Deploy an SAProuter with NSX
Objective
This guides provides instructions for deploying an SAProuter on VMware on OVHcloud with NSX.
Requirements
- Access to the OVHcloud Control Panel.
- A VMware on OVHcloud solution deployed.
- Access to NSX with management rights.
Instructions
Network Firewall configuration
OVHcloud provides a firewall and anti-DDoS solution, the Network Firewall. This option protects you against potential attacks from the public network. We advise you to enable it for your public IP address which you will use in this configuration.
If you didn't create a Network Firewall and a firewall rule for the public IP address used by your NSX gateway, follow these steps to do it. If you are familiar with the Network Firewall, you can skip the first three steps.
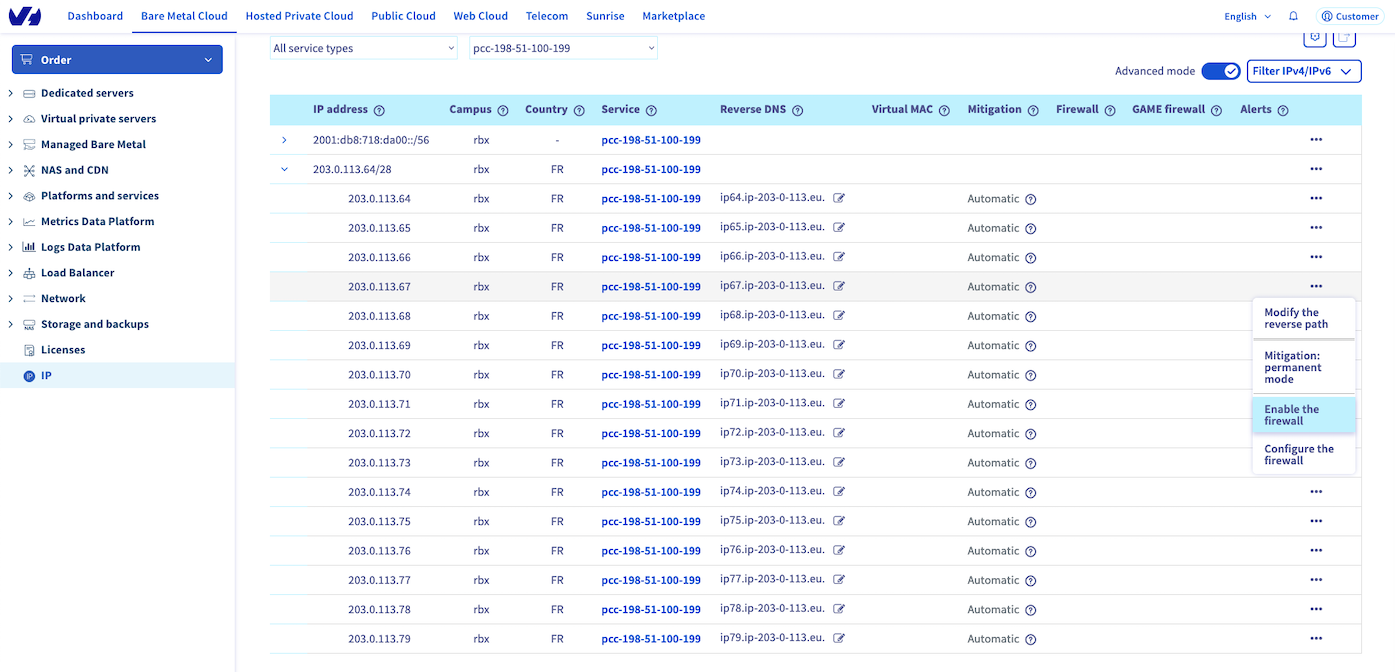
Connect to your OVHcloud Control Panel, open the Bare Metal Cloud tab, expand the Network menu then click on IP.
If you have many public IP addresses or services, you can filter them with the All service types value and select Hosting Private Cloud (VMware), or with the All services value and select your VMware on OVHcloud solution.
In our First steps with NSX guide, the Displaying the HA VIP virtual IP address chapter shows you the way to get the public IP address held by your NSX gateway.
Expand the IPv4 address block, select the IPv4 address used by your NSX gateway and click on Create Firewall.
