KMS for VMware on OVHcloud - Configuring VM encryption
Objective
Find out how to order, activate and configure an OVHcloud KMS (OKMS) within a VMware vSphere managed on OVHcloud to enable the encryption policy for your virtual machines.
Requirements
- Access to the OVHcloud Control Panel.
- A Hosted Private Cloud VMware vSphere on OVHcloud offer.
- You must have the necessary rights to manage VMware HPC resources and OVHcloud KMS with IAM.
- You must have read the following guides:
- The KMS public certificate (OKMS) (see step vCenter Trust KMS).
- A certificate signature request (CSR) generated by vSphere and signed by OKMS to trust the exchanges between the OVHcloud KMS and vCenter.
Instructions
Summary of guide steps:
- Introduction - List of available URLs and OKMS API calls
- Step 1 - Ordering an OVHcloud KMS (mandatory)
- Step 2 - OVHcloud KMS activation (mandatory)
- Step 3 - Creating an IAM policy (mandatory)
- Step 4 - Configuring OKMS with vSphere (mandatory)
- Step 5 - Creating a VM storage policy (mandatory)
- Step 6 - Enabling encryption on a VM (mandatory)
- TLS OKMS useful information
Introduction, list of available URLs and OKMS API calls
For more information on the choices you can make with KMS and VMware on OVHcloud Hosted Private Cloud, please read our guide “Introduction to solutions for encrypting VMs”.
OKMS URLs
Information and API endpoints.
| Type | URL | Region | OKMS Enum Region | IP |
|---|---|---|---|---|
| Endpoint | eu-west-rbx.okms.ovh.net | France - Roubaix | EU_WEST_RBX | 91.134.128.102 |
| Swagger | swagger-eu-west-rbx.okms.ovh.net | France - Roubaix | EU_WEST_RBX | 91.134.128.102 |
| Endpoint | eu-west-sbg.okms.ovh.net | France - Strasbourg | EU_WEST_SBG | 137.74.127.152 |
| Swagger | swagger-eu-west-sbg.okms.ovh.net | France - Strasbourg | EU_WEST_SBG | 137.74.127.152 |
| Endpoint | ca-east-bhs.okms.ovh.net | North America - Beauharnois | CA_EAST_BHS | 142.44.140.50 |
| Swagger | swagger-ca-east-bhs.okms.ovh.net | North America - Beauharnois | CA_EAST_BHS | 142.44.140.50 |
| Endpoint | ca-east-tor.okms.ovh.net | North America - Toronto | CA_EAST_TOR | 72.251.10.6 |
| Swagger | swagger-ca-east-tor.okms.ovh.net | North America - Toronto | CA_EAST_TOR | 72.251.10.6 |
| Endpoint | ap-southeast-syd.okms.ovh.net | Asia Pacific - Sydney | AP_SOUTHEAST_SYD | 139.99.175.10 |
| Swagger | ap-southeast-syd.okms.ovh.net | Asia Pacific - Sydney | AP_SOUTHEAST_SYD | 139.99.175.10 |
| Endpoint | ap-southeast-sgp.ovh.net | Asia Pacific - Singapore | AP_SOUTHEAST_SGP | 51.79.192.115 51.79.192.94 |
| Swagger | swagger-ap-southeast-sgp.ovh.net | Asia Pacific - Singapore | AP_SOUTHEAST_SGP | 51.79.192.115 51.79.192.94 |
| Endpoint | eu-west-par.okms.ovh.net | France - Paris | EU_WEST_PAR | 57.130.4.16 57.130.4.25 57.130.4.26 |
| Swagger | swagger-eu-west-par.okms.ovh.net | France - Paris | EU_WEST_PAR | 57.130.4.16 57.130.4.25 57.130.4.26 |
List of API v1 and v2 KMS calls
Information and API calls.
| Method | API | Path | Comments |
|---|---|---|---|
| Credentials: | |||
| GET | v2 | /okms/resource/{okmsId}/credential | - List all access credentials. |
| POST | v2 | /okms/resource/{okmsId}/credential | - Request a new access credential. |
| GET | v2 | /okms/resource/{okmsId}/credential/{credentialId} | - Get an access credential. |
| DEL | v2 | /okms/resource/{okmsId}/credential/{credentialId} | - Revoke and delete an access credential. |
| Reference: | |||
| GET | v2 | /okms/reference/serviceKey | - Get service key type, size, curve and operations combination. |
| Resources: | |||
| GET | v2 | /okms/resource | - List OVHcloud KMS services. |
| GET | v2 | /okms/resource/{okmsId} | - Get an OVHcloud KMS service. |
| Service Keys: | |||
| GET | v2 | /okms/resource/{okmsId}/serviceKey | - List all keys. |
| POST | v2 | /okms/resource/{okmsId}/serviceKey | - Create or import a service key. |
| GET | v2 | /okms/resource/{okmsId}/serviceKey/{keyId} | - Retrieve a key. |
| PUT | v2 | /okms/resource/{okmsId}/serviceKey/{keyId} | - Update a service key. |
| DEL | v2 | /okms/resource/{okmsId}/serviceKey/{keyId} | - Delete the given service key. |
| Authentication: | |||
| GET | v1 | /dedicatedCloud/{serviceName}/vmEncryption/kms | - List virtual machine encryption KMS servers. |
| POST | v1 | /dedicatedCloud/{serviceName}/vmEncryption/kms | - Create virtual machine encryption KMS server. |
| GET | v1 | /dedicatedCloud/{serviceName}/vmEncryption/kms/{kmsId} | - Get virtual machine encryption KMS server. |
| DEL | v1 | /dedicatedCloud/{serviceName}/vmEncryption/kms/{kmsId} | - Remove virtual machine encryption KMS server. |
| POST | v1 | /dedicatedCloud/{serviceName}/vmEncryption/kms/{kmsId}/changeProperties | - Update virtual machine encryption KMS server. |
Step 1 - Ordering an OVHcloud KMS (mandatory)
How to order an OVHcloud KMS (OKMS) for HPC VMware on OVHcloud?
 .
.
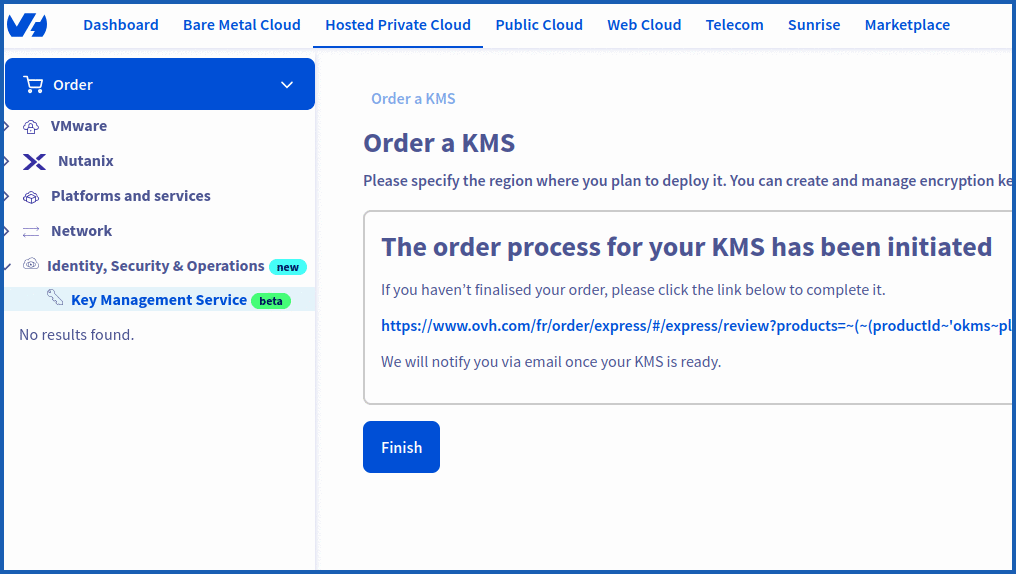
Via the OVHcloud Control Panel
To access the OVHcloud KMS, log in to your OVHcloud Control Panel, then go to the Hosted Private Cloud section. In the left-hand column, click Identity, Security & Operation, then Key Management Service.
To order a new KMS server, click the Order a KMS button, then Select a region.
The encryption keys and access certificates for this KMS will be stored in the specified region. They can be used for any OVHcloud product, regardless of region.
Once you have made your choice, click on the Order button.
Finally, click Finish to finalize the order.
Once your order has been confirmed, your KMS will contain the Name, the ID and the Region.
