Object Storage - Identity and access management
Objective
This guide explains how to manage identities and access to your Object Storage resources.
Requirements
- A Public Cloud project in your OVHcloud account
OVHcloud Control Panel Access
- Direct link: Public Cloud Projects
- Navigation path:
Public Cloud> Select your project
Instructions
Click on Object Storage in the left-hand menu.
Creating a user
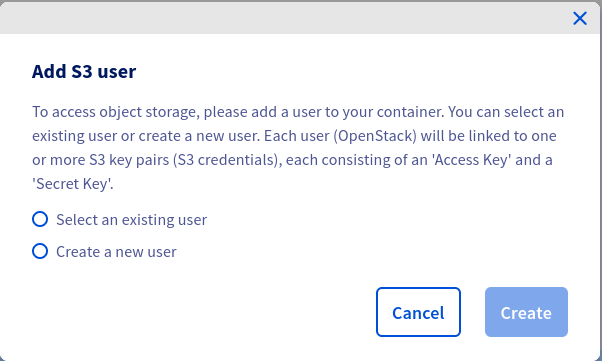
Click Create User.
If you already have OpenStack users, you can select one of these:
then
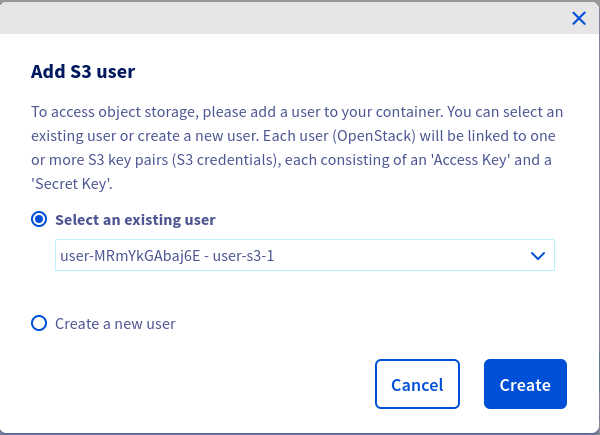
If you choose to select an existing user, ensure that the user has an ObjectStore operator or Administrator role.