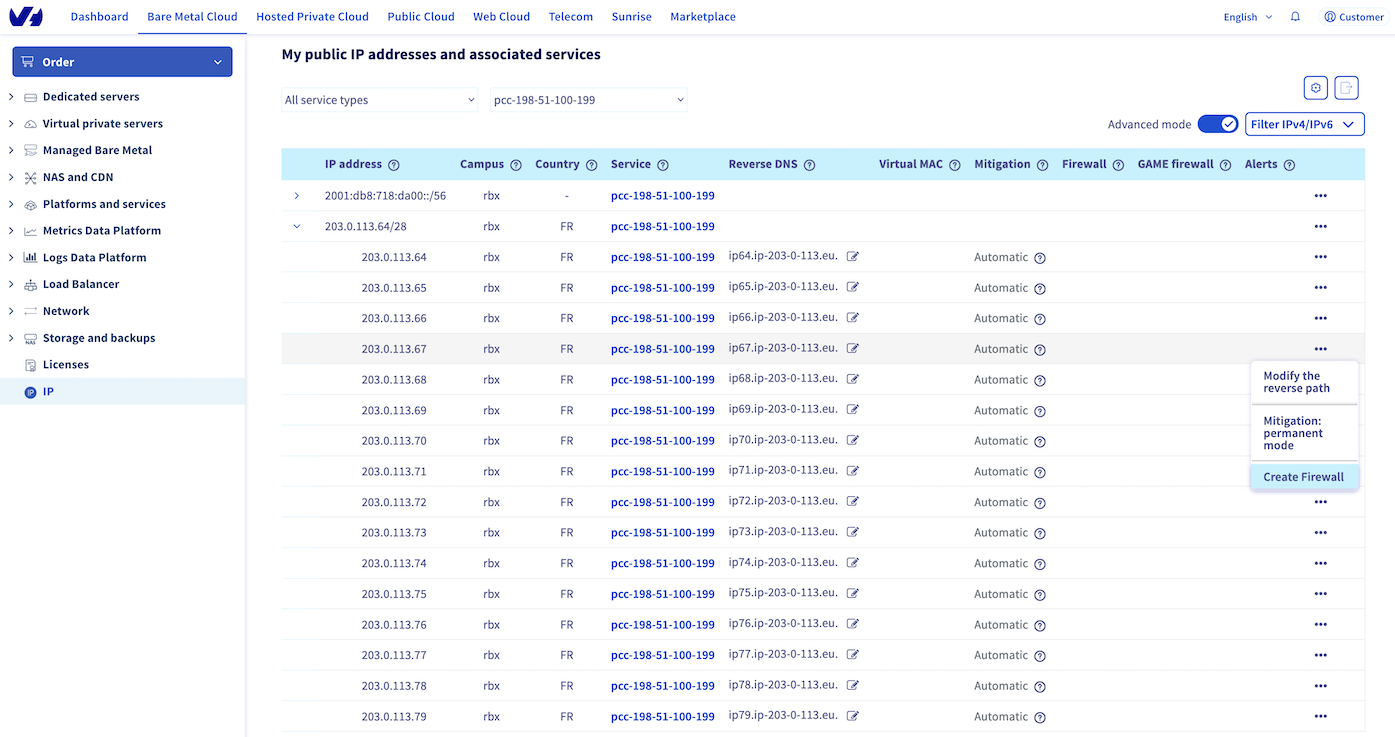
Click on Configure the firewall to open the edition window of your Network Firewall.
