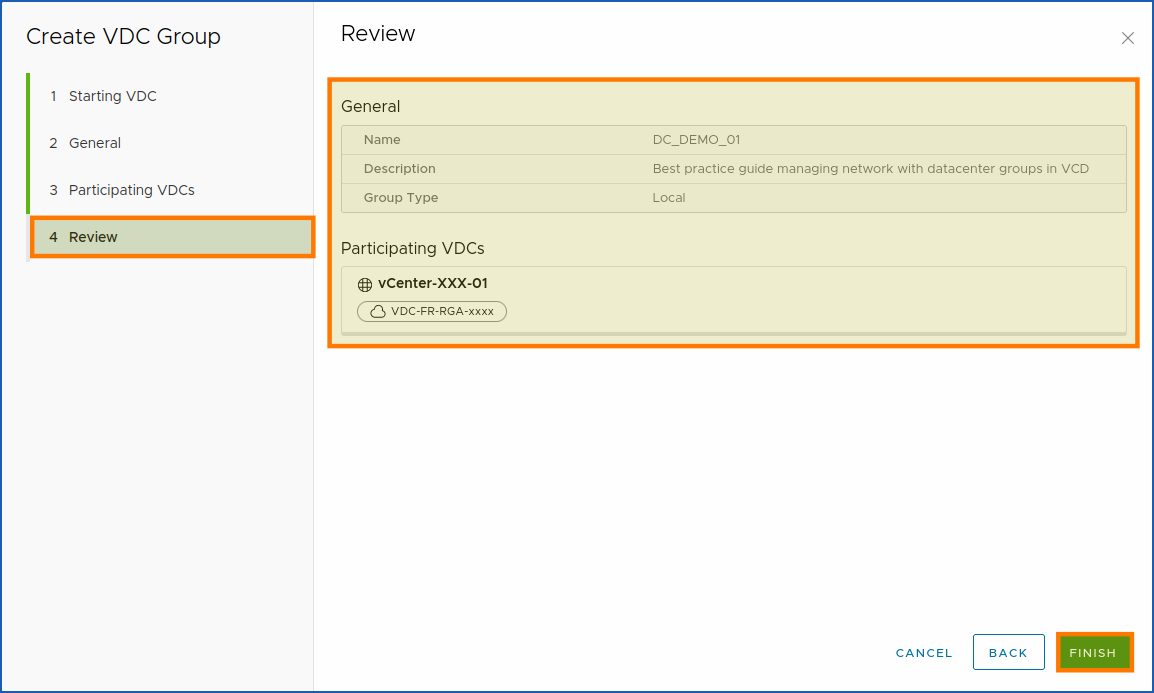
Finally, click on FINISH.
Step 3 - Create an Edge Gateway (optional)
How do I create an Edge Gateway with Public VCF as-a-Service?
This step is necessary, otherwise you will not be able to finish creating your network in step 3.
We will now create an Edge Gateway so that our IP space can be accessed via the private network, which we will create in the third subpart of this step.
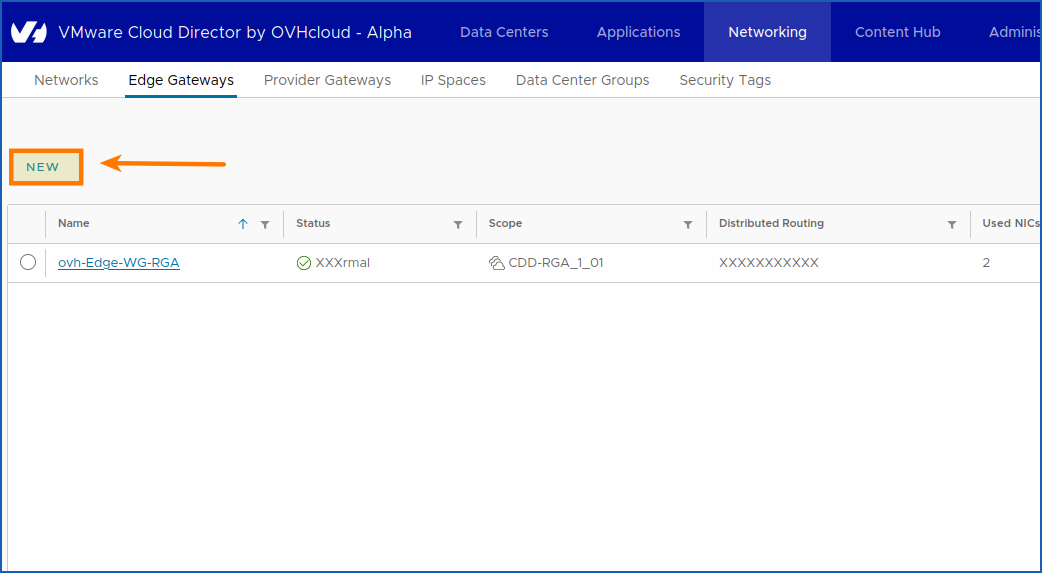
To access the Edge Gateways section, click on Networking > Edge Gateways.
To create a new Edge Gateway, click on NEW.