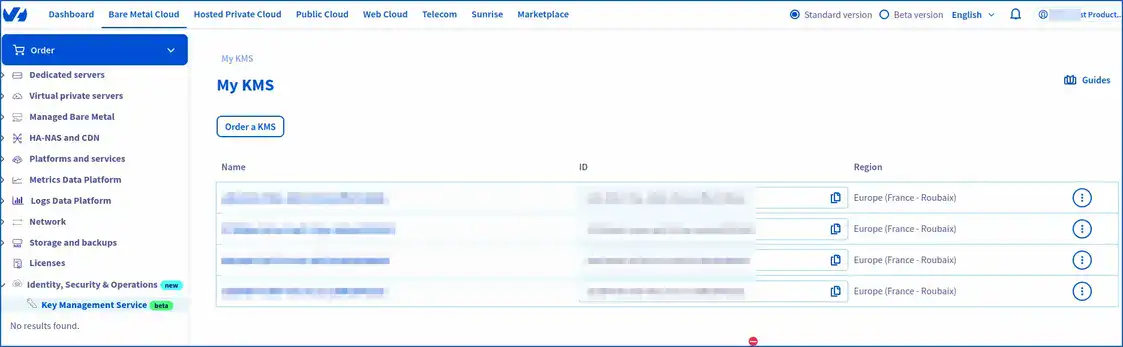
Copy your OKMS "ID".

The ID looks like a typical UUID. It will then be useful to:
- List your OVHcloud resources.
- List all access information (credentialId).
- Generate the "credentialId" with your CSR (the credentialId being the ID of the proof of signature of your CSR, your request for new access credentials).
- List all keys OKMS.
You can view the table above.
Settings:
okmsId: Your OVHcloud KMS ID (OKMS).
In step 3, we will look at how to carry out these requests.
Here is a global view of your KMS order for your OVHcloud VMware vSphere managed HPC environment.
You can copy and paste all the information needed to launch the API calls (IP, URN, KMIP etc...).
Via OVHcloud APIs
To list your OVHcloud KMS orders, use the following API call:
Settings:
okmsId: Your OVHcloud KMS ID (Okms).
Return example:
You now have an OVHcloud KMS server to set up within your managed VMware on OVHcloud environment.
Step 2 - Activate OVHcloud KMS (mandatory)
How to activate the OVHcloud KMS (OKMS) by opening traffic flows within your HPC vSphere managed on OVHcloud?
To validate the OVHcloud KMS (OKMS) with Hosted Private Cloud VMware on OVHcloud, create an inbound flow opening rule (firewall) within your VMware vSphere on OVHcloud HPC gateway.
This step must be completed immediately after you have ordered your KMS (OVHcloud) and before the KMS has been added to the managed VMware vSphere web interface.
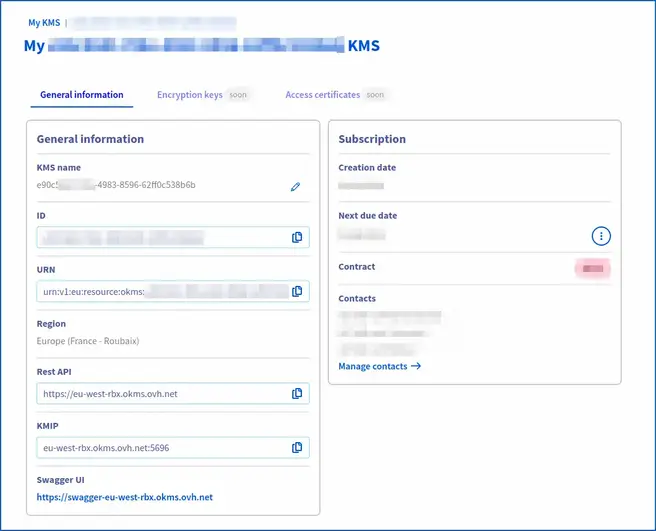
Via the OVHcloud Control Panel
Open feeds (required):
To create or import a KMS key management service, log in to your OVHcloud Control Panel, then go to the Hosted Private Cloud section. In the left-hand column, click on VMware, then select the service concerned. On the page that pops up, click on the Security tab.
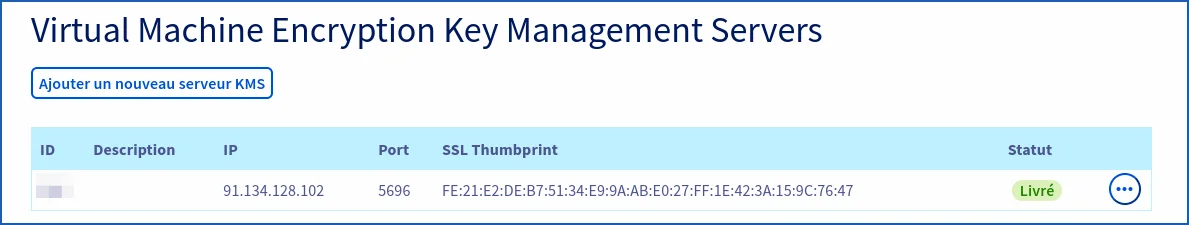
Then go further down in the Virtual Machine Encryption Key Management Servers section.
You will need to add your KMS via the control panel immediately after you have purchased and delivered your OVHcloud KMS. This is to allow flows within OVHcloud firewalls to be authorized.
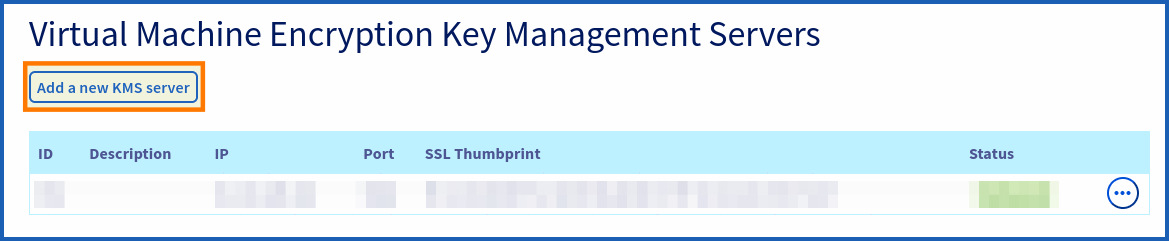
You can add your OKMS from the HPC control panel, by clicking Add a new KMS server
In the new window that pops up, fill out the following forms:
- IP: Please use the IP address, as the domain name cannot be added. For example, use the IP address
137.74.127.152for the region of Strasbourg and the IP address91.134.128.102for the region of Roubaix. - Description: Enter a description for your OKMS.
- SSL Thumbprint: Enter the SSL/TLS Thumbprint of your OKMS.
To retrieve the TLS fingerprint, launch the following OpenSSL command (adapt your OKMS endpoint to the right region (e.g. eu-west-rbx/sbg), which includes your OVHcloud KMS):
To retrieve the public IP of the OVHcloud KMS server, launch a ping. For example:
This is the IP of the Roubaix KMS and its TLS fingerprint. Adapt the command above to suit the region where your KMS is located (Strasbourg, for example).
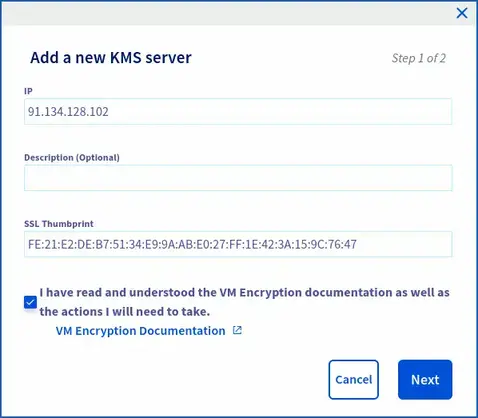
Please check that the following confirmation is ticked before you continue : "I have read and understood the VM Encryption documentation and the actions I will need to carry out on my own".
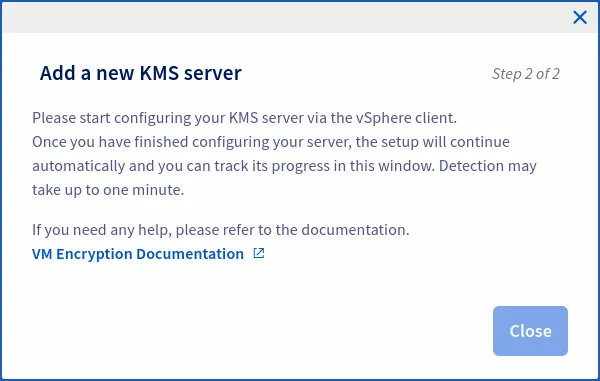
Wait for the streams to open and change the status to green delivered.
At the same time, check your rights within IAM. To use KMS, you will need additional rights.
To do this, go to the Users tab of your HPC managed vSphere. In the table that opens, click on the ... button to the right of the user concerned, then on Modify.
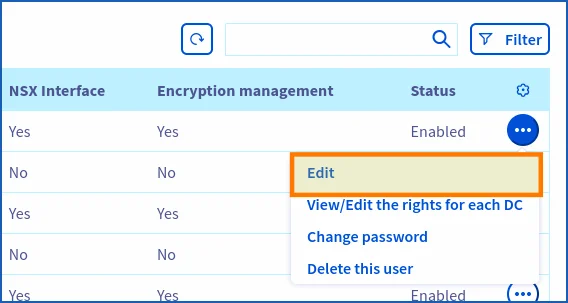
Verify that the Encryption management is enabled.