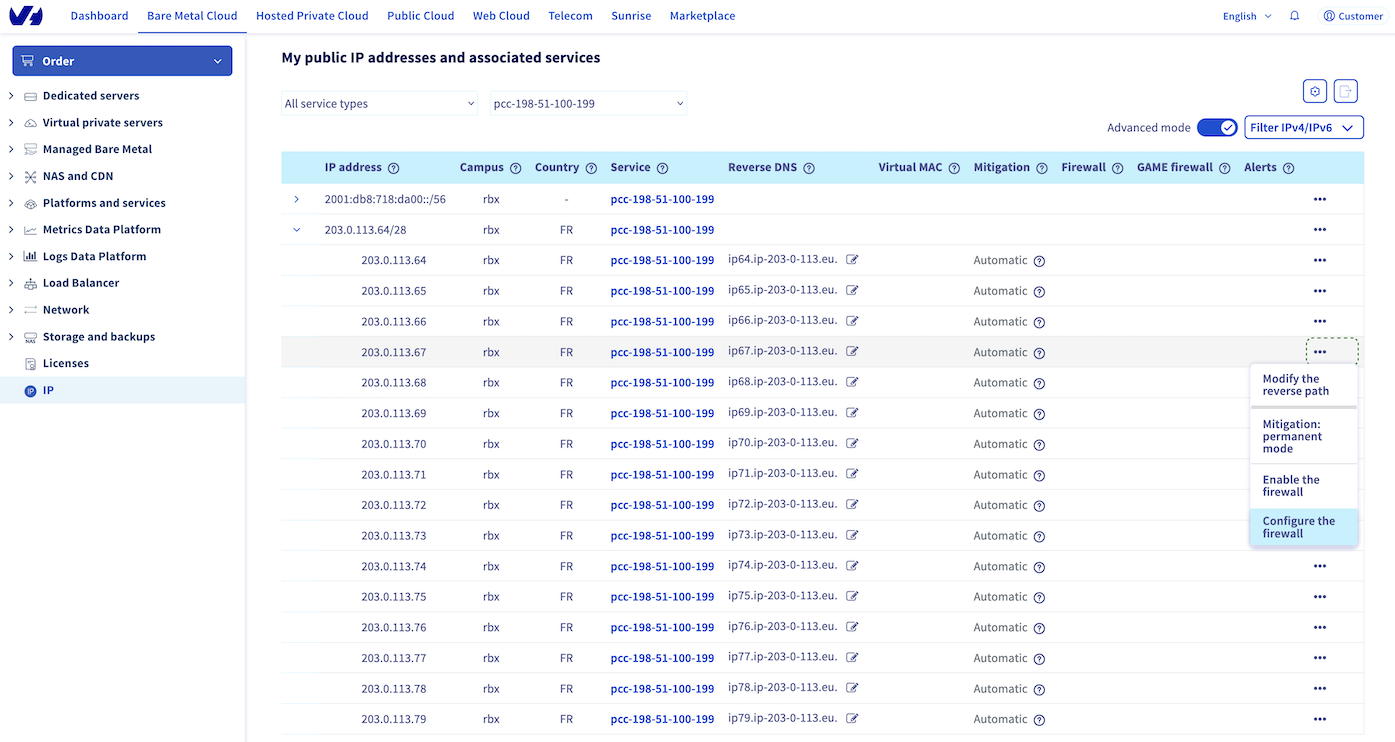
We advise you to create 2 default rules in your Network Firewall.
Click on Add a rule then set these parameters:
- Parameters for the first rule:
- Priority: 0
- Action: Authorise
- Protocol: TCP
- Flags: ESTABLISHED
We suggest that you authorise the TCP protocol from all IP addresses with the flag ESTABLISHED. This is to check that the packet is from a previous opened/initiated session. If you don't authorise it, the server won't receive TCP packets from SYN/ACK requests.
- Parameters for the second rule :
- Priority: 19
- Action: Refuse
- Protocol: IPv4
We recommend refusing all IPv4 traffic which wasn't authorised by any prior rule.

Create the rule to allow the connection from the SAP support infrastructure.