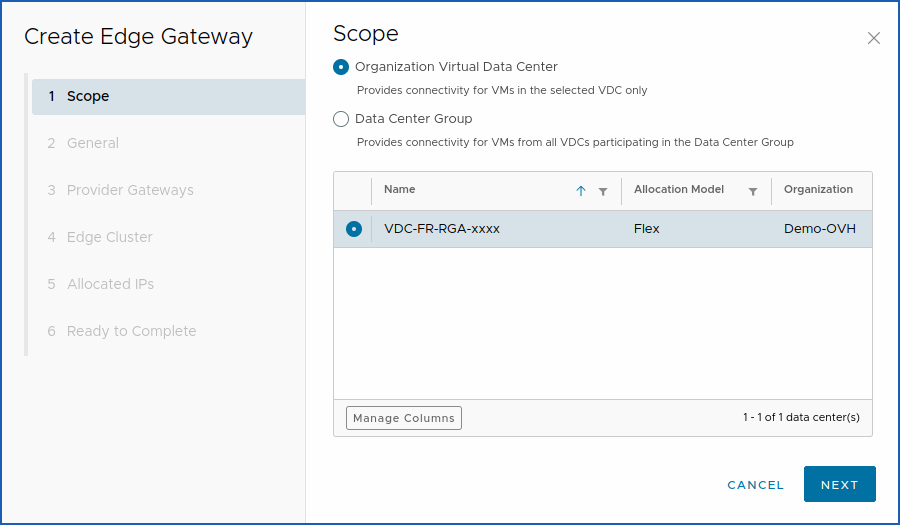
Here, you will see the window for creating an Edge Gateway for your Public VCF as-a-Service environment:
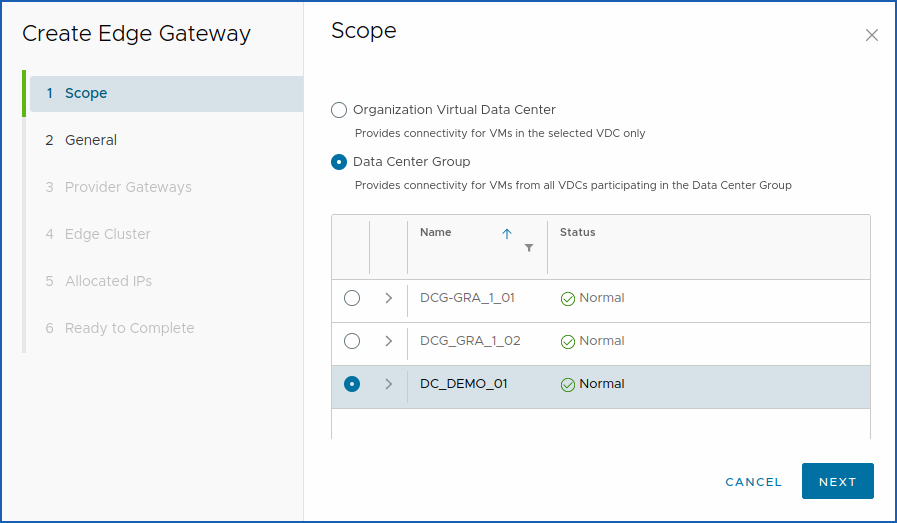
You can then choose between: Organization Virtual Data Center or Data Center Group.
- Organization Virtual Datacenter: Provides connectivity for VMs in the selected vDC only.
- Datacentre Group: Provides connectivity for the VMs of all virtual domain controllers participating in the datacentre group.
1. Choose Organization Virtual Data Center or Data Center Group to select the virtual datacentre with which you want to install your new Edge Gateway.
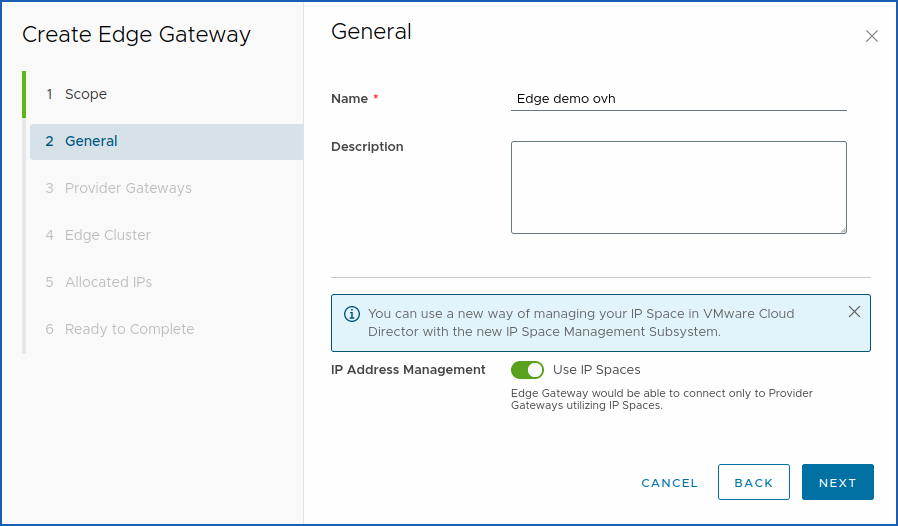
2. After the general section, you can name your edge gateway in any way you want:
Example:
- Name:
ovh-Edge-GW-GRA. - Description:
Edge Gateway private network dmz zone 1 (Graveline, Roubaix, etc..).
Next, click on Use IP Spaces.
This forces the use of IP spaces with the Provider gateways and optimize the application of new intelligent Public VCF as-a-Service network space management techniques.
When done, click on NEXT.
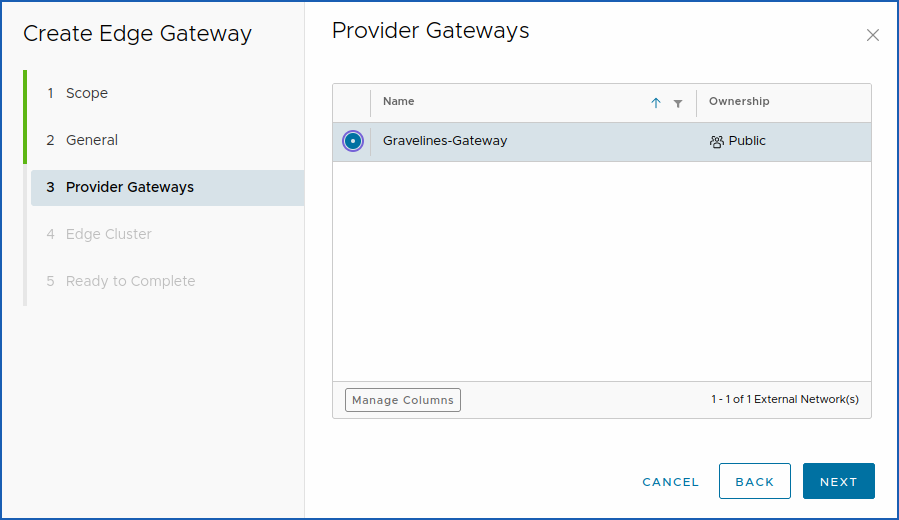
3. We will now move to sub-part 3 of the Edge gateway creation which is the choice of the Provider Gateways.
Choose the default gateway for your vDC provider: graveline-gateway.