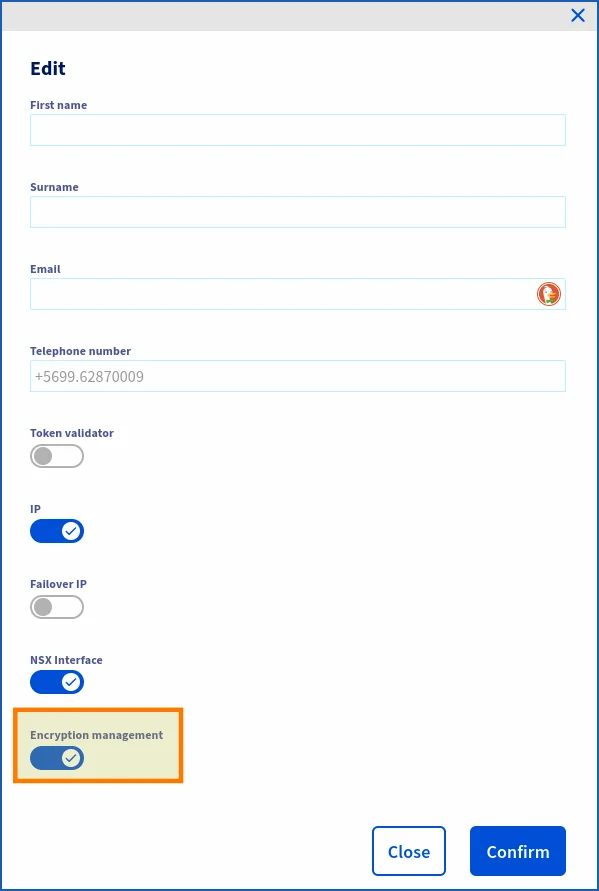
If you are using a particular IAM role with a global policy within your HPC managed vSphere, enable encryption management for that role. If this is the role created when IAM was enabled (iam-admin), the role has default encryption management.
With your policy, ensure that the users, resources, actions and product types of your HPC VMware vSphere managed on OVHcloud have been added.
IAM policy example:
- Identity: local user XX -> OVHcloud local user.
- User groups: ADMIN, XXXX-XX-XX/user_iam.
- Resources: pcc-XXX-XXX-XXX-XXX (reference for your managed vSphere).
- Product type: iam_ressources_type_okms/kmip.
- Actions: vSphere Admin, pccVMware:apiovh:vmEncryption/kms/changeProperties, pccVMware:vSphere:assumeRole?iam-admin -> User vSphere iam-admin, okms:kmip:get, okms:apikms:serviceKey/create etc..
For your information, the domain ID corresponds to the URN of your OVHcloud KMS.
Via OVHcloud APIs (optional)
If you have already opened the streams from the control panel, you can use the following API call (optional).
Opening flows step:
Settings:
serviceName: Enter the reference of your managed vSphere. Example: pcc-XX-XX-XX-XX.description: Enter the description of your OKMS.ip: Enter the public IP address of your OKMS.sslThumbprint: Enter the TLS fingerprint of your OKMS.
Copy and paste (with KMS settings):
To retrieve the public IP of the OVHcloud KMS, ping it by adapting the command to the region where your KMS is located:
To update your KMS with an OVHcloud KMS:
Settings:
kmsId: Enter the ID of your OKMS server. (Example: 350)serviceName: Enter the name of your managed vSphere. Example: pcc-XX-XX-XX-XX.
Example:
Return:
After running the API, you should see the following result in response:
Wait (status: updating) for the streams to open and for the status to change to the "delivered" state (optional).
Step 3 - Create an IAM policy
How do I create an IAM policy to enable VM encryption?
To enable encryption within vSphere, you must have sufficient rights within your KMS resources and OVHcloud account.
If you do not already have an IAM policy created, we will create one to list the necessary steps.
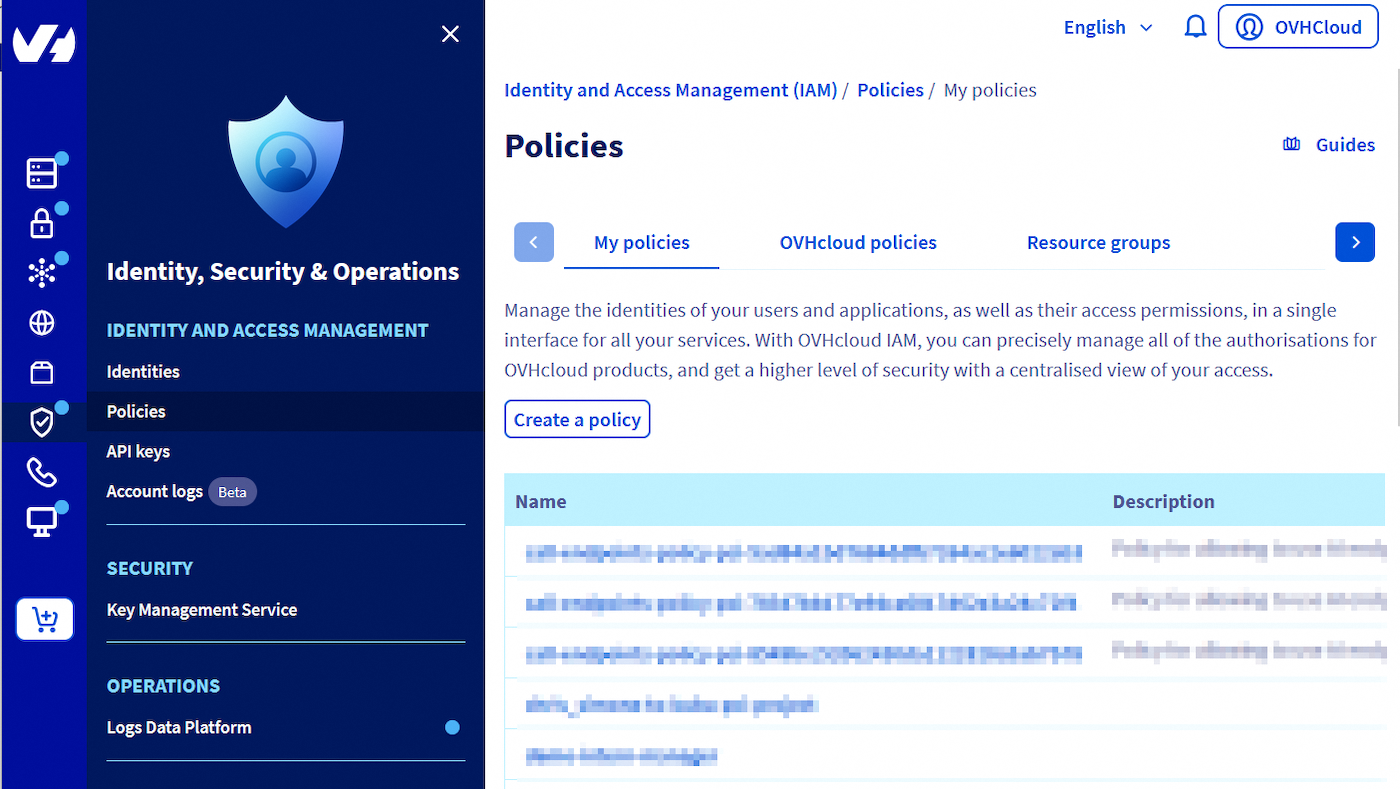
You will need to log in to your OVHcloud control panel.
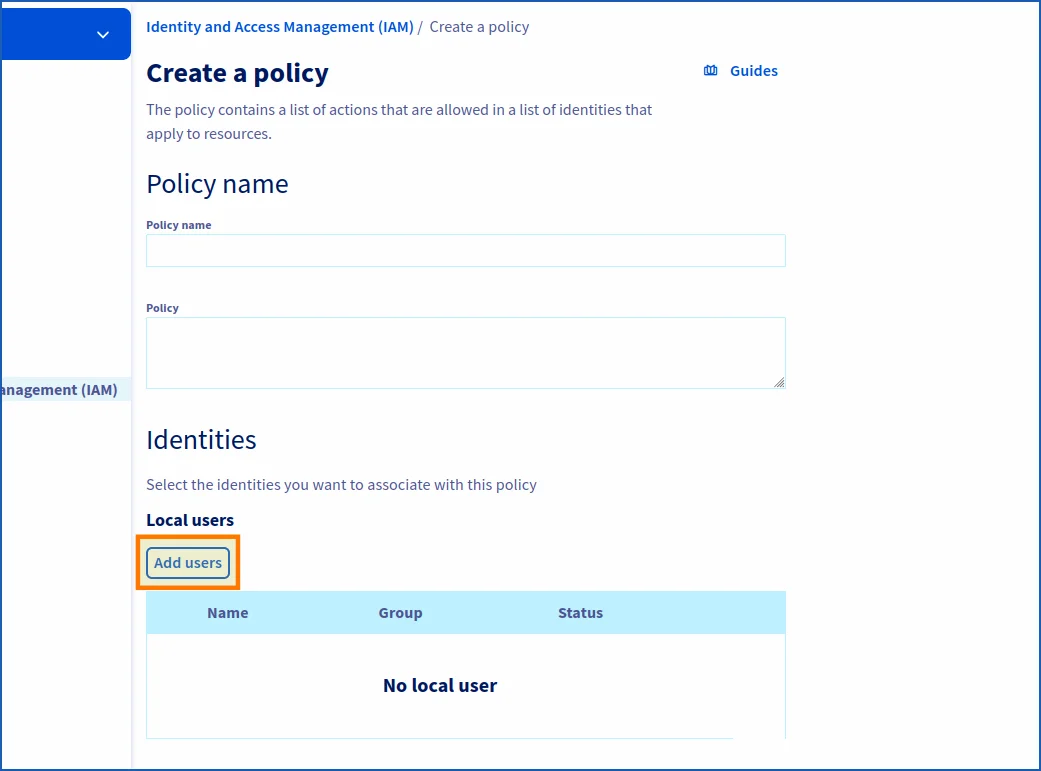
Go to Identity, Security & Operations section. Click Policies, then Create a policy.