Click on Add a rule then set these parameters:
- Priority: 1
- Action: Authorise
- Protocol: TCP
- IP source: 194.39.131.34/32
- Destination port: 3299
- Flags: None
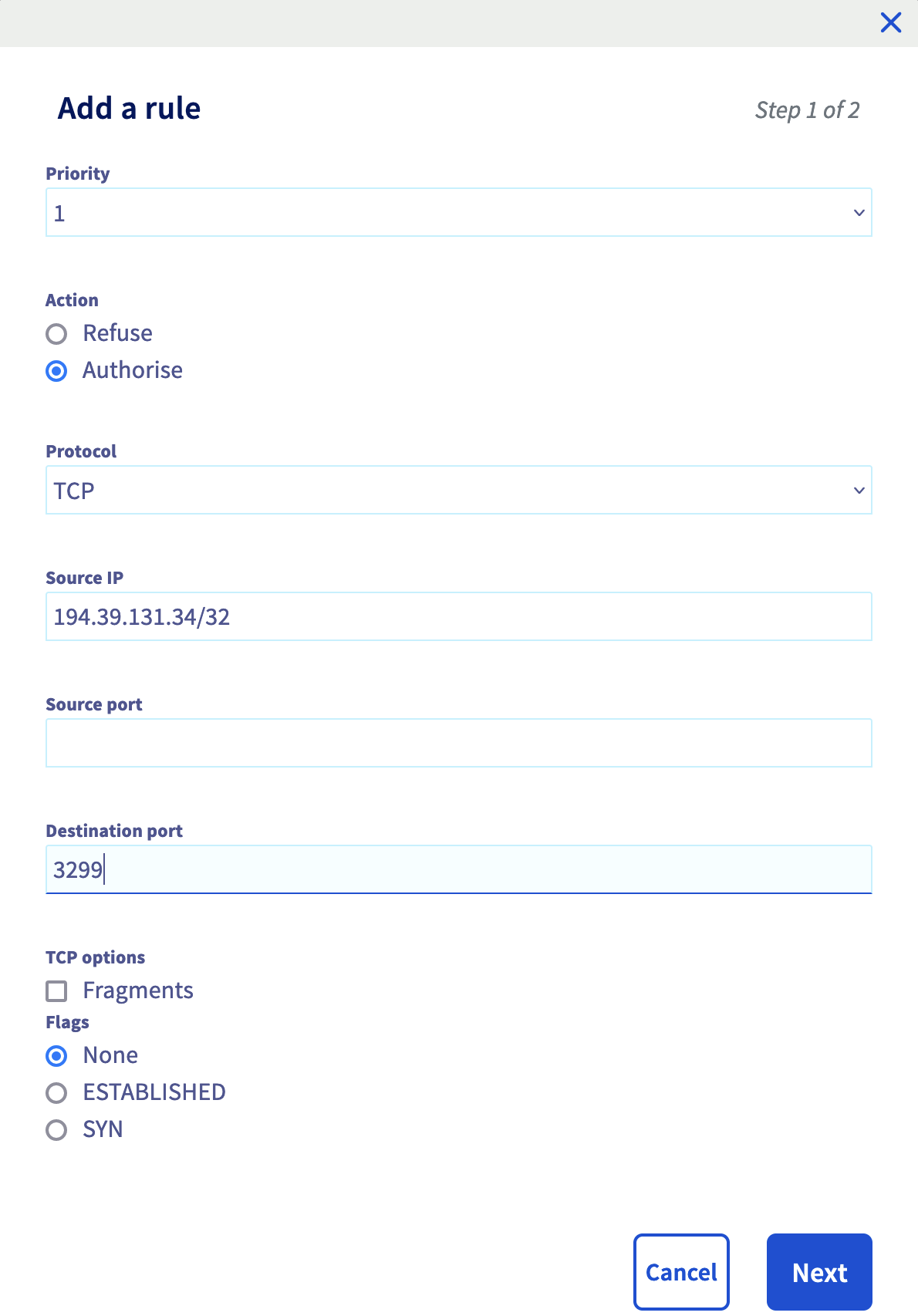
Find more information about the SAP support public IP address on the SAP support website.
After a few seconds, the rule is enabled.
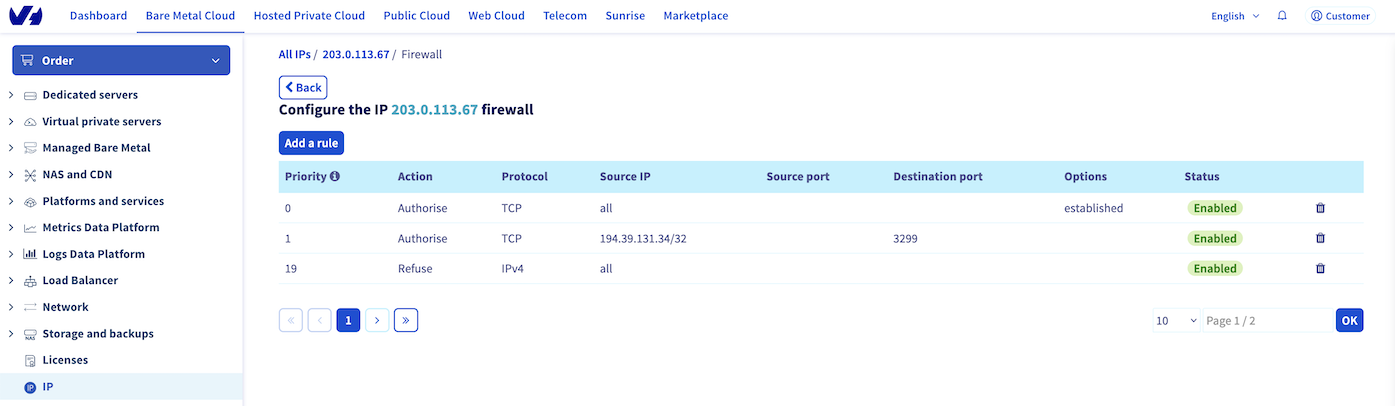
Click on the Back button, select the IP address where you have set up the rule and click on Enable the firewall.
