Configuring a TERMINATED_HTTPS listener via CLI / Horizon
Objective
Our Public Cloud Load Balancer is based on OpenStack Octavia and is fully integrated into the Public Cloud universe.
After setting up your Load Balancer, you can configure it with a certificate in order to process HTTPS connections.
This tutorial explains how to configure a secure Public Cloud Load Balancer.
Requirements
- A Public Cloud project in your OVHcloud account
- Preparing your environment for using the OpenStack API
- OpenStack Octavia client and OpenStack Barbican set up
- A certificate from a third-party supplier
If you are not yet familiar with creating a Load Balancer, please follow our guide on Getting started with Load Balancer on Public Cloud before you continue with this tutorial.
Accesso allo Spazio Cliente OVHcloud
- Link diretto: Public Cloud Projects
- Percorso di navigazione:
Public Cloud> Seleziona il tuo project
Instructions
Attaching a Floating IP address to a Load Balancer
You can find the instructions for this part in this documentation in the section bearing the same name.
Preparing the certificate
For this stage, we need a certificate, which has already been generated.
When your certificate is generated by your supplier, you generally receive 2 or 3 files, described as follows:
- Main certificate (.crt or .pem file).
- Private key (.key file) generated during the CSR request.
- Intermediate certificate or complete chain (.crt file), if supplied. Some suppliers already include the intermediate chain in the main certificate, in which case you will only receive 2 files.
If you have obtained 3 files, you will need to merge the main certificate with the intermediate certificate to create a complete certificate. If your supplier already provides a complete certificate incorporating the intermediate chain, this merging step should be omitted.
You need to create a PKCS#12 package with your certificate inside:
You must download this file directly onto your computer in order to be able to send it to Openstack Barbican (‘Secret as a Service’).
Configuring your Load Balancer
Via Horizon
In the Horizon interface, open the Network section, then click Load Balancers
Select your Load Balancer by clicking on it.
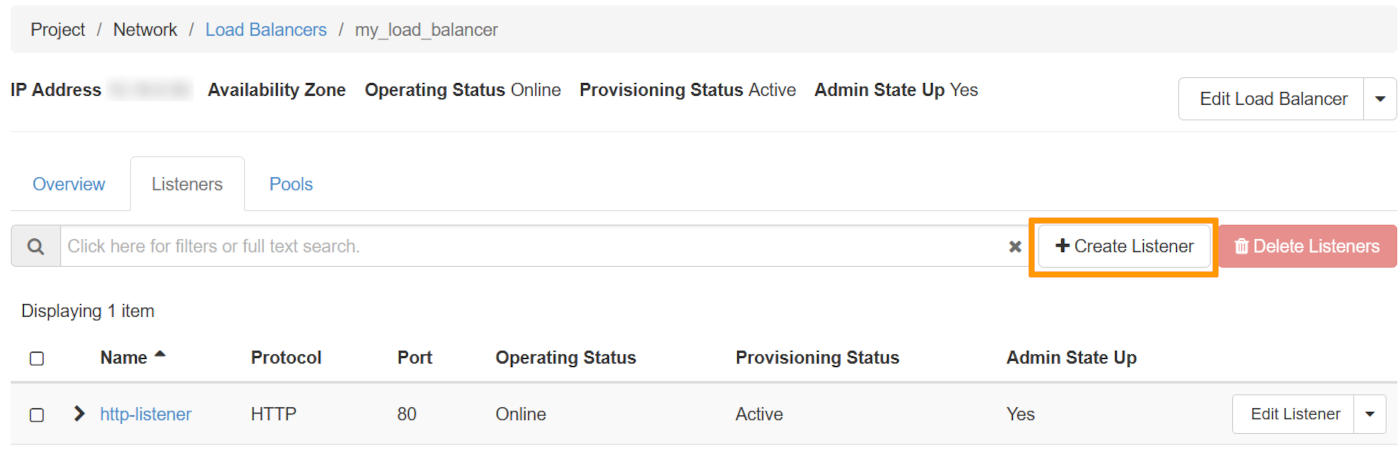
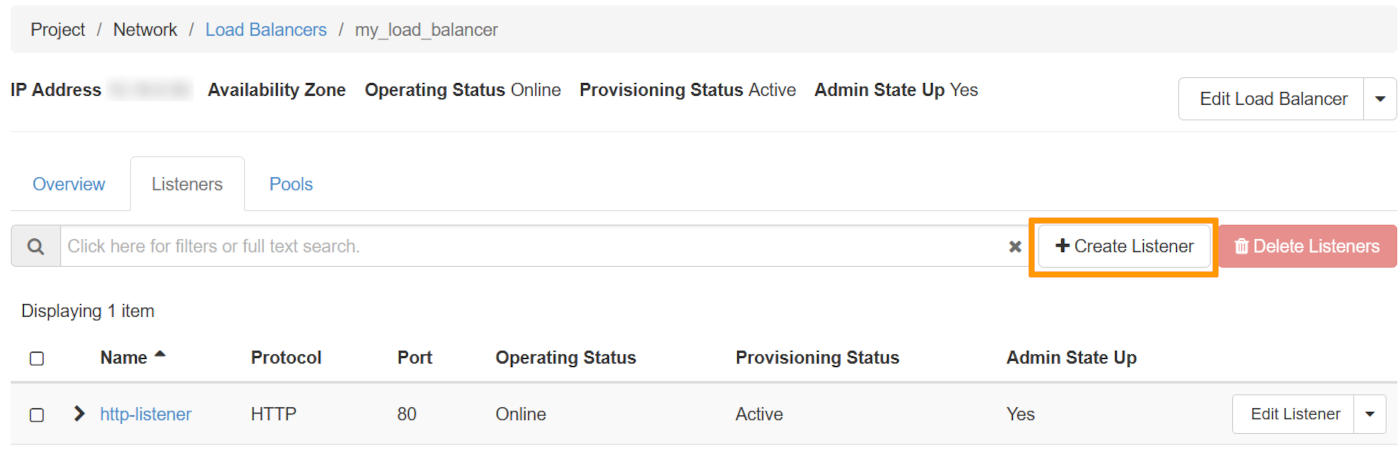
Next, click on the Listeners tab, then on Create Listener:
Listener Details
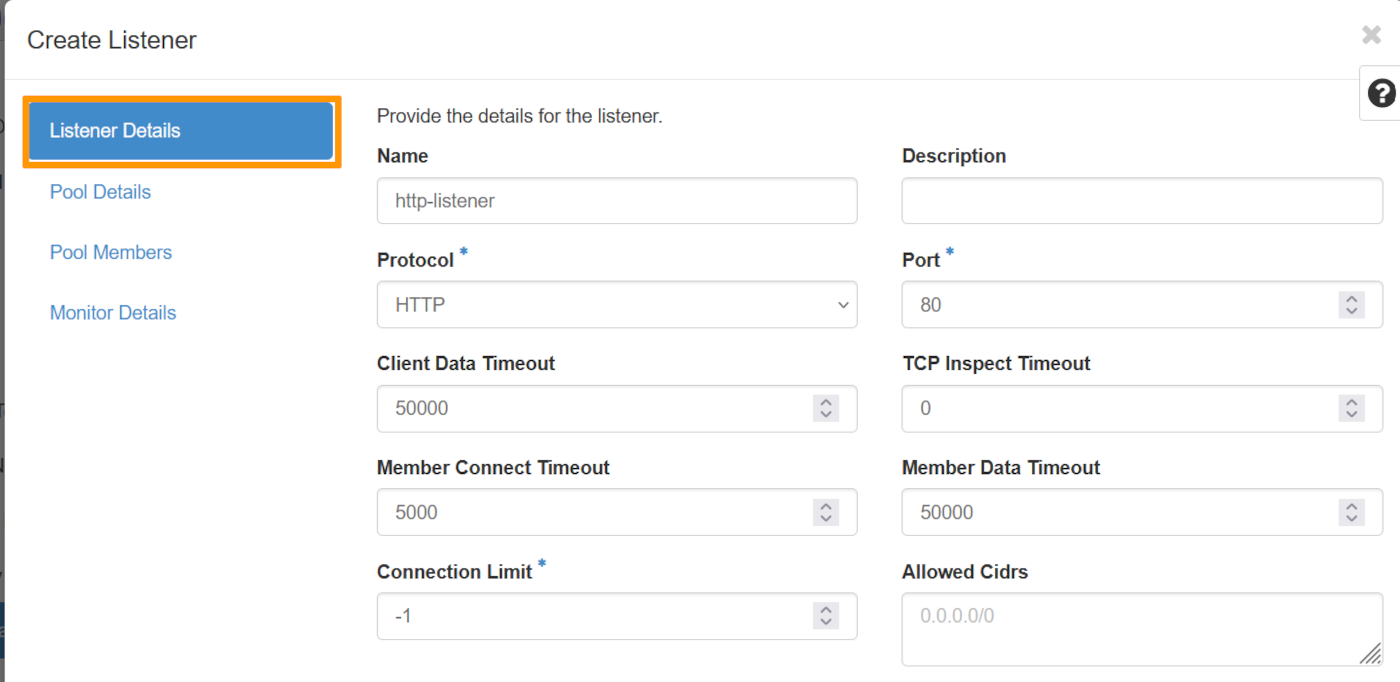
| Information | Details |
|---|---|
| Name | Specify a name for your listener. |
| Protocol | Select the HTTP protocol |
| Port | Select 80 |
Pool Details
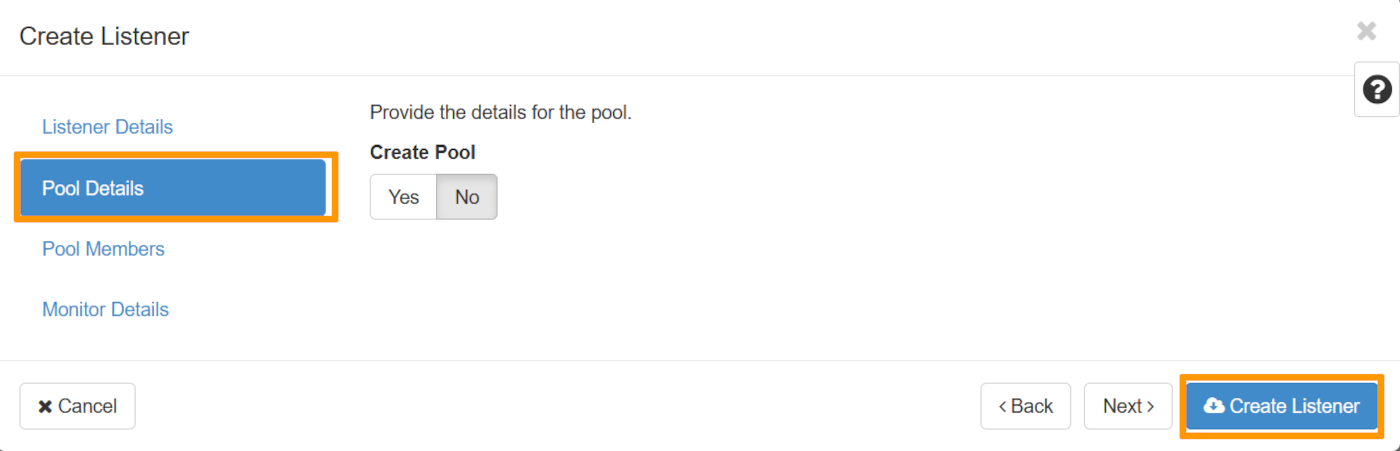
Under ‘Create Pool’, click No, then at the bottom, click on Create Listener.
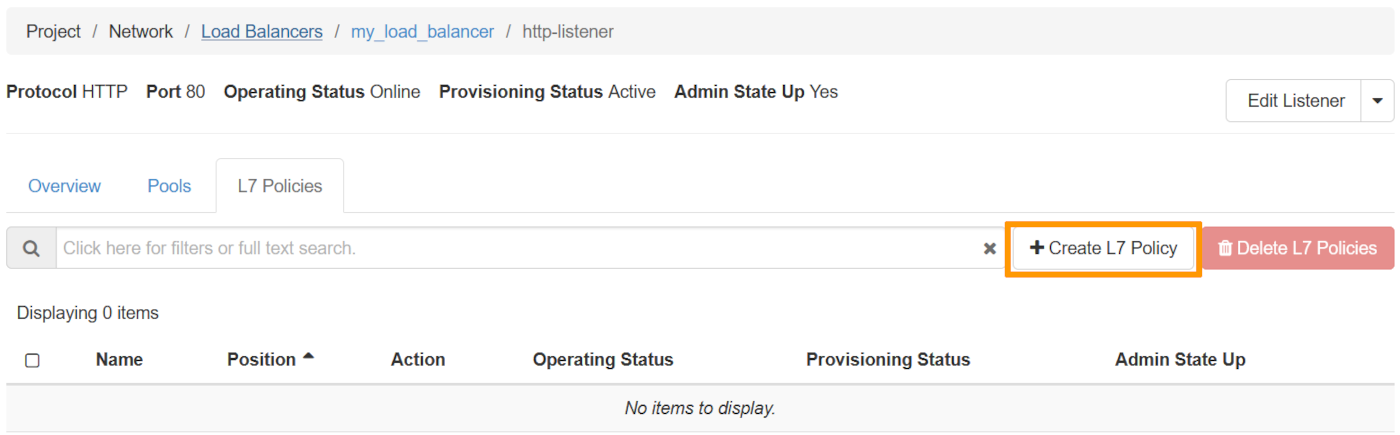
Once the listener has been created, click on it. Next, click on the L7 policies tab, then on Create L7 Policy.