Add the name of your policy, otherwise you will not be able to create it at the end.
And an intelligent description of your IAM strategy.
In Identities, add your local OVHcloud user (the one with which you generated the CSR from the API) by clicking Add a user.
You then need to add the actions in order to generate the keys for your vSphere encryption policy.
Click in the Product type field, then add Key Management System (KMS)
You can choose to add all actions or filter more finely according to your user needs.
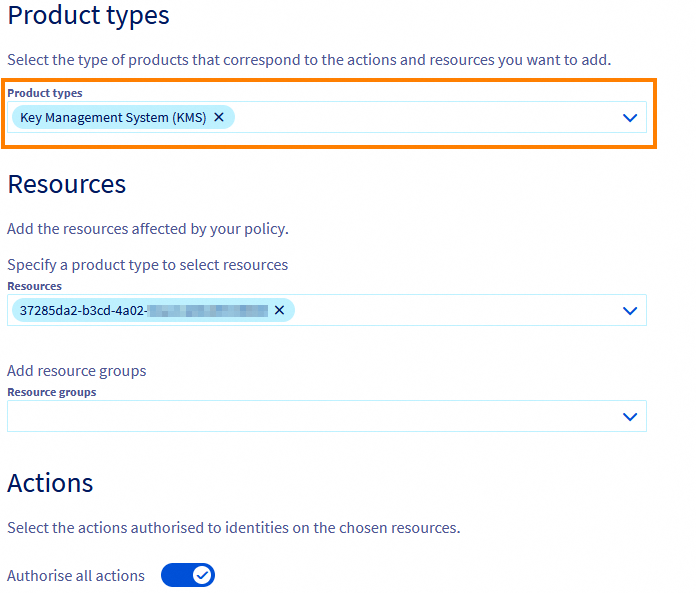
Finally, click Create policy.
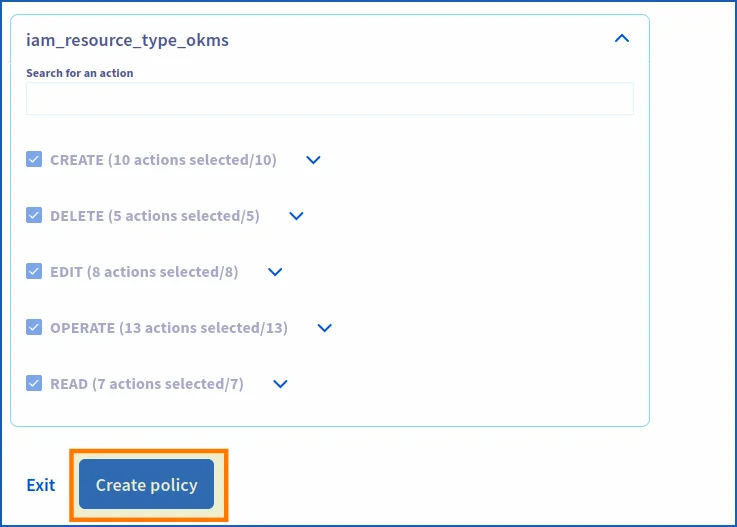
Your policy has been created. You can now enable encryption within PCC by changing the "VM strategy" of your virtual machines.
If you do not have a pre-established policy, explore the API control panel and determine the IAM actions required for the policy. If you already have an IAM policy, you can modify it and add the necessary actions.
Step 4 - Configuring OKMS with VMware vSphere HPC (mandatory)
How to add the OVHcloud KMS in your OVHcloud managed vSphere?
After ordering your OKMS, open the flows within your OVHcloud managed vSphere. All you need to do now is configure the import within vSphere and install the trust relationship between vCenter and OKMS.
To enable vCenter to test your OVHcloud KMS server, log in to your control panel, then go to the Hosted Private Cloud section. In the left-hand column, click VMware and select the datacentre concerned.
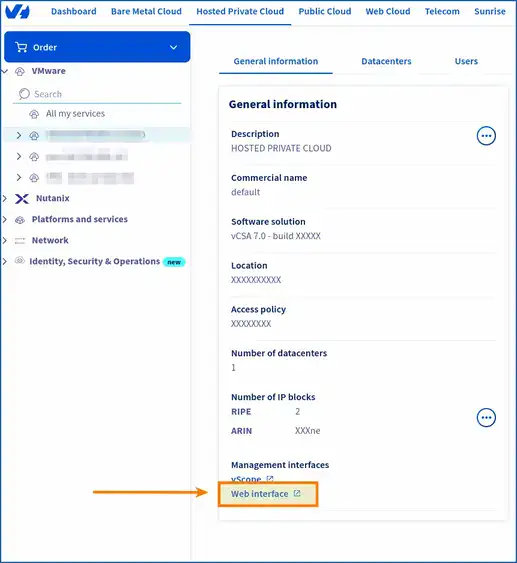
On the page that pops up, in the General information tab, scroll down to Management interfaces, then click Web interface.
On the new page that pops up, click on the square labeled vSphere HTML Client.
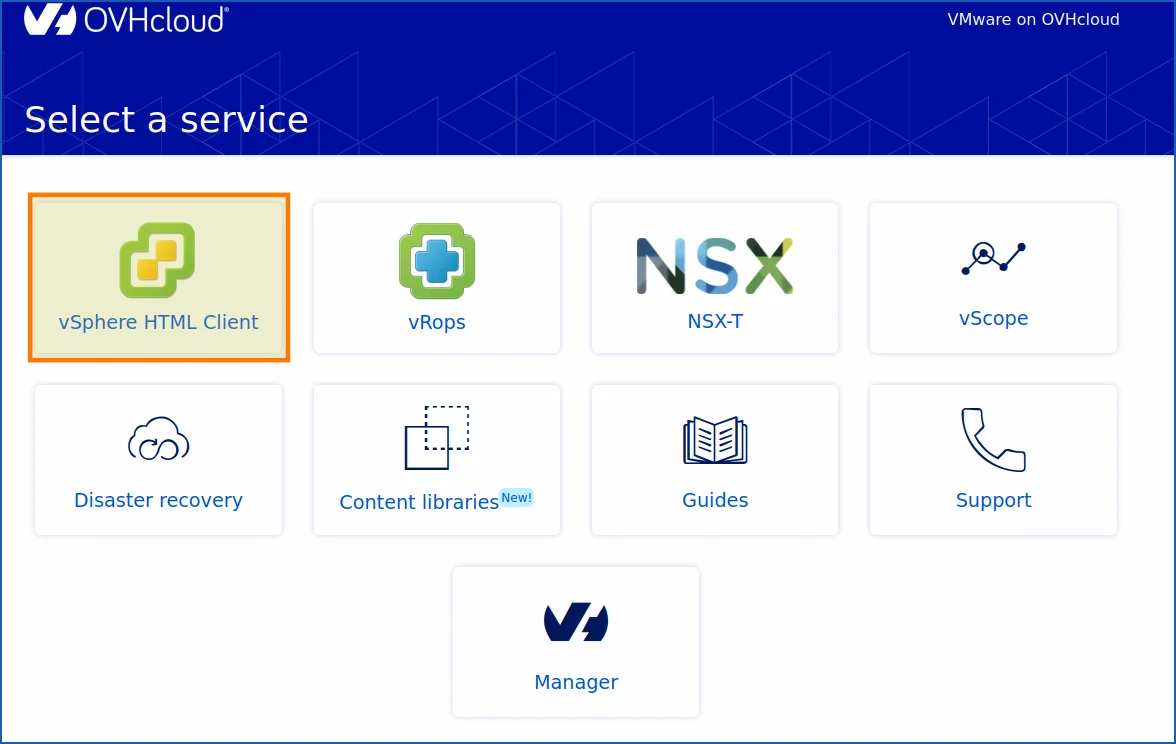
You are now on the login or home page of your managed vSphere. The URL at the top of your browser should look like this:
<https://pcc-x.x.x.x.ovh.de/ui/>
Log in with a local user or with an IAM user, depending on the permissions you have set up within your control panel and your HPC managed vSphere on OVHcloud.