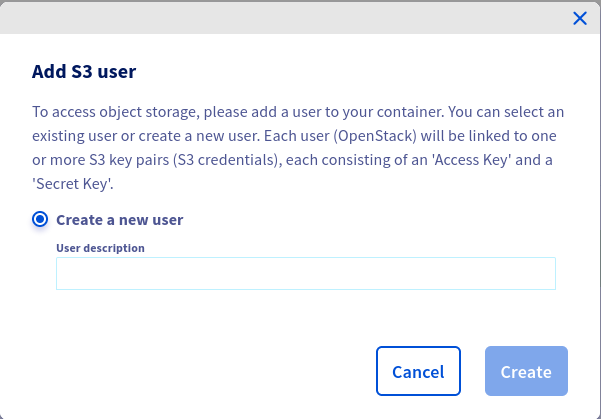
Otherwise, create a new user:
Once your user has been created, you will see the credentials:
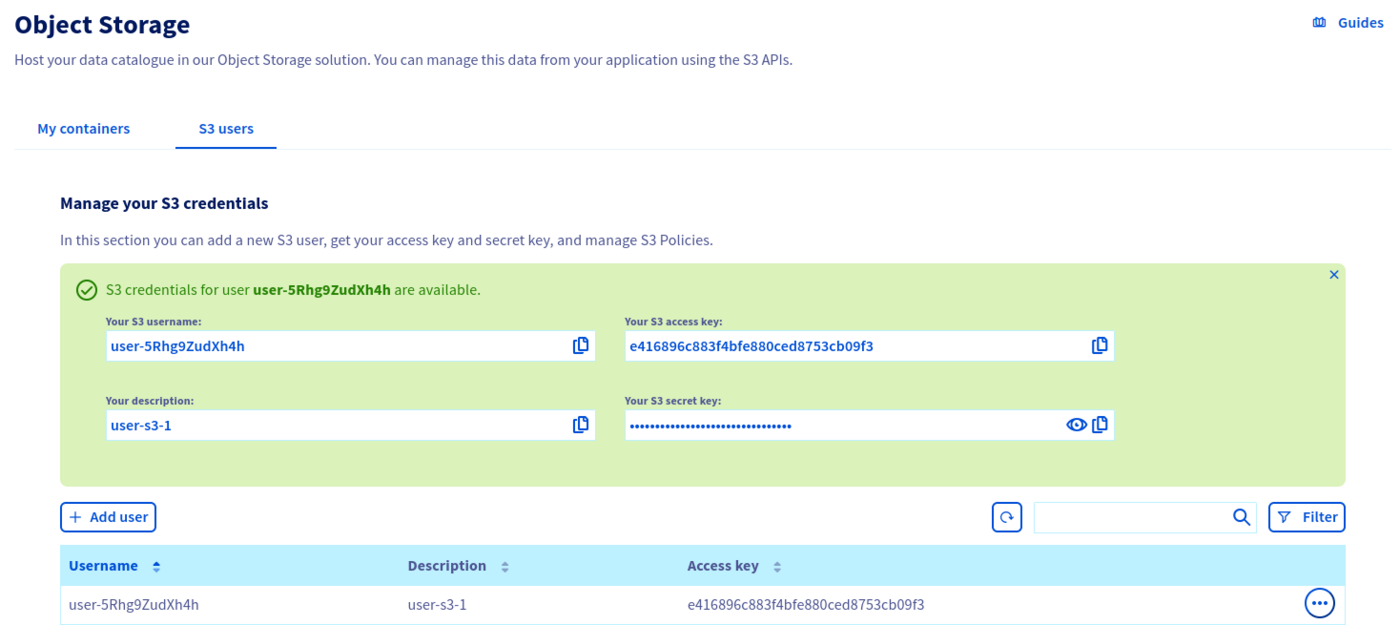
By clicking on the ... at the end of a user's line, you can, among other things, download the rclone configuration file, see the user's secret key, delete the user.
Manage access to a bucket via a profile
You can define access to your buckets via predefined profiles.
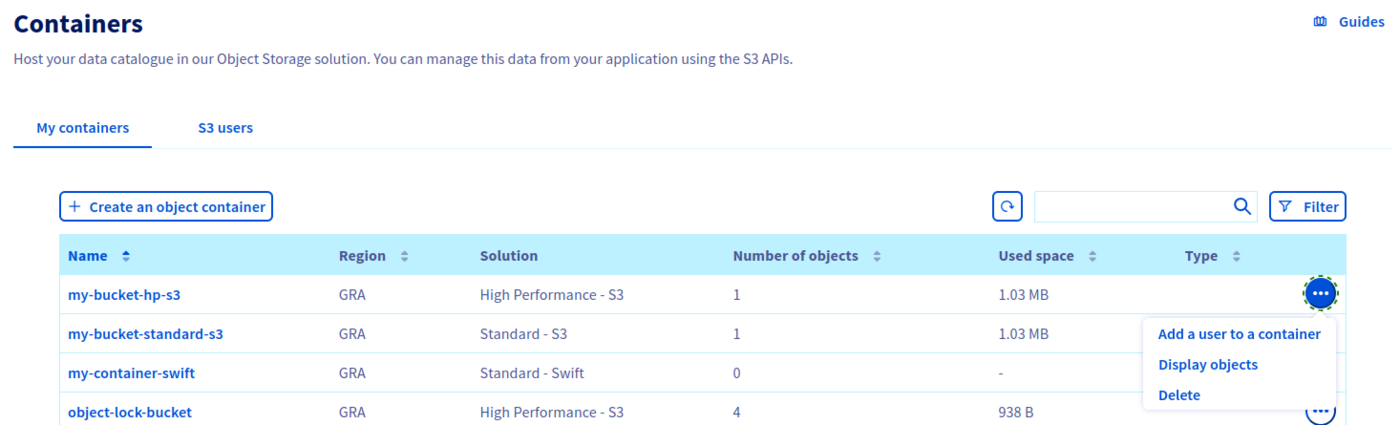
Click on the ... at the end of your bucket line, then Add a user to a container.
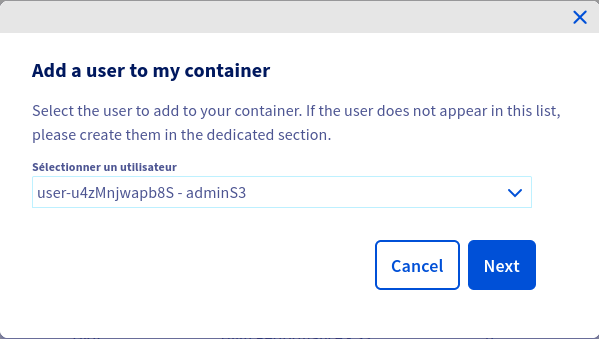
Select the user to add to your bucket and click Next.