L7 Policy Details
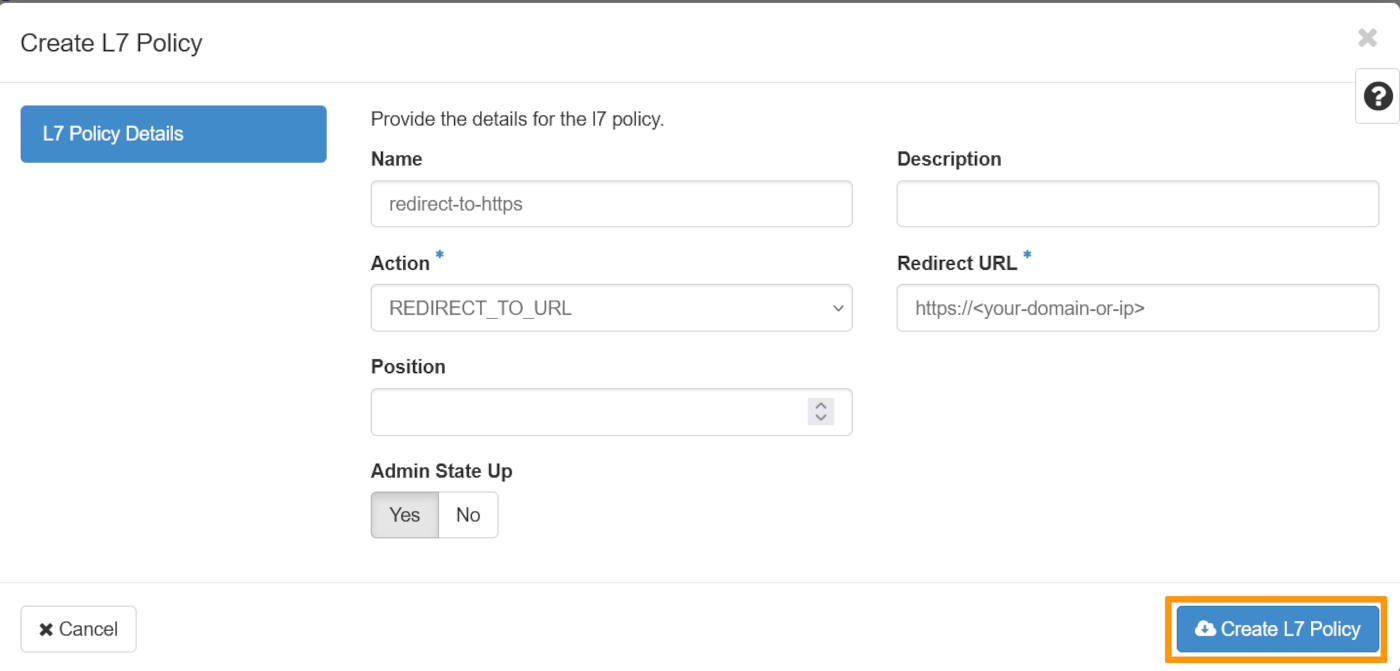
| Information | Details |
|---|---|
| Name | Specify a name for your L7 Policy |
| Action | choose the value REDIRECT_TO_URL |
| Redirect URL | Enter the domain name |
Once done, click on Create L7 policy.
Via the OpenStack API or via the OVHcloud Control Panel
To create a listener via the OpenStack API or via the OVHcloud Control Panel you can consult the relevant section in this guide, in the ‘Configuring your Load Balancer’ section.
Then configure the redirection of HTTP requests to HTTPS:
Configuring the secure Listener on the Load Balancer
Now that you have managed your certificate, you can add a secure Listener and associate a pool and its members with it:
Via Horizon
In the Horizon interface, open the Network section, then click on Load Balancers.