You are now logged in to your managed vSphere on OVHcloud.
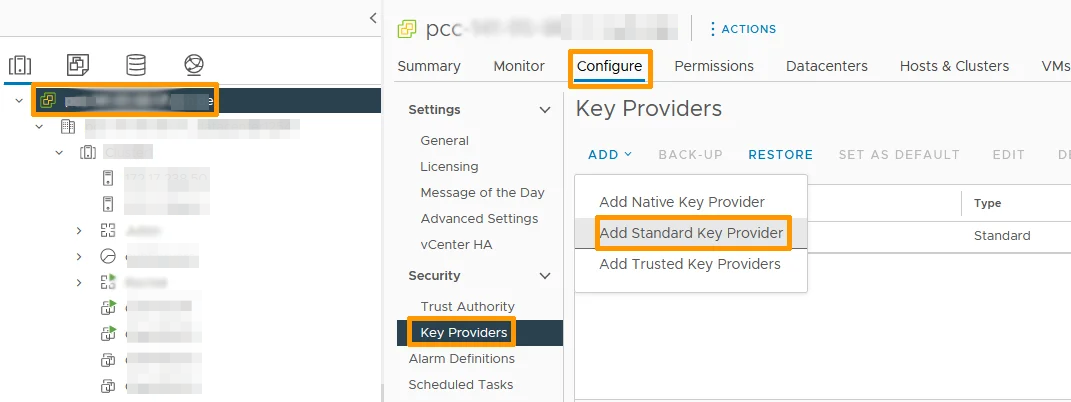
To access key provider management from vSphere, click Configure from your pcc-XXX-XXX-XXX-XXX. Go to the Security section, then click Key Providers. On the page that appears, click the Add button, then Add a standard key provider.
Once you have selected the option to add a Key Provider, a window or form will open to enter the details of the Key Provider you wish to add. This may include information such as the IP address or domain name (DNS) of the OKMS server, but also the port used (5697).
The domain names and the port (KMIP) do not change.
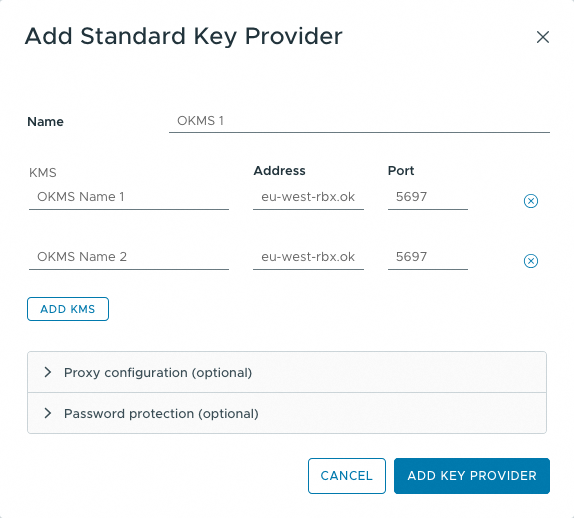
You will find the following fields:
| Field | Input | Description |
|---|---|---|
| Name | - Name your cluster within vCenter. | |
| KMS | - The name that will appear in vSphere for your OKMS. | |
| Address | eu-west-rbx.okms.ovh.net eu-west-sbg.okms.ovh.net | - Endpoint of the OKMS server. Choose a domain name over an IP (in vSphere). |
| Port | 5697 | - Port used by KMIP (does not change). |
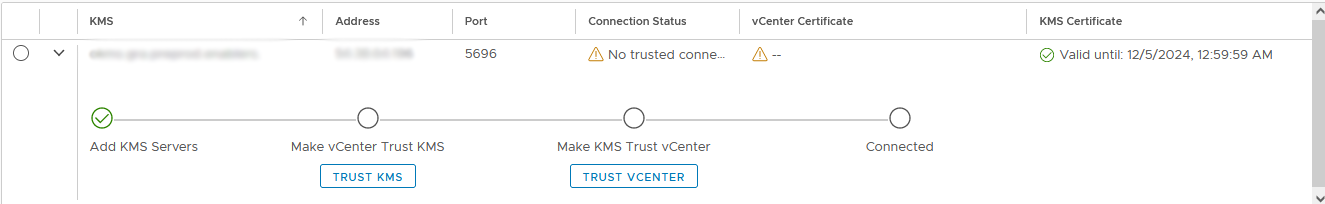
Wait for vSphere to establish the connection with the Key Provider you added. You should see a hint or message confirming that the connection has been successfully established.
Please wait for vSphere to establish a connection with the key provider you have just added. You should see a message confirming that the connection has been established successfully.
Trust between vCenter and KMS can be conflicting, please wait a few minutes before starting over, or refresh your vSphere page with the circular arrow button at the top and slightly to the right.
If it still doesn't work, do a manual upload (optional).
Before generating your CSR and/or KMS Certificate, and then your private key, you must ensure that vCenter has downloaded the public certificate from the OVHcloud KMS server. Once your KMS has been imported into vSphere, you will need to validate the trust relationship between each element.
Once you have added your KMS, add it by default (if you have multiple key providers). If not it will be added automatically.
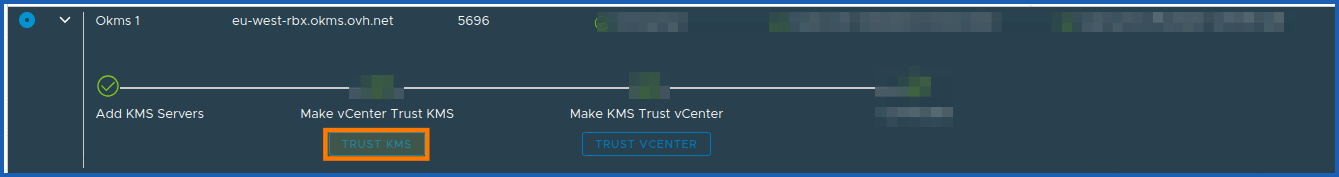
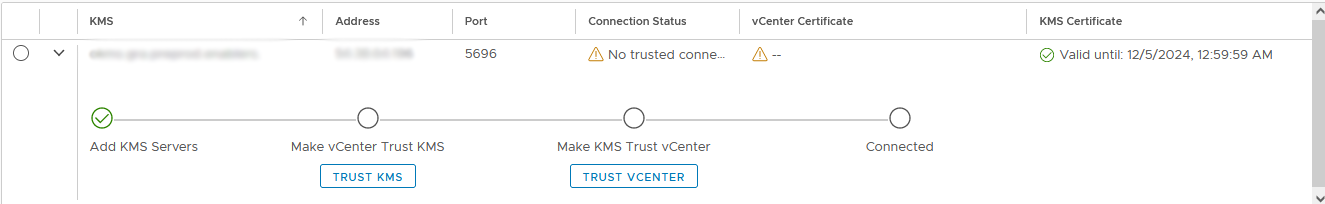
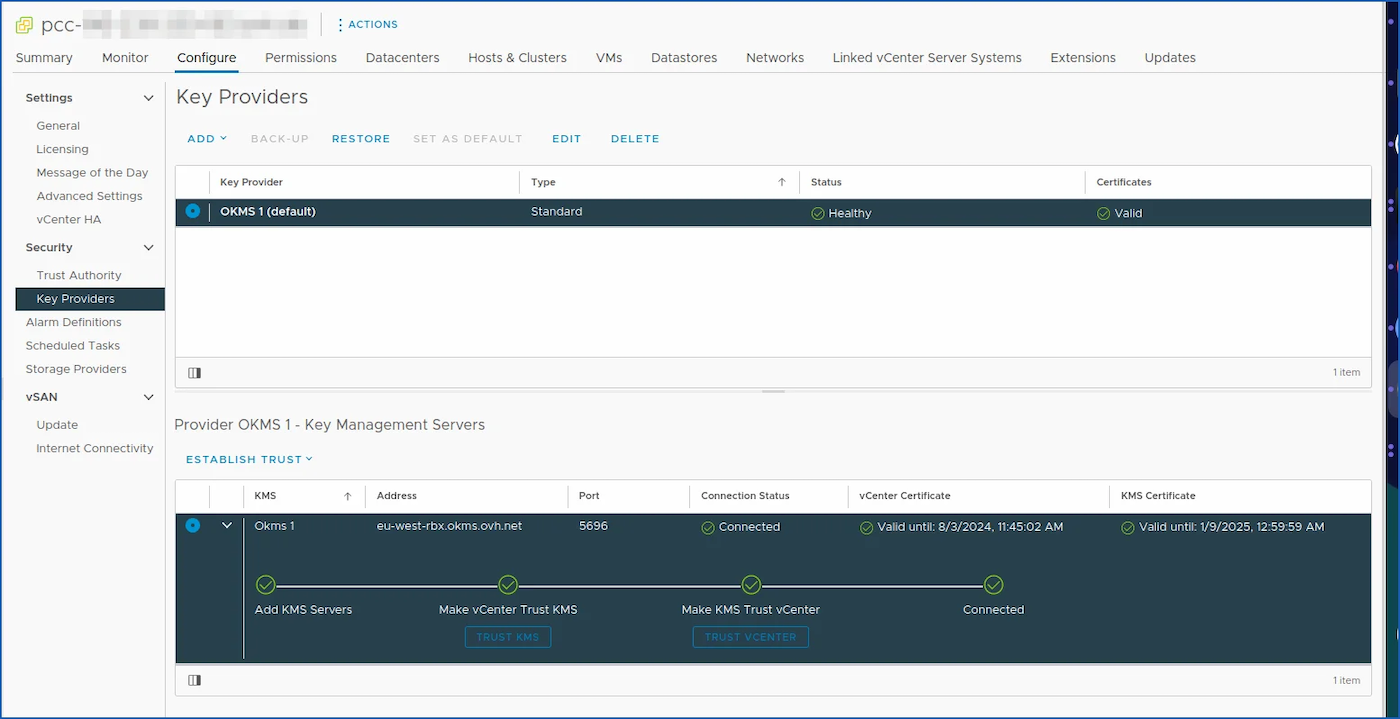
Move to the bottom Provider OKMS 1 - Key Management Servers by clicking on the small circle and also on the right arrow to unfold and display your KMS.