NSX gateway configuration
The NSX gateway is the gateway between Internet and your SAP infrastructure hosts on your VMware on OVHcloud solution. You must configure the NSX gateway to allow the connection from SAP support to your SAP infrastructure via SAProuter.
Firewall
We recommend doing a network filtering on your NSX gateway, in addition of the network filtering done by the previously configured Network Firewall.
This network filtering on your NSX gateway allows you to secure your SAProuter if the Network Firewall was to be disabled on your public IP address.
Connect to your VMware on OVHcloud solution and click on the NSX tile.
Click on the Security tab then, in the Policy Management category, click on Gateway Firewall and select your T0 gateway "ovh-T0-xxxx".
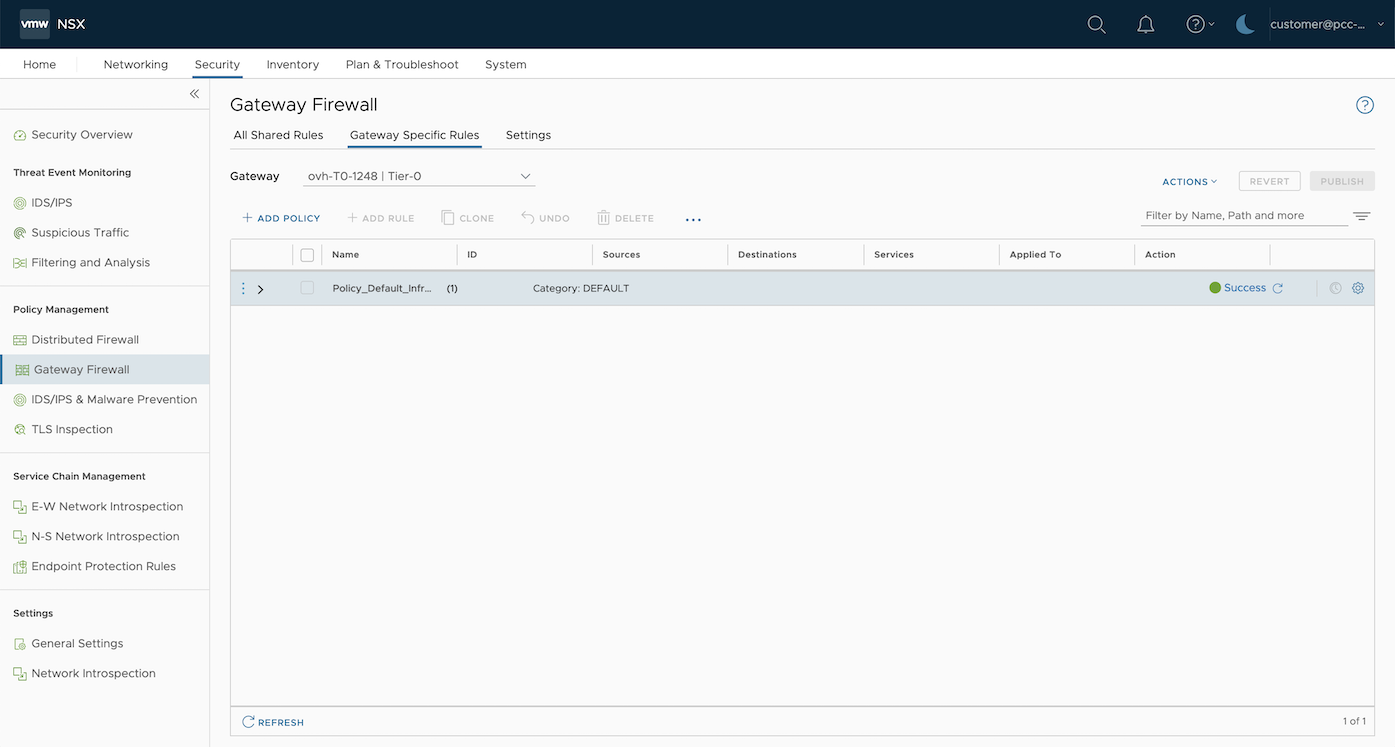
Click on Add policy and give it a name (example: SAP). Inside this policy, you can also set all SAP firewall rules.