Select your Load Balancer by clicking on it.
You can now click on the Listeners section, then on Create Listener as follows:
Listener Details
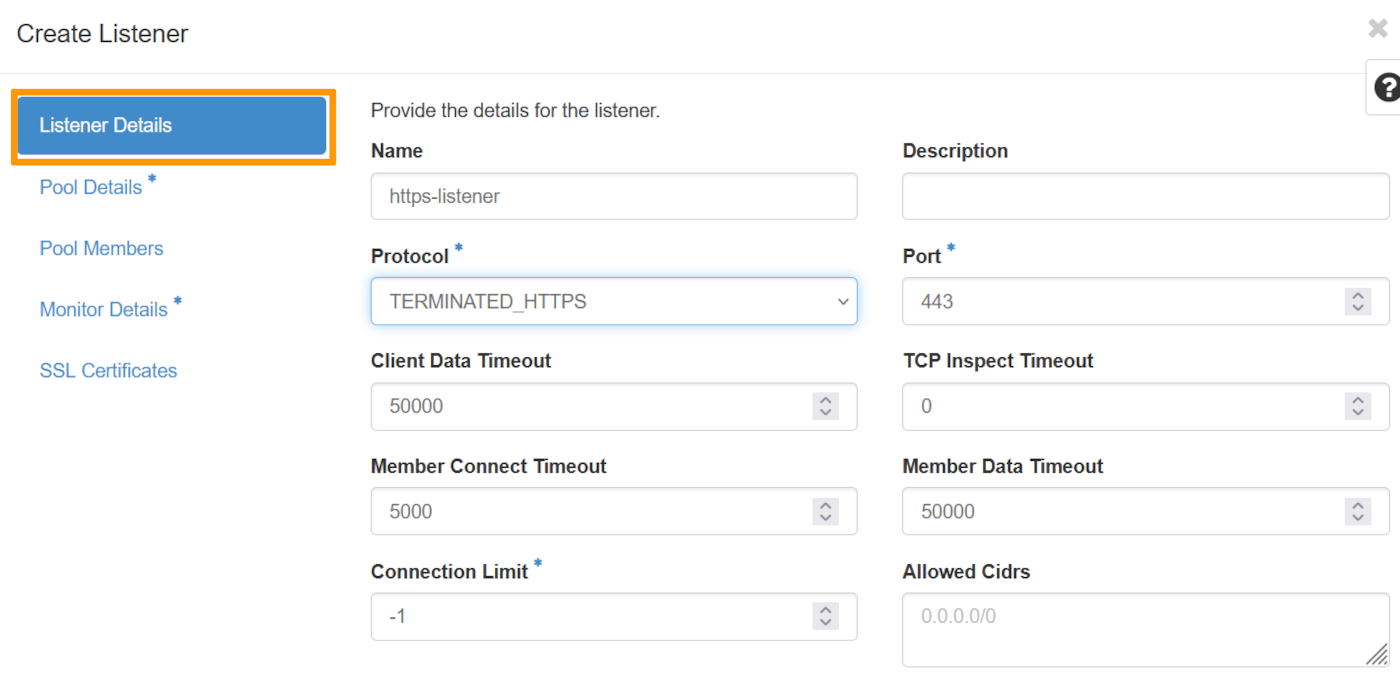
| Information | Details |
|---|---|
| Name | Specify a name for your listener. |
| Protocol | Select the TERMINATED_HTTPS protocol |
| Port | Select 443 |
Pool Details