If you do not see that the trust relationship automatically turns green, click on TRUST KMS
Then click on TRUST
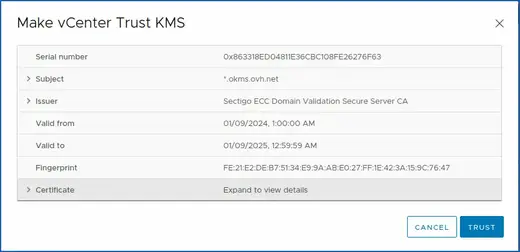
Typically, vCenter automatically downloads the KMS public certificate. If it doesn't, do it manually.
You can retrieve it from the endpoints provided with this snippet (if you need additional information on the certificate, check the toolkit at the end of this guide):
Copy the return from -------BEGIN CERTIFICATE---- to -----END CERTIFICATE----- into your managed vSphere web interface.
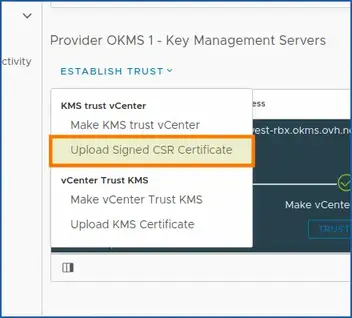
Click on ESTABLISH TRUST > vCenter Trust Kms > Upload KMS Certificate
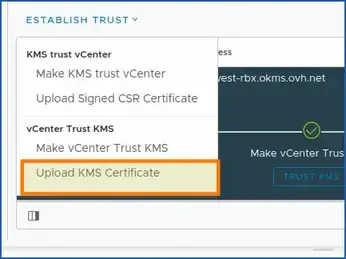
Finally, paste the public KMS certificate retrieved from the snippet into the vSphere window.

Wait a little while and refresh the vSphere Web page as explained before (for refreshing a vSphere Web console).
Select your Key Provider KMS (OKMS) that you have just added, and click the Approve vCenter Instance button.
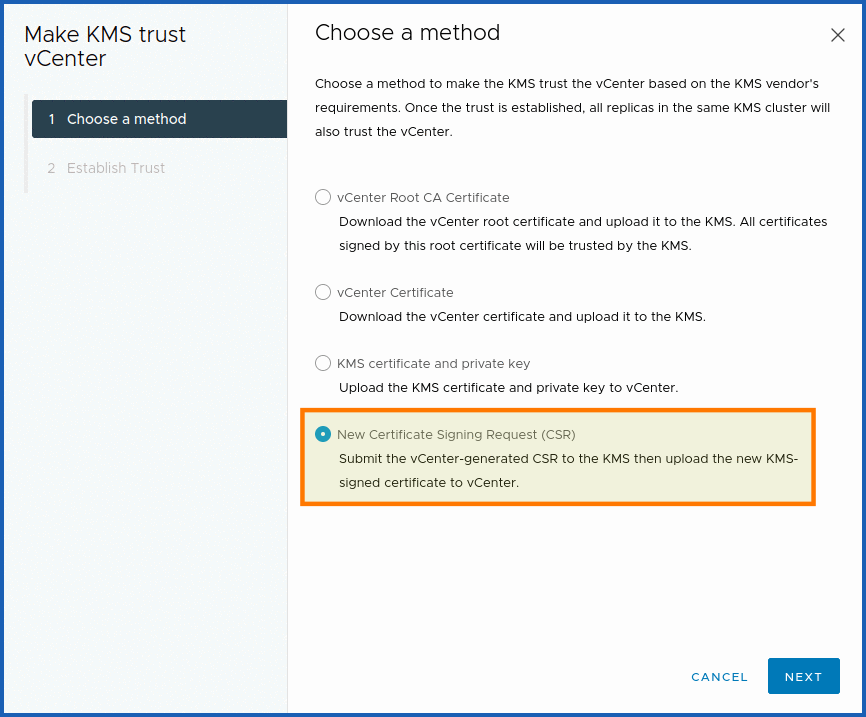
We recommend the more secure "With CSR" method by clicking on New Certificate Signing Request (CSR). However, you are free to choose the one that suits you best.
For more information on the advantages and disadvantages of using a CSR, read the KMS documentation.
With CSR (recommended) :
In order to communicate with your KMS, you need to create an access certificate signing (CSR) request. This will be used for all interactions with the OVHcloud KMS and vSphere, whether for creating encryption keys or performing operations with them.
Each certificate contains an OVHcloud identity that can be used to calculate access rights via the OVHcloud IAM.
This certificate can be generated by providing your own private security key ("credentialId") via a Certificate Signing Request (CSR).
Once your KMS is ordered and vCenter has approved the KMS. Launch the generation of the CSR in order for KMS to approve vCenter and sign the CSR.
Click Make KMS Trust vCenter.
Select New Certificate Signing Request (CSR), then copy or download the CSR below. Make it available to the OVHcloud KMS via the API v2 /okms, and ask them to sign the certificate.
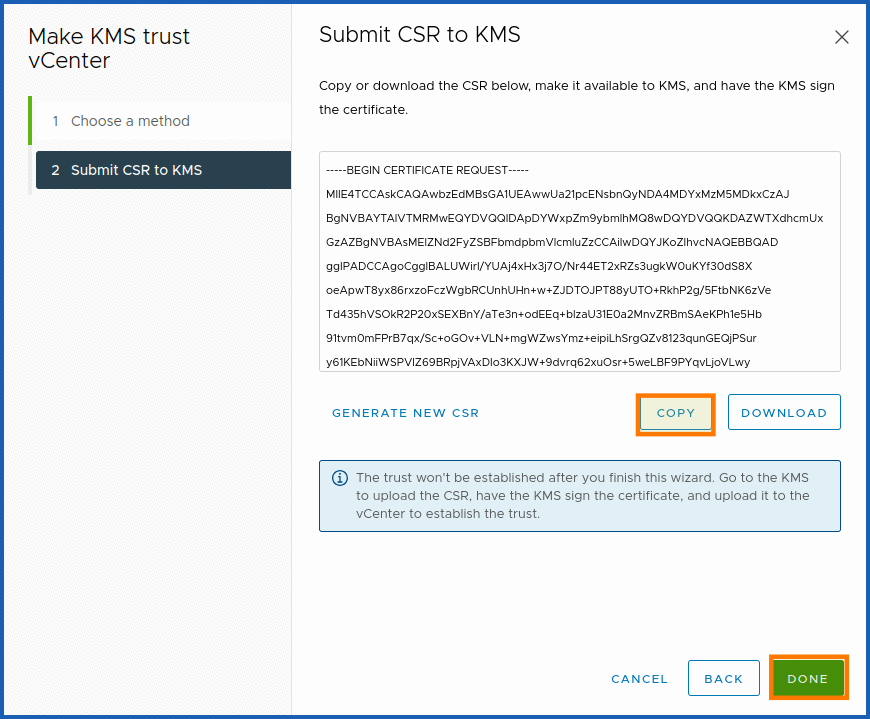
Copy your CSR into a file csr.pem in order to have it signed by the OVHcloud KMS.
To format the CSR in json to work in the OVHcloud API console, run the AWK command below:
Paste the return of this command into the following API POST call, in the "csr" field, to have your CSR signed with the OVHcloud KMS.
Make sure to fill in the rest of the fields (Urn, Description, etc..) with the correct IAM permissions.
