Manage your server reboot with the OVHcloud Link Aggregation feature
Objective
This guide is designed to help you deploy all of the components and services you need to launch your OVHcloud solutions successfully in a fully private environment.
Get a private infrastructure without having to change the default configuration for your OVHcloud dedicated servers.
We have already carried out all our tests, qualifications and configuration validations, based on well-defined parameters and operating criteria, in order to offer you technical environments that are best adapted to your hardware.
Netboot (Network Boot) consists of using your network interface (in low-level mode) as a tool to select the boot of your operating system.
You can boot any system from a network volume, such as SAN or NFS. However, the system usually boots from a local volume: local disk, CD/DVD or USB.
As a reminder, we strongly advise against changing the default configurations: BIOS configuration, Boot Order, etc.
We have pre-configured this startup mechanism in our solutions, and have integrated all of our tools into it: netboot, monitoring, recycling, etc. If these settings were to be modified, our teams would no longer be able to perform the tasks dedicated to them under the conditions we have chosen, and above all, you could render the boot inoperative.
With OVHcloud dedicated servers, you can configure/declare your own networks.
Each server is equipped with at least 2 network interfaces, effectively functioning as aggregated links, ensuring redundancy in the event of failure.
You can therefore use/declare your public and private networks via our solution vRack.
We will present the case of dedicated server(s) configured in OLA mode, i.e. with only private networks.
This choice offers your infrastructure the best possible isolation/protection for your hosted service.
The only significant difference is that private networks do not have access to everything that does not belong to your infrastructure.
As a result, a server isolated by its private network prevents the boot mechanism. This means that when systems are booted via the Netboot (Network Boot) method, they are based on OVHcloud’s internal network and shared services.
Netboot startup overview
A major component exists in 2 versions:
- PXE: Using a standardised client/server environment, based on BOOTP/DHCP/TFTP protocols, to enable boot/deployment through the client system network.
- iPXE: Using a more advanced, standardised client/server environment, based on HTTP, iSCSI, AoE, FCoE, Wi-Fi protocols to enable client system network boot/deployment.
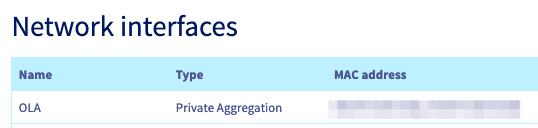
A quick overview of Netboot startup at OVHcloud
List of components involved during startup:
- A DHCP server: Assigns a network configuration (lease with IP address) for a client machine that is attempting to boot.
- A TFTP service: Resources available across the network that will be queried by PXE and iXPE.
- The rEFInd solution, in the form of a BootLoader, was chosen because it was perfectly adapted. It will allow the search of boot sectors of client machines: local disk, USB, etc.
Here is a (logical) Netboot boot schema:
| Description/Details |
|---|
| 1. Sending a discover request to DHCP from the client machine (in broadcast) |
| 2. DHCP assigns an IP address to the client machine (offer/request/ack). iPXE binary recovery request |
| 3. iPXE binary TFTP recovery |
| 4. Loading iPXE binary as firmware |
| 5. iPXE firmware recovery request |
| 6. Retrieving the associated iPXE script in TFTP |
| 7. Running the iPXE script. Retrieving rEFInd resources: required binary and configuration file |
| 8. Running and loading the rEFInd binary |
| 9. rEFInd launches its scan task to identify boot sectors for local disks |
This description is as generic as possible, in order to remain clear, and so as not to add technical elements or constraints that go beyond our example. The aim of this scheme is to provide an overall view of the operating principle.
Requirements
This article is intended for experienced users who have at least basic knowledge of the open-source world, as well as knowledge of system and network administration.
- At least one dedicated server with an operating system already installed.
- An additional dedicated server with the default network interfaces configured, namely public and private network access. This server will host all services (DHCP and TFTP). The operating system will be one of your choice.
- You must have all of the network interfaces for this server in private mode, which implies that you have already configured our OLA feature.
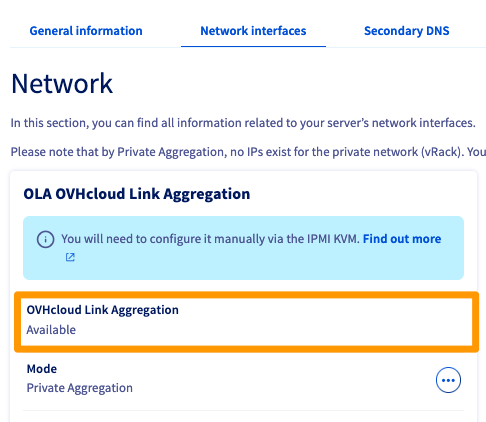
OVHcloud Control Panel Access
- Direct link: Dedicated Servers
- Navigation path:
Bare Metal Cloud>Dedicated servers> Select your server
Select your server and check that it is eligible for
OLA: OVHcloud Link Aggregationin theNetwork interfacestab.
Instructions
Deploy your DHCP and TFTP services
- Install the packages for DHCP/TFTP services.
- Perform the basic configuration for each service.
- Turn on your server.