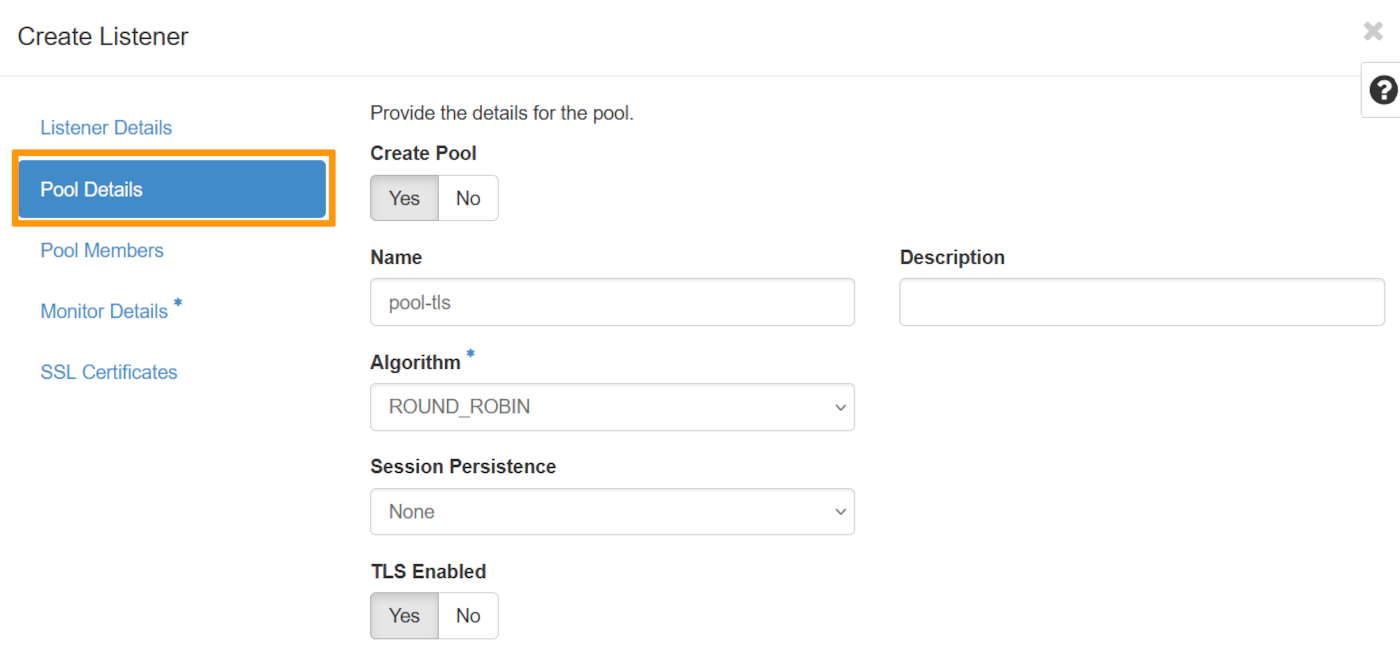
Under ‘Create Pool’ select Yes.
Choose a name for your Pool, in the ‘Algortihm’ field, choose the value ROUND_ROBIN and select Yes under ‘TLS Enabled’.
Pool Members
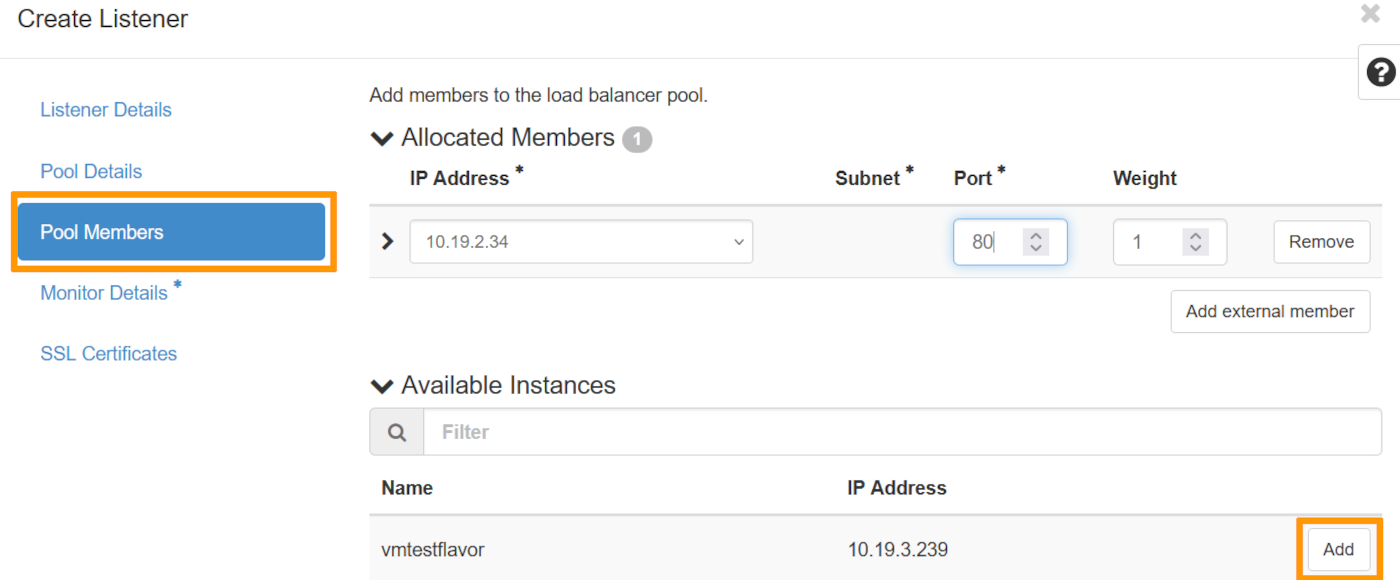
Select the corresponding instance and click on Add. Once this has been done, select port 80. as the ‘Port’.