Settings:
okmsId: ID of your OVHcloud KMS (OKMS).With CSR provided: Trust chain between OKMS and VCenter with or without CSR.
A "credentialId" of the signature will be given to you to prove it as been signed. You need to retrieve it with the okmsId in order to launch the next API call GET (see below) and retrieve the signed CSR. All you need to do now is to upload the signed CSR to the vSphere Web interface.
Now copy the signed CSR of the following API call:
Settings:
credentialId: ID generated during your API POST call /okms/resource/{okmsId}/credential with CSR ("fromCSR": true,)okmsId: ID of your OVHcloud KMS.
Copy the "certificatePEM" (signed CSR) from ------BEGIN CERTIFICATE------ until the end of -----END CERTIFICATE------.
Then run the AWK command below to format it so that the Web vSphere interface can read it:
Copy the command return and paste it in the vSphere Web interface.
To upload the signed CSR, click on ESTABLISH TRUST, then KMS Trust vCenter > Upload Signed CSR Certificate.

Check that the connection has been established by selecting your OVHcloud KMS key provider.
The Connected option must be confirmed with a green validation bracket (as in the screenshot below)
Step 5 - Create a VM storage policy (required)
How do I create a VM storage policy to enable encryption in VMware vSphere?
In step 6, you will complete the encryption activation on a virtual machine with the OKMS using a Storage Policy that we will now create.
This storage policy uses host-based policies. You must have enabled Host-based rules, and then enabled the storage policy components.
To create a storage policy, you need to access your PCC vSphere. If you have followed the previous steps, you must already be logged in to the control panel, after adding your OVHcloud KMS in step 4.
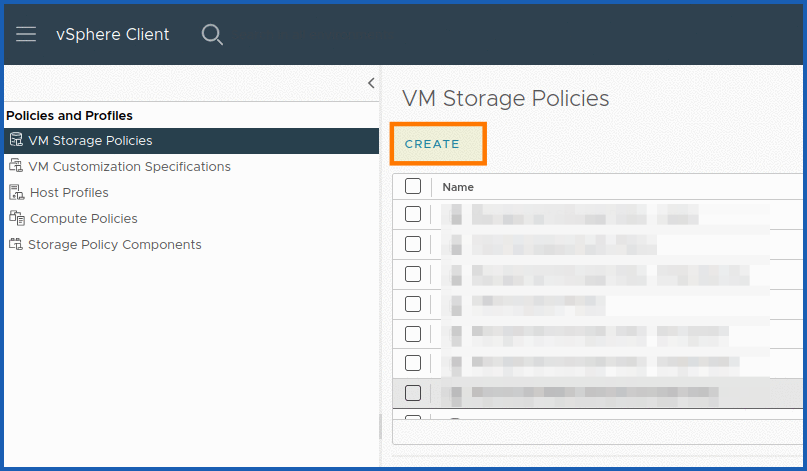
You now need to go to Policies and profiles > VM storage strategies.
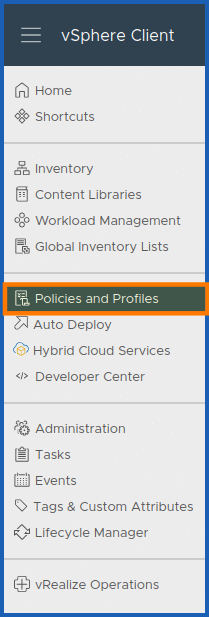
Click CREATE in VM Storage Policies.
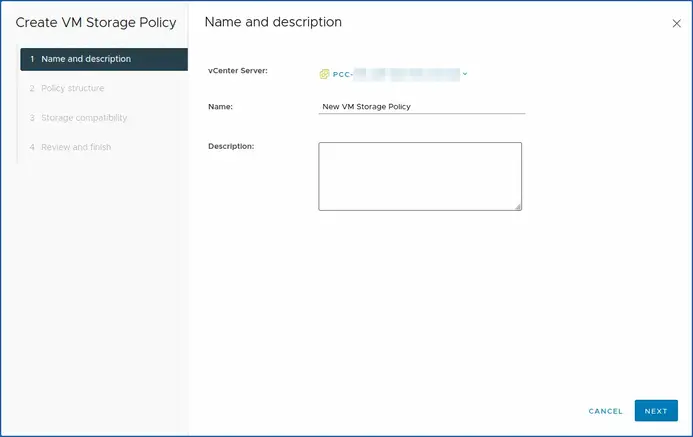
The policy creation window will now open. You are in step 1 Name and description.
You need to determine your vCenter server, which is the PCC on which you want to create your storage strategy.
Once you have PCC-XXX-XXX-XXX-XXX.ovh.XX chosen, give it a Name and Description.
You can click NEXT to continue.
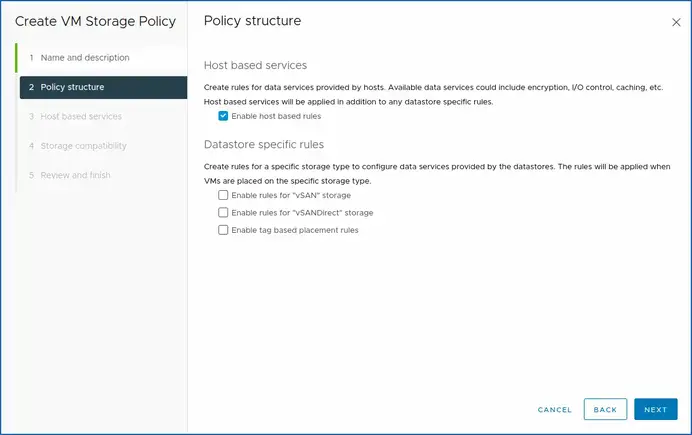
This brings you to step 2, Policy structure.
Here, we will enable host-based policy rules. Select the Enable host-based rules checkbox.
To continue, click NEXT.
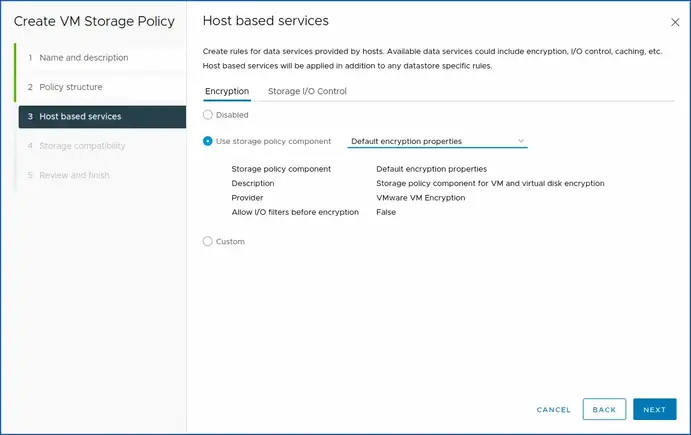
For step 3, you must confirm the choices in the previous step by enabling validation of the storage policy component (encryption).
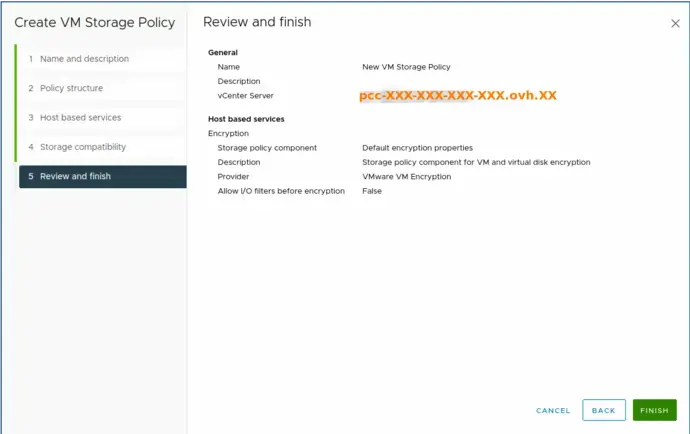
For the purposes of this guide, we will leave the default setting Default encryption properties.
You must click Encryption.
Then use the storage policy component Default encryption properties.
- Storage policy component: Default encryption properties.
- Description: Storage policy component for VM and virtual disk encryption.
- Provider: VMware encryption.
- Allow I/O filters before encryption: False.
For your information, these available data services may include encryption, I/O control, caching, and so on. Host-based services will be applied in addition to the data store-specific rules.
To complete step 3, click NEXT.
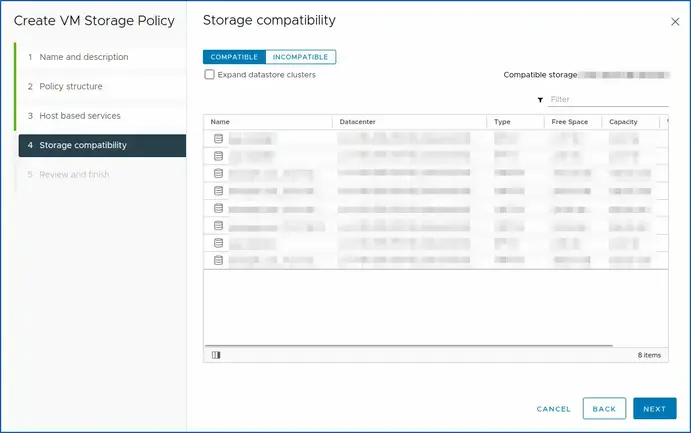
In step 4 (storage compatibility), yu have the compatibility and incompatibility of your Hosted Private Cloud VMware on OVHcloud datacentre (Dedicated Cloud).