Once you have chosen (step 3: Create an Edge Gateway), click NEXT.
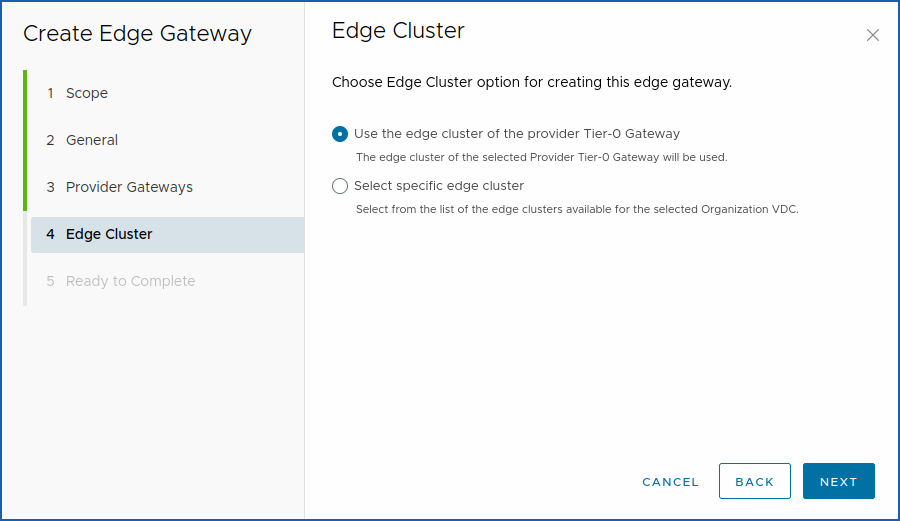
4. Choose the Edge Cluster option to create this provider Edge Gateway:
The parameter: Use the Tier-0 Gateway provider edge cluster means that the edge cluster of the selected Tier-0 provider gateway will be used in order to keep the shortest network path.
When you have chosen your settings (step 4), click on NEXT.
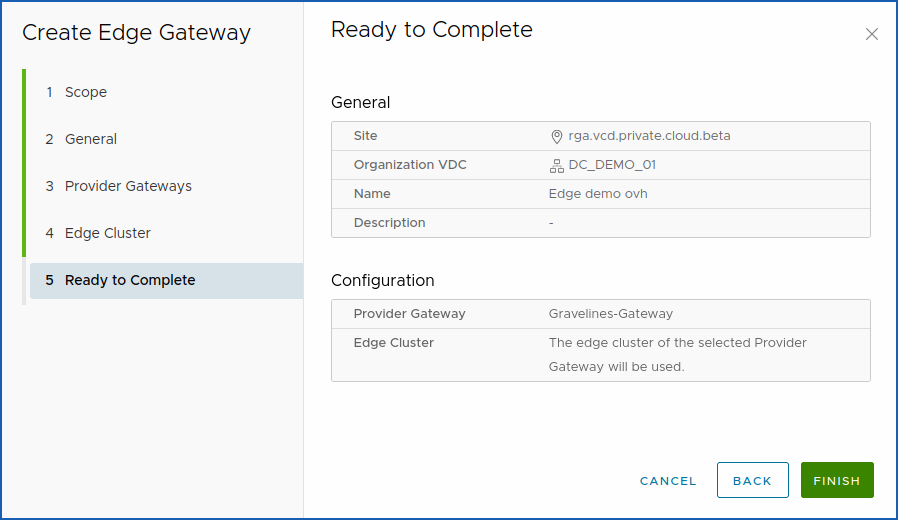
Once you have added the settings, you can check that everything is correct in section 5: Ready to Complete.
Finally, (step 5: Create an Edge Gateway) click on FINISH.
Step 4 - Create a private network
How do I create a network with Public VCF as-a-Service?
We will now create a new network and attach our preconfigured settings.
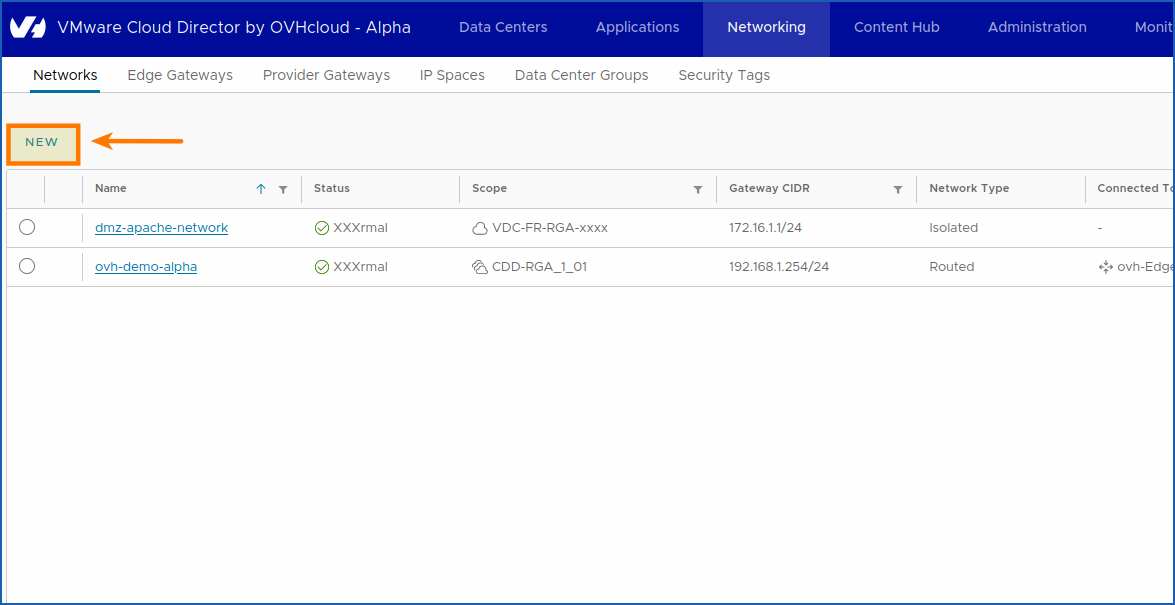
Go to the Networking section by clicking Networking > Networks.