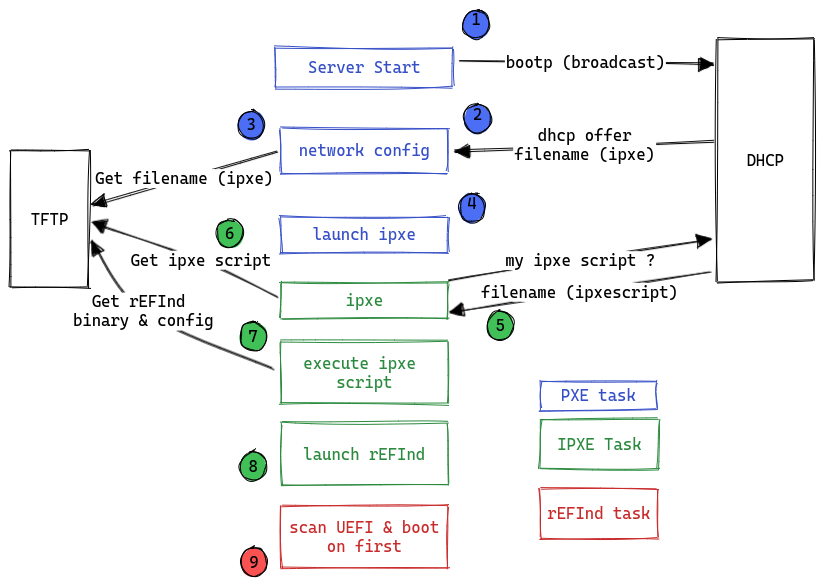
Below is an example of a basic private infrastructure (layer 2 diagram):
Example:
- Services hosted/shared on Node 0.
- Only one Node 1 client machine with active OLA.
After booting the systems, and in order for DHCP services and optional services (DNS and NTP) to be fully functional, consider declaring/adding rules in the local firewall, via the private network interface of the machine hosting the services.
DHCP service
Below is a sample configuration file for your DHCP service.
Depending on your distribution, the tree may be different (kea-dhcp4.conf).
In general, it is sufficient to:
- Declare a network interface for listening (waiting for requests).
- Specify the IP protocol version (v4 or v6).
- Enter a primary configuration file (as an example, see file below).
Details:
- Private network (e.g. 192.168.1.0/28)
subnet_mask: 255.255.255.240broadcast_address: 192.168.1.15dns_servers: See optional chapterntp_servers: See optional chapterdefault_router: 192.168.1.1next-server: 192.168.1.1host: Client machine namehardware ethernet: Client machine hardware address (MAC)server-name: Client hostname machine
TFTP service
Depending on your distribution, there are several packages performing the TFTP server function.
For example: tftp-server, tftpd, tftpd-hpa or atftpd.
The installation tree may be different depending on the version of the package and the operating system you are using.
What you need to know:
- This service uses port 69 (UDP).
- It is mandatory to declare a "target" directory, corresponding to a local tree that will be used for receiving and downloading files.
Configuration example with tftpd-hpa software:
We will use the path /srv/tftp as an example, and upload the necessary files:
The rEFInd bootloader
- File contents
refind.pxe:
- File contents
refind.conf:
This involves integrating the minimum guidelines for proper integration with OVHcloud SI.
Getting started
Below is a preview of what you get when displaying a UEFI Netboot (default):
Corresponds to steps 1 through 8.
Corresponds to the result of steps 8 and 9.
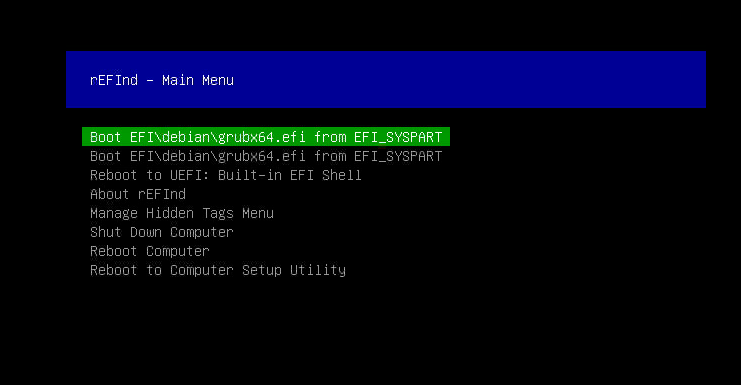
Above, we have the rEFInd bootloader loaded on a machine with a debian system installed.
You will find on this link the resources used to develop our tests and examples throughout this presentation. They can be used as templates, depending on your needs.
Optional
We also recommend deploying DNS and NTP services.
These are not necessary for the system startup phases, so not imposed in this procedure. They are, however, among the services that will be important in the future, especially for the stability of your infrastructure.
Service DNS
You can use the local table for each Node, i.e. the /etc/hosts file, or you can use a service like dnsmasq.
Service NTP
It is strongly recommended that you use an NTP service, especially if your infrastructure includes several machines.
- List of ports to authorise on your local firewall (on the machine hosting the services):
- NTP port 123
- DNS port 53
Go further
Understanding and customising your DHCP service
Understanding and customising your iPXE service
Understanding and customising your rEFInd service
Discovering and understanding NTP
Discovering and understanding Dnsmasq
Join our community of users.
-
Secure Shell (SSH) : un protocole de réseau sécurisé utilisé pour établir des connexions entre un client et un serveur. Il permet d'exécuter des commandes à distance de manière sécurisée. ↩