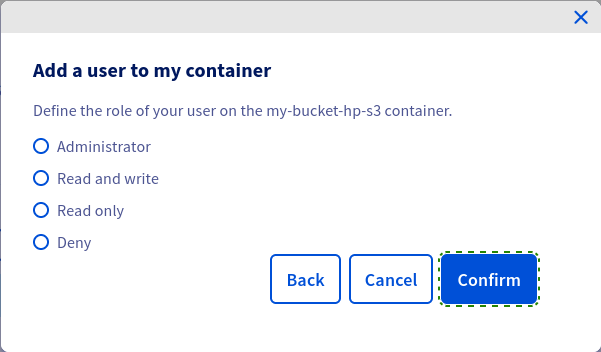
Set access to your bucket for this user and click on Confirm.
Advanced resource access management
Overview
By default, all resources (buckets, objects) and sub-resources (lifecycle configuration, website configuration, etc.) are private in Object Storage. Only the resource owner, i.e., the user account that creates it, has full control.
Access to private resources can be granted via access policies. Access policies can be categorized broadly into two types:
- user-based: access policies attached to a specific user are called user policies. A user policy is evaluated using Object Storage IAM permissions and applies only to the specific user it is attached to.
- resource-based: bucket policies and ACLs are policies that are attached directly to specific resources.
Bucket policies are a feature that is not yet available for Object Storage. This article is about user policies.
You can refine your permissions by importing a JSON configuration file. To do this, go to the Object Storage Policy Users tab.
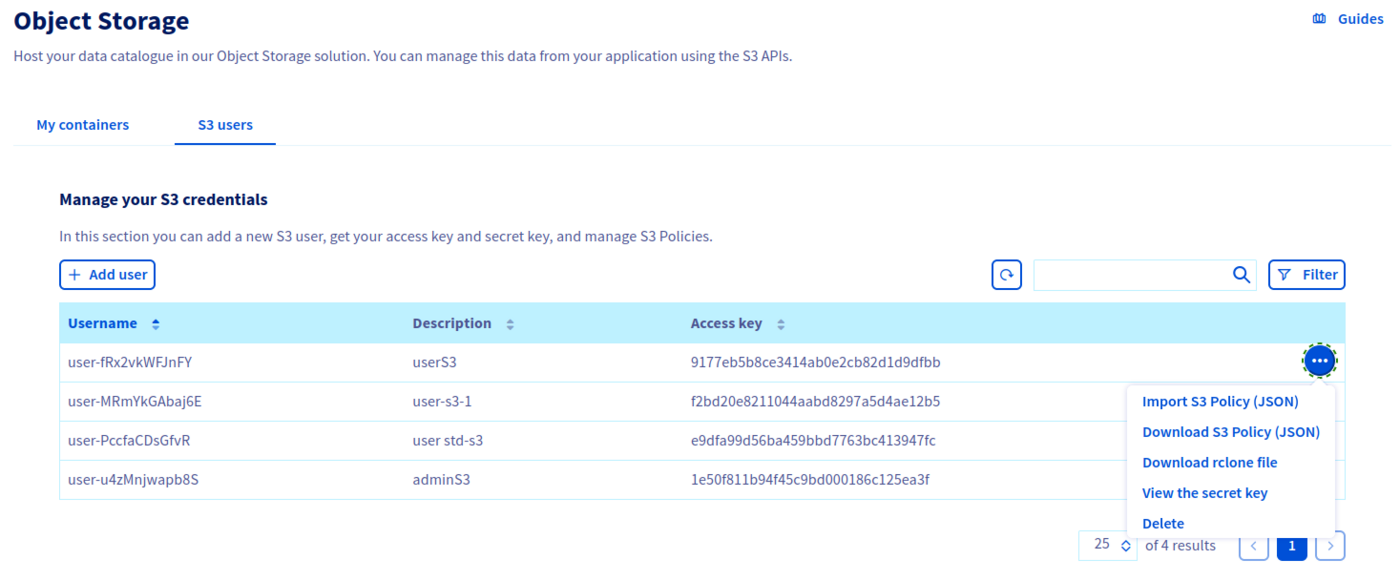
Click on the ... at the end of your user's line, then Import JSON file.
If you want to change a user's rights, you may need to download the JSON configuration file in advance by selecting Download JSON File.