Then click on NEW.
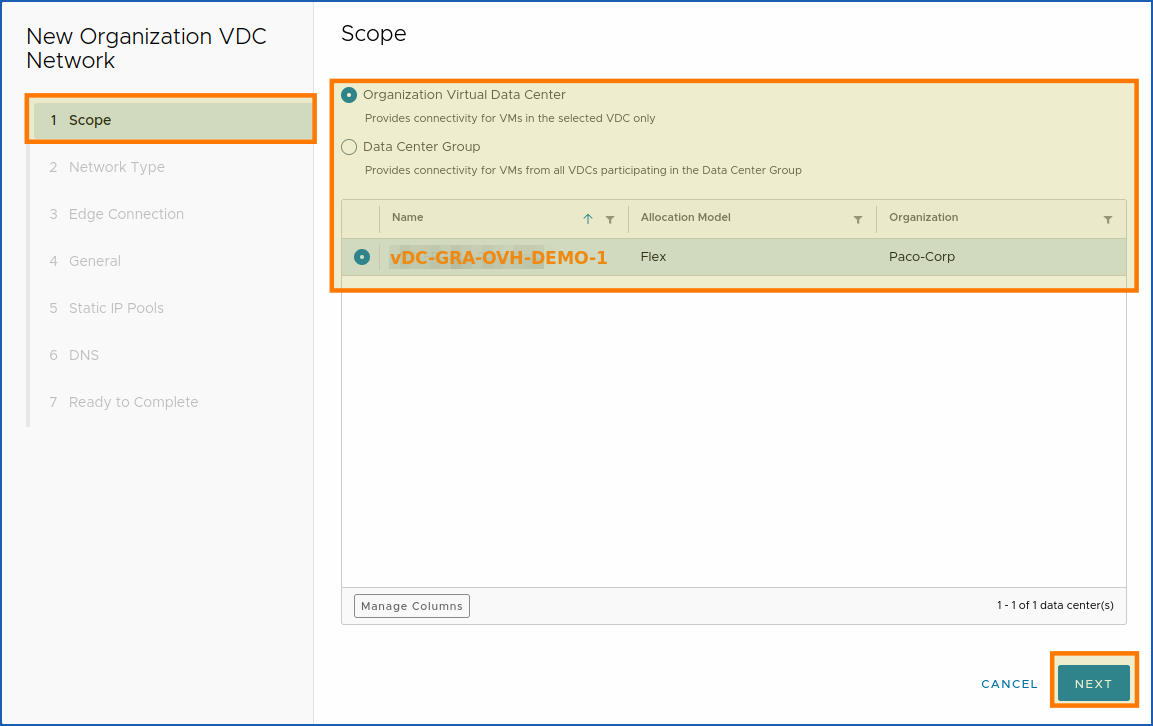
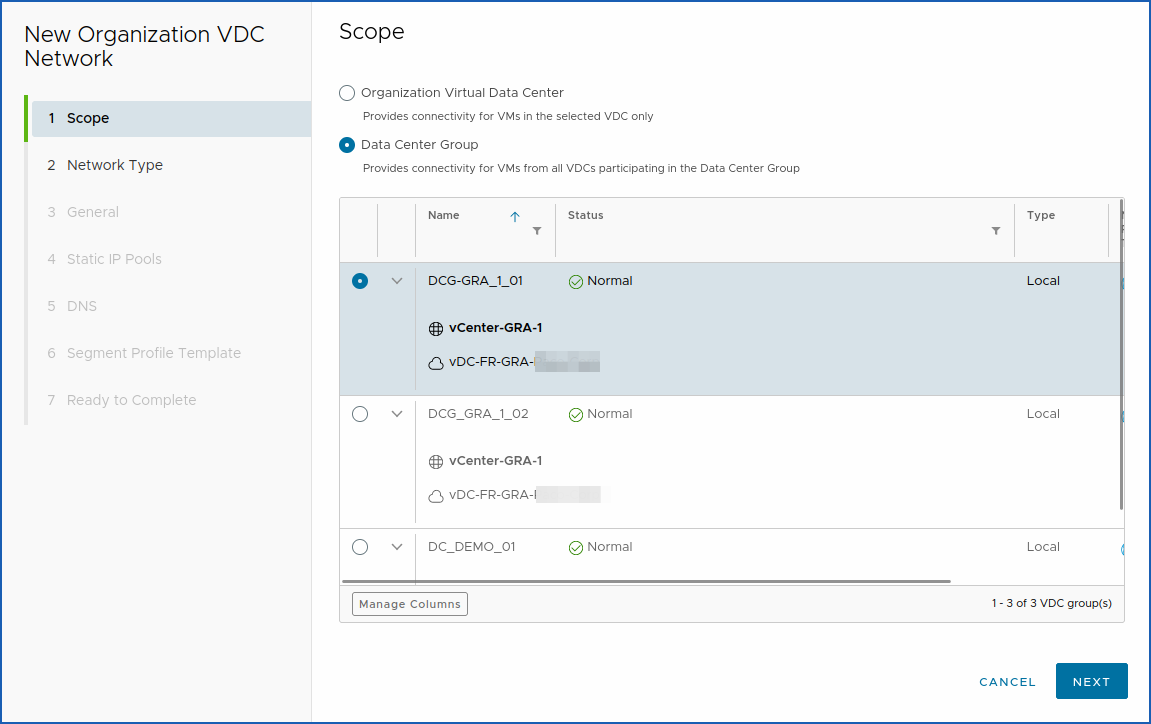
1. You will find this after the Scope 1 section.
You can choose between:
- Organization Virtual Datacenter: Provides connectivity for VMs in the selected vDC only.