When you have finished checking the compatibility of your storage space, click NEXT.
Click FINISH to finish the last step (step 5).
Once you have created your policy, you can now enable encryption on one of your virtual machines.
Step 6 - Enabling encryption on a VM (required)
How do I enable encryption in a VM with the storage policy?
Locate the virtual machine (VM) you want to encrypt. Turn it off if it is on (mandatory).
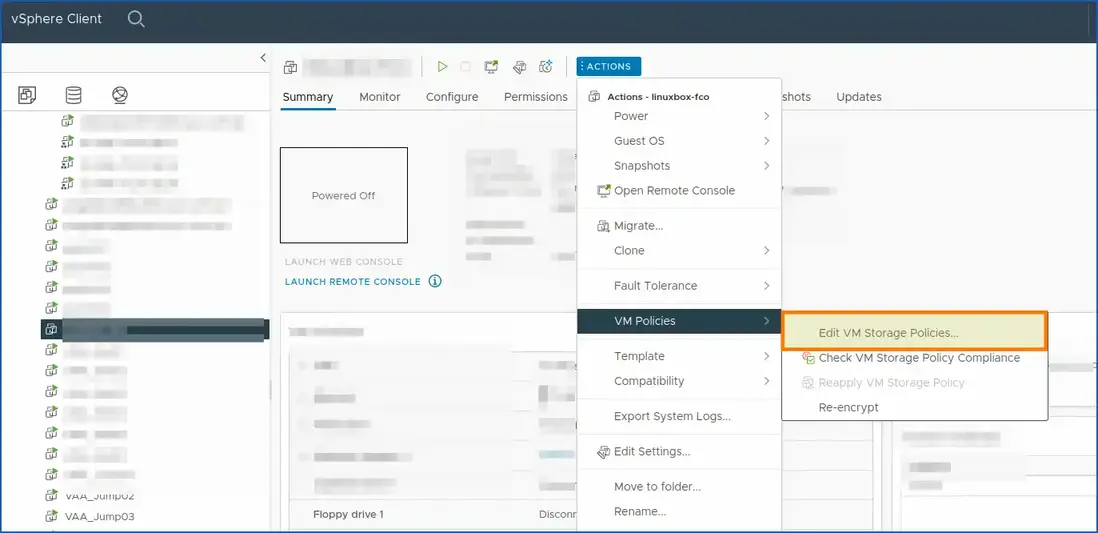
Right-click the selected virtual machine to display the shortcut menu or click ACTIONS.
Then select VM Policies.
Next, choose Modify VM storage strategies.
This will open a window or panel where you can modify the storage policies of the VM selected.
Search for encryption or security options in storage policies to enable KMS encryption for this VM.
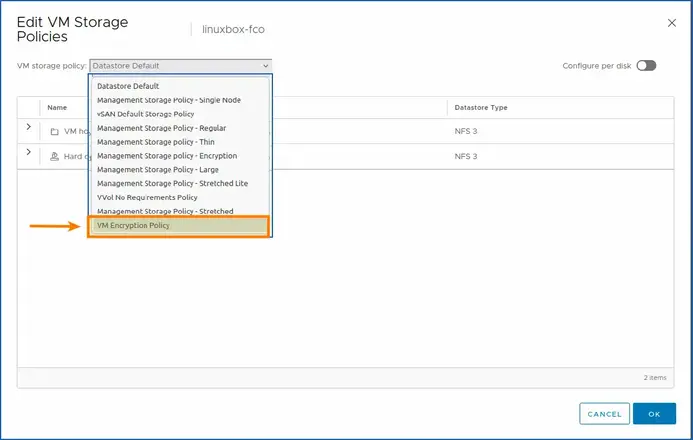
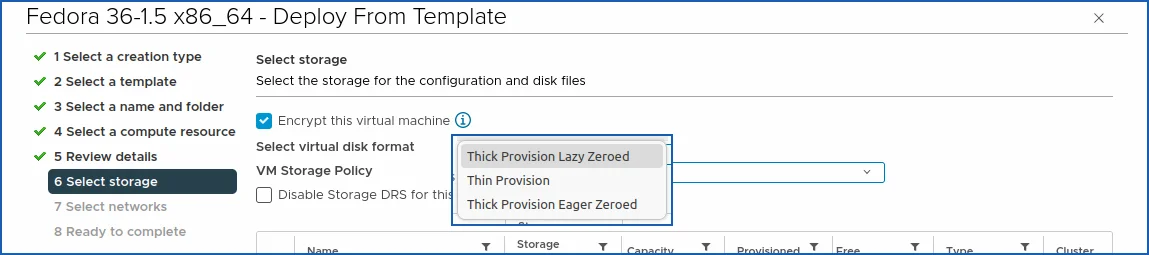
If you deploy a new VM from an OVHcloud template, you have several choices for encrypting your VM:
- Thick Provision Lazy Zeroed.
- Thin Provision.
- Thick Provision Eager Zeroed.
Choose the one that suits you best, if you have any doubts, use this guide: Which disk format to choose.
Tick the Encrypt this VM box.
After making the necessary changes, save the changes and close the window.
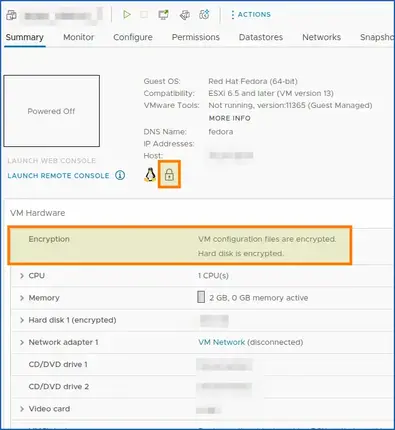
You have now edited the VM storage policies and enabled KMS encryption for your server. A small padlock on your virtual machine’s summary information confirms this.
You should now clearly see a small padlock in the general view of your VM as well as in the description of the encryption.
This confirms that your policy works with the OKMS server and that encryption is enabled.
Go further
Useful information - TLS/KMS
Useful information for manipulating your TLS certificates with OpenSSL and more
Warning: when you copy and paste your CSR, it must be formatted to work with json format.
\n must be added at each line break. To do this, you can launch this OpenSSL command in order to convert your certificate to pkcs12 format:
openssl pkcs12 -export -inkey client.key -in client.crt -out cert_key.p12.
CSR decode:
To decode your CSR, you can run this OpenSSL command with your CSR:
openssl req -in mycsr.csr -noout -text.
Or use a more graphical web tool, such as: sslshopper.
Certificate decode:
openssl x509 -in certificate.crt -text -noout.
Certificate Key Matcher:
To check if the CSR matches your certificate, you can do so with these OpenSSL commands:
SSL Converter
OpenSSL Convert PEM:
- Convert PEM to DER:
openssl x509 -outform der -in certificate.pem -out certificate.der. - Convert PEM to P7B:
openssl crl2pkcs7 -nocrl -certfile certificate.cer -out certificate.p7b -certfile CACert.cer. - Convert PEM to PFX:
openssl pkcs12 -export -out certificate.pfx -inkey privateKey.key -in certificate.crt -certfile CACert.crt.
OpenSSL Convert DER
Convert DER to PEM:
openssl x509 -inform der -in certificate.cer -out certificate.pem.
OpenSSL Convert P7B:
- Convert P7B to PEM:
openssl pkcs7 -print_certs -in certificate.p7b -out certificate.cer.
Convert P7B to PFX:
openssl pkcs7 -print_certs -in certificate.p7b -out certificate.cer.openssl pkcs12 -export -in certificate.cer -inkey privateKey.key -out certificate.pfx -certfile CACert.cer.
OpenSSL Convert PFX:
- Convert PFX to PEM:
openssl pkcs12 -in certificate.pfx -out certificate.cer -nodes.
Format CSRs for VMware
Adapt the command with your CSR file.
Retrieve the OKMS public certificate manually (optional)
If you encounter any difficulties during step 4 Make vCenter trust KMS, you can download it (manual download: copy the snippet return from a shell and paste it into the vSphere web interface "Download the KMS certificate").
You can launch this snippet (you need to have Python and OpenSSL installed). It allows you to export and format the public OKMS certificate.
Change the OKMS input with the URL of the correct region. You must have Python and OpenSSL installed:
If you require training or technical support to implement your migration with Public VCF as-a-Service, please contact your TAM or click here to get a quote and request a custom analysis of your project from our Professional Services team experts.
Join our community of users.