Understanding the user policy evaluation process
At the moment, user permissions are evaluated as follows:
- if exists, evaluate user policy else fallback to ACLs
- check for an explicit deny: if there is an explicit deny, then deny permission, else, check for an explicit allow
- check for an explicit allow: if there is an explicit allow, then allow permission
- if there is no explicit deny nor explicit allow, then fallback to ACLs
- fallback to ACLs
This evaluation process will be subject to change with the upcoming implementation of bucket policies.
Some examples of JSON configuration files:
Read/write access to a bucket and its objects
Read-only access to a bucket and its objects
Deny listing of all buckets owned by the parent account
The (s3:ListAllMyBuckets) action is allowed by default for a given user. Add the Deny effect if you want to explicitly refuse the use of the ListBuckets API operation.
Allow all operations on all project resources
Read/write access to all objects in a specific folder (/home/user2) in a specific bucket (<bucket_name>)
Allow all operations to specific IPs by whitelisting authorized IPs
As a consequence of the current authorization process, implicit deny is not supported by OVHcloud Object Storage if the user is the bucket owner i.e., since ACLs are evaluated by default and since the bucket owner has FULL_CONTROL ACL, if the user is the bucket owner and even if there is no explicit allow in the policy file, the user will be authorized.
The following policy to attempt to allow read access to objects only to specific IPs will not work under current conditions if attached to the bucket owner i.e., even if the bucket owner makes requests from IPs that are not in the specified range, the bucket owner will be authorized.
The following policy to attempt to deny read access to objects to specific IPs by blacklisting unauthorized IPs will not work under current conditions if attached to the bucket owner because there is no explicit deny and requests from the specified IPs will not match the allow, therefore, we fall back to the ACLs.
List of supported actions
| Action | Scope |
|---|---|
| s3:AbortMultipartUpload | Object |
| s3:BypassGovernanceRetention | Object |
| s3:CreateBucket | Bucket |
| s3:DeleteBucket | Bucket |
| s3:DeleteObject | Object |
| s3:DeleteBucketTagging | Bucket |
| s3:DeleteBucketWebsite | Bucket |
| s3:DeleteObject | Object |
| s3:DeleteObjectTagging | Object |
| s3:GetBucketAcl | Bucket |
| s3:GetBucketCORS | Bucket |
| s3:GetBucketLocation | Bucket |
| s3:GetBucketLogging" | Bucket |
| s3:GetBucketObjectLockConfiguration | Bucket |
| s3:GetBucketTagging | Bucket |
| s3:GetBucketVersioning | Bucket |
| s3:GetBucketWebsite | Bucket |
| s3:GetEncryptionConfiguration | Bucket |
| s3:GetIntelligentTieringConfiguration | Bucket |
| s3:GetLifecycleConfiguration | Bucket |
| s3:GetObject | Object |
| s3:GetObjectAcl | Object |
| s3:GetObjectLegalHold | Object |
| s3:GetObjectRetention | Object |
| s3:GetObjectTagging | Object |
| s3:GetReplicationConfiguration | Bucket |
| s3:ListAllMyBuckets | Bucket |
| s3:ListBucket | Bucket |
| s3:ListBucketMultipartUploads | Bucket |
| s3:ListMultipartUploadParts | Object |
| s3:ListBucketMultipartUploads | Bucket |
| s3:ListBucketVersions | Bucket |
| s3:ListMultipartUploadParts | Object |
| s3:PutBucketAcl | Bucket |
| s3:PutBucketCORS | Bucket |
| s3:PutBucketLogging | Bucket |
| s3:PutBucketObjectLockConfiguration | Bucket |
| s3:PutBucketTagging | Bucket |
| s3:PutBucketVersioning | Bucket |
| s3:PutBucketWebsite | Bucket |
| s3:PutEncryptionConfiguration | Bucket |
| s3:PutIntelligentTieringConfiguration | Bucket |
| s3:PutLifecycleConfiguration | Bucket |
| s3:PutObject | Object |
| s3:PutObjectAcl | Object |
| s3:PutObjectLegalHold | Object |
| s3:PutObjectRetention | Object |
| s3:PutObjectTagging | Object |
| s3:PutReplicationConfiguration | Object |
Go further
If you need training or technical assistance to implement our solutions, contact your sales representative or click on this link to get a quote and ask our Professional Services experts for assisting you on your specific use case of your project.
Join our community of users.