- Datacentre Group: Provides connectivity for the VMs of all virtual domain controllers participating in the datacentre group.
Select the vDC Virtual Datacenter Organization or the Datacenter Group in the scope in which you want to create your network.
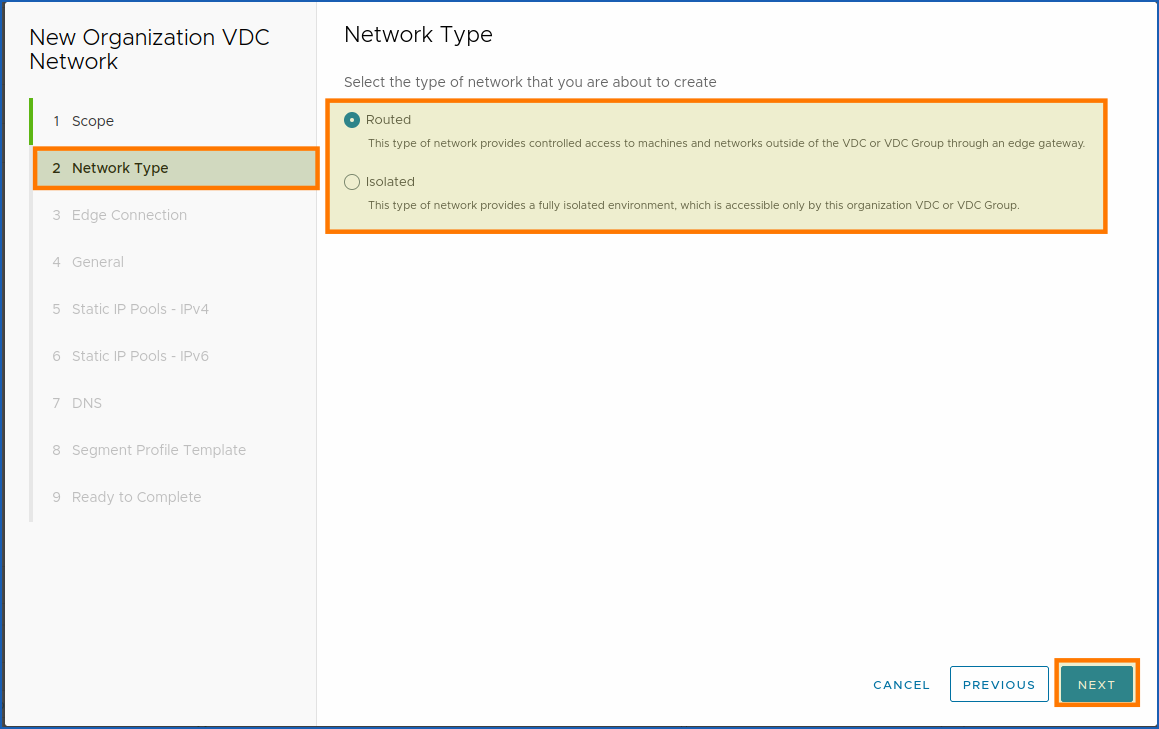
Next, select the type of network you want to create.
What choices are available?
You can create a routed or isolated Network type to suit your needs.
The "routed" allows incoming traffic, while the "isolated" forbids it.
Public VCF as-a-Servicedefinition:
- Routed: This type of network provides controlled access to machines and networks outside of the vDC or vDC group through an edge gateway.
- Isolated: This type of network provides a fully isolated environment, accessible only by this organization's vDC or vDC group.
For a routed network, if your VDC-FR/US/CA-GRA-XXX-XXX vDC does not have an Edge Gateway available, you will get this error:
The vDC “vDC-FR-GRA-XXXX-Corp” has no Edge Gateway available.
You can either create another "Edge Gateway", or use the "Datacenter Groups" available to provide connectivity for the VMs of all participating vDCs.
The Routed (through an "ovh-Edge-GW-GRA" Edge Gateway) type of network provides controlled access to machines and networks outside of the vDC or vDC group through an edge gateway.