Monitor Details
We're going to select No as we won't be demonstrating this part in this guide.
SSL Certificates
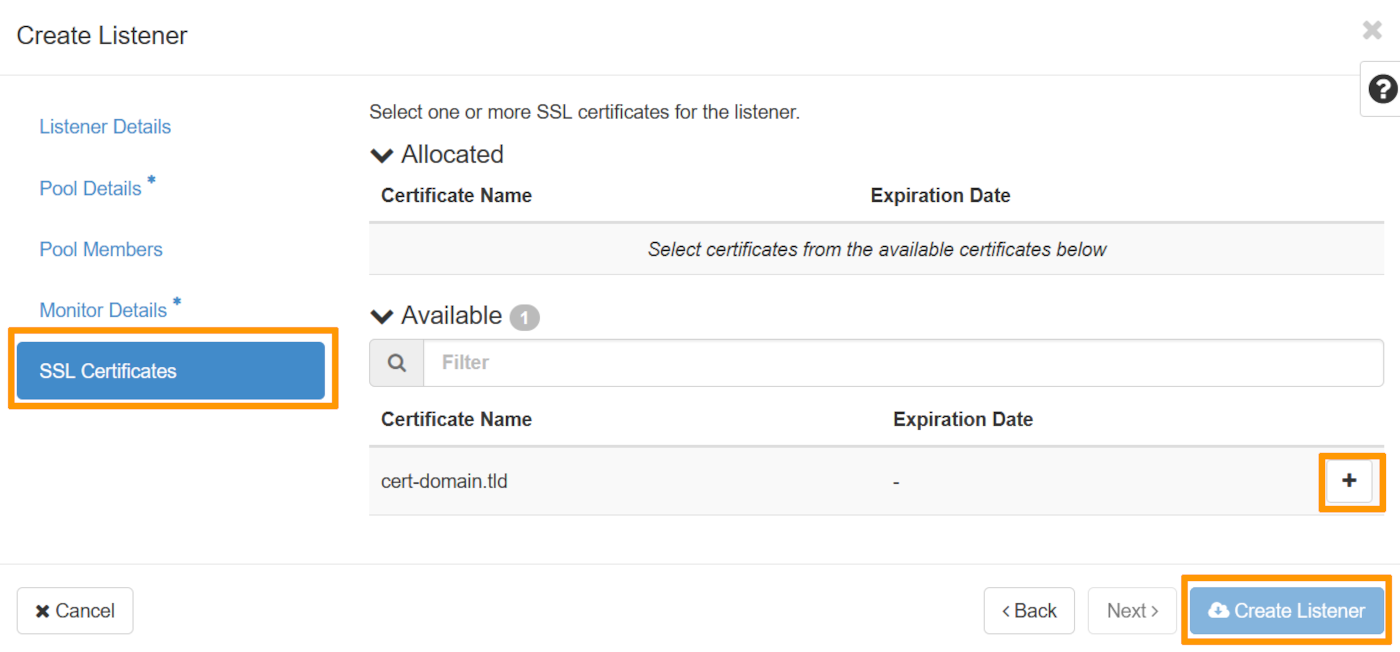
Select the certificate that was previously added to Openstack Barbican, in this section.
Once done, click on Create Listener to create your configured Load Balancer.
Via the OpenStack API
You can now access your Load Balancer securely. However, you will need to renew your certificate. Check the renewal policy with your certificate provider.
Go further
Official documentation of OpenStack Octavia
Getting started with Load Balancer on Public Cloud
If you need training or technical assistance to implement our solutions, contact your sales representative or click on this link to get a quote and ask our Professional Services experts for assisting you on your specific use case of your project.
Join our community of users.