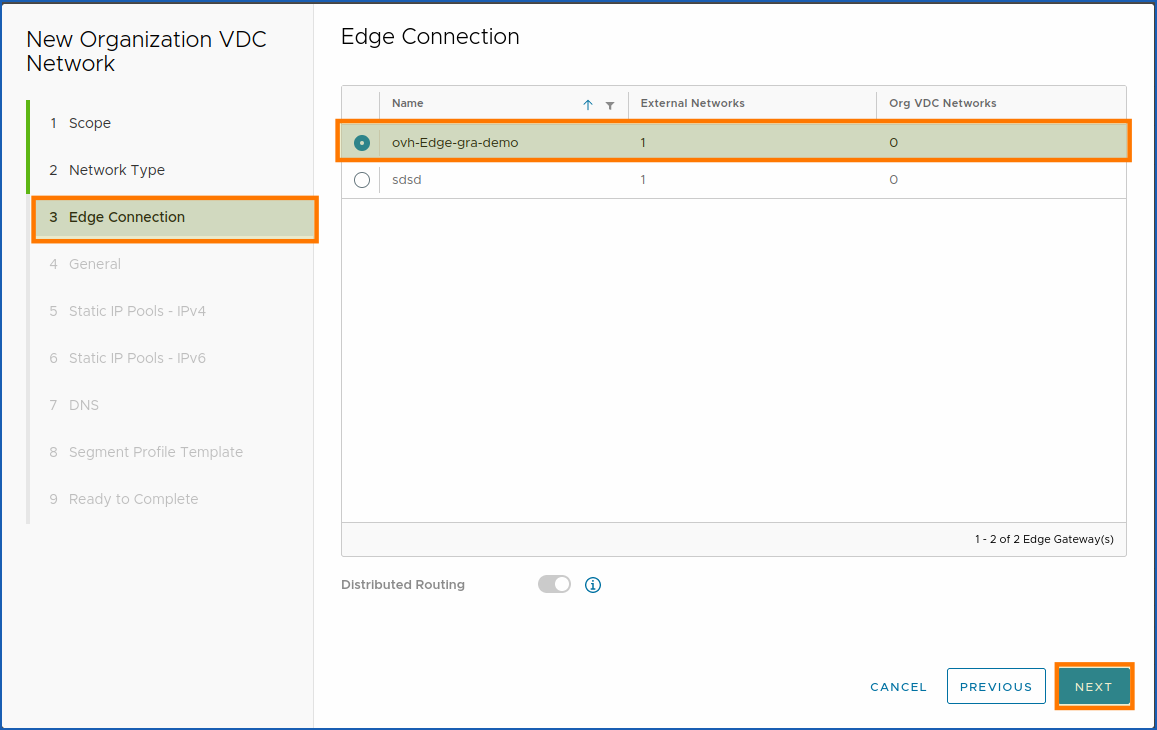
2. In the Edge Gateways section, you will see your previously created Edge gateway: ovh-Edge-gra-demo.
- Distributed Routing: Edge gateway must have non-distributed routing enabled.
This would disable distributed routing so that all VM traffic passes through the service router.
Choose your Edge Gateway by clicking on the available round button (white) to the left. Then, once finished, click NEXT.
To conclude, click on NEXT.
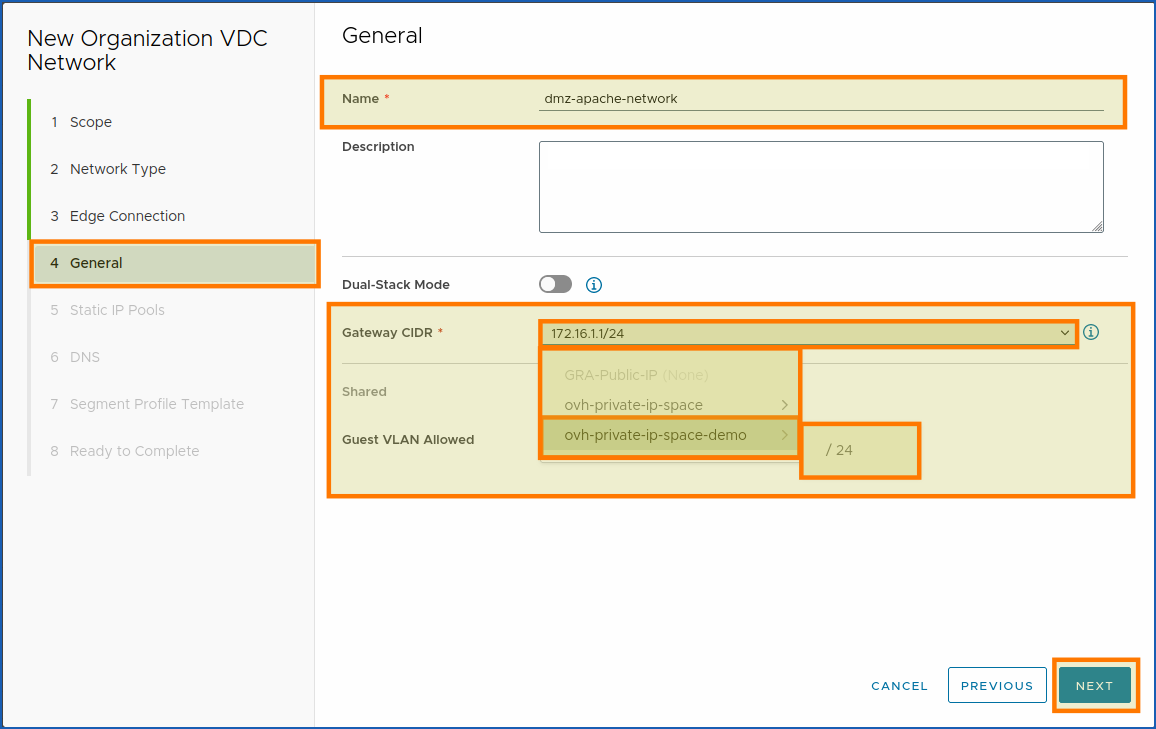
3. In the general section, you can add the name of your network, a description, and the IP space created earlier.
If it has been created, it will automatically appear in the list (see next screenshot: CIDR. Gateway*).
- Network:
ovh-private-ip-space-demo > /24.
Dual-Stack Mode: Enables the network to have one IPv4 subnet and one IPv6 subnet.
You cannot undo the activation of dual stack networking mode.
We don't need IPv6 at all, so we choose to leave this option disabled.
To continue (step 3: Create a private network), click on NEXT.
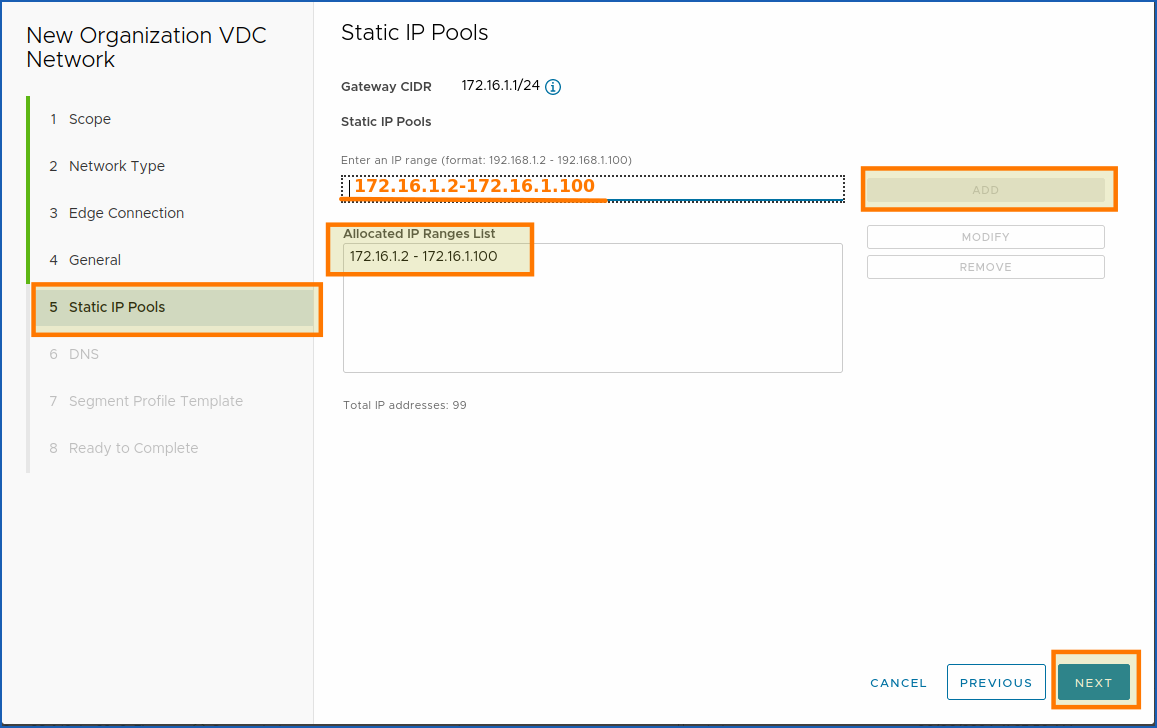
4. Here, you can allocate your network’s IP range. We choose to allocate 98 IPs:
172.16.1.2-172.16.1.100.
Once your IP range has been allocated, check that there is no space before and after the dash between the two IP ranges:
172.16.1.2**->-<-**172.16.1.100.
As well as at the beginning and end of your 2 IPs, ->172.16.1.2<- and ->172.16.1.100<-.
- Example:
172.16.1.2-172.16.1.100.
To continue, click on NEXT.
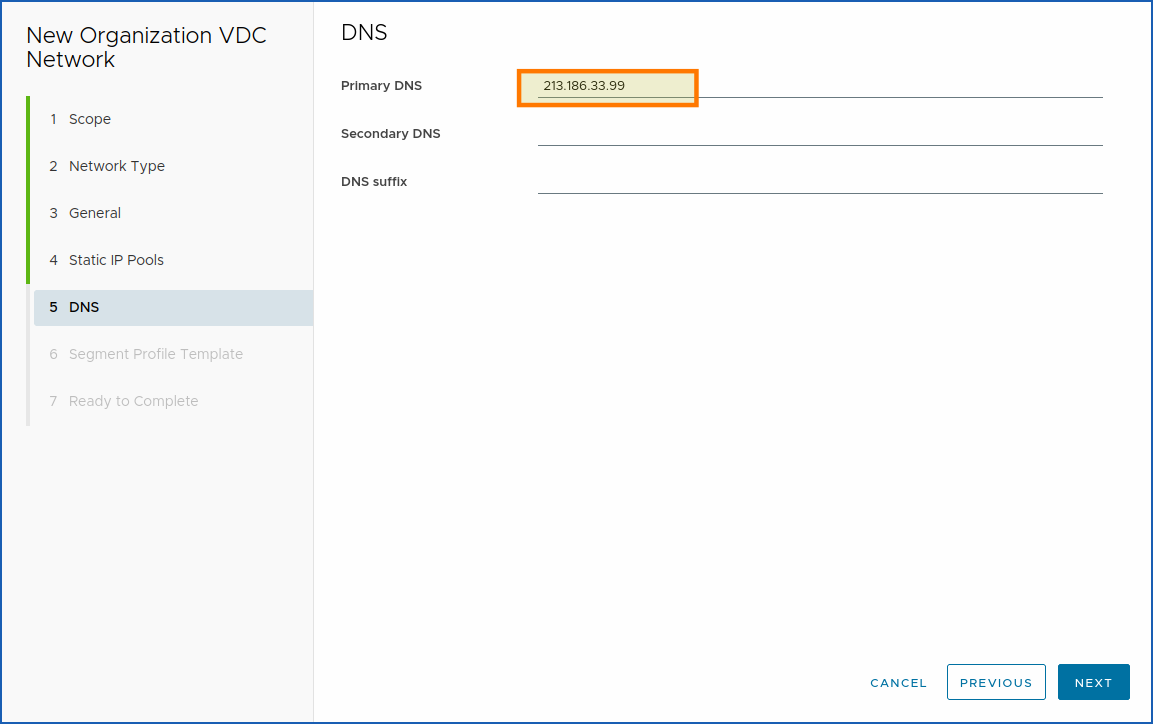
5. In the fifth section, add the DNS servers for your network.
For security reasons, we have decided to blur them here.
But you can leave those used by default in the Hosted Private Cloud VMware on OVHcloud universe:
| DNS | |
|---|---|
| Primary | 213,186,33,99 |
| Secondary | not used. |
| Suffix | not used. |
To continue with step 5 (creating a private network), click on NEXT.
6. (Optional) Segment profile templates can be defined here.
Segment profiles can be used for advanced networking use cases, such as enabling CARP protocol or Promiscuous mode in nested environments.
There are 3 available modes:
- Default (applied automatically)
- Allow-DHCP
- Promiscuous mode
These profiles are necessary in specific situations:
- MAC or IP learning for nested environments
- Custom security profiles to allow DHCP traffic
- Spoofing protection needs
To configure Promiscuous or Allow-DHCP mode:
- Go to
Networking>All Networks - Select the target network
- In the
Segment Profilessection, clickEdit - Choose the appropriate profile
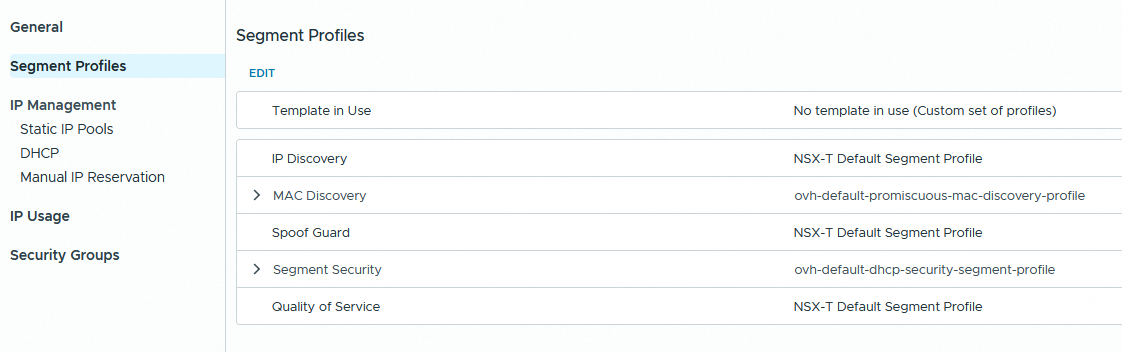
| Setting | Promiscuous mode | Allow-DHCP mode |
|---|---|---|
| IP address discovery | NSX-T Default Segment Profile | NSX-T Default Segment Profile |
| MAC Discovery | ovh-default-promiscuous-mac-discovery-profile | ovh-default-promiscuous-mac-discovery-profile |
| SpoofGuard | NSX-T Default Segment Profile | NSX-T Default Segment Profile |
| Quality of service | NSX-T Default Segment Profile | NSX-T Default Segment Profile |
| Segment Security | NSX-T Default Segment Profile | ovh-default-dhcp-security-segment-profile |
Promiscuous and DHCP profiles must be set manually after the network is created if required.
Do a final check of the settings, then click FINISH.
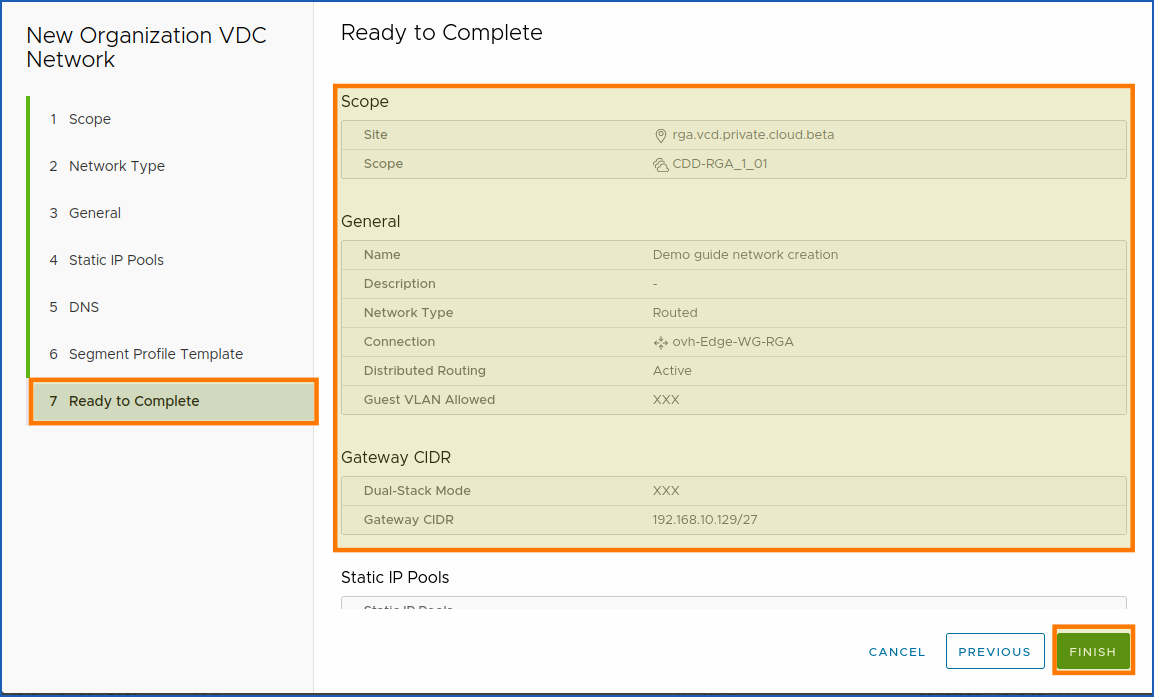
Your network is now fully created and ready to use.
Glossary:
CIDR: CIDR stands for Classless Inter-Domain Routing.
Go further
You can now follow the steps of the next guide :
- Coming soon: Guide 3 - Public VCF as-a-Service - Network - How to create an IPsec tunnel with Public VCF as-a-Service?
If you experience any network issues within Public VCF as-a-Service, please read our guide « Public VCF as-a-Service - Network - Concepts »
If you require training or technical assistance in implementing our solutions, contact your sales representative or click here for a quote and request a custom analysis of your project from our Professional Services team experts.
Ask questions, give your feedback and interact directly with the team building our Hosted Private Cloud services on the dedicated Discord channel.
Join our community of users.