Select your new policy and click on Add a rule.
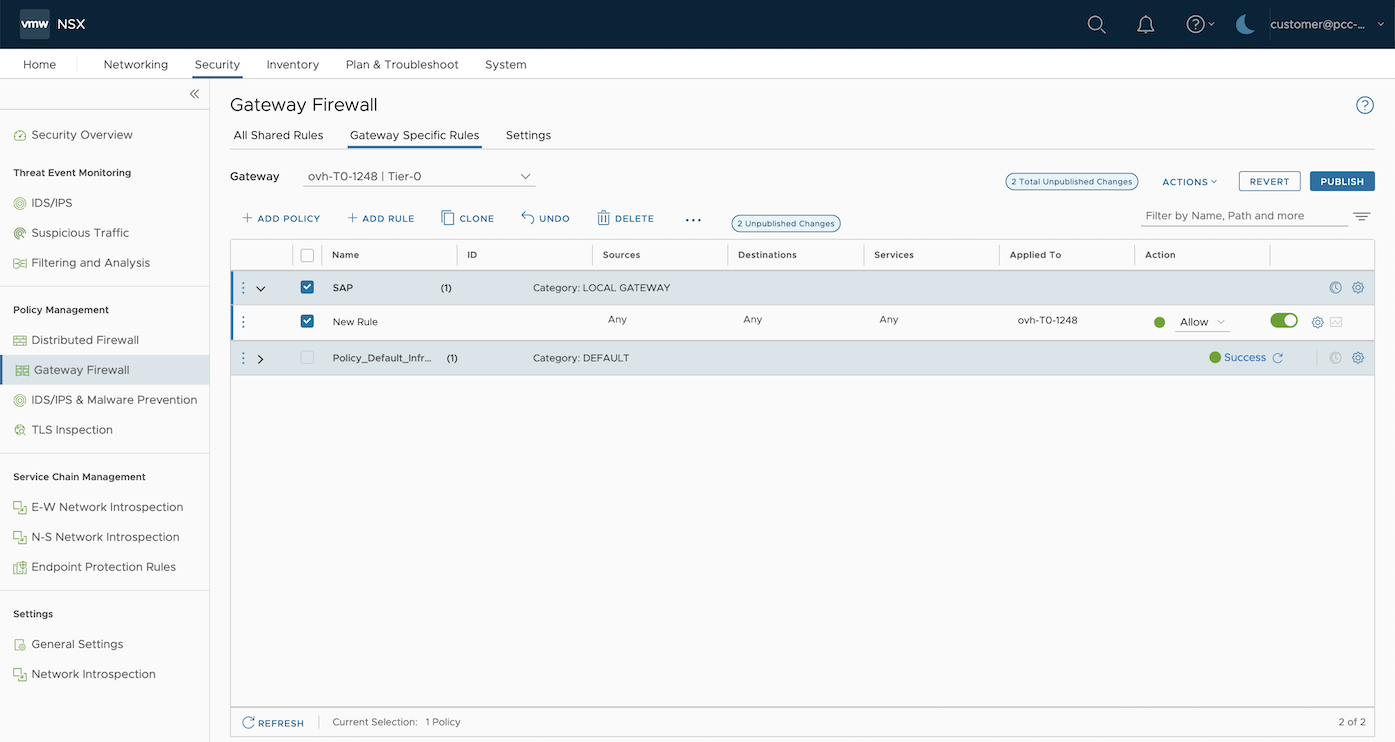
Set the following parameters:
- Name: SAP support
- Sources: 194.39.131.34/32
- Destinations: Private IP address of your SAProuter
- Services: TCP - Destination: 3299
- Action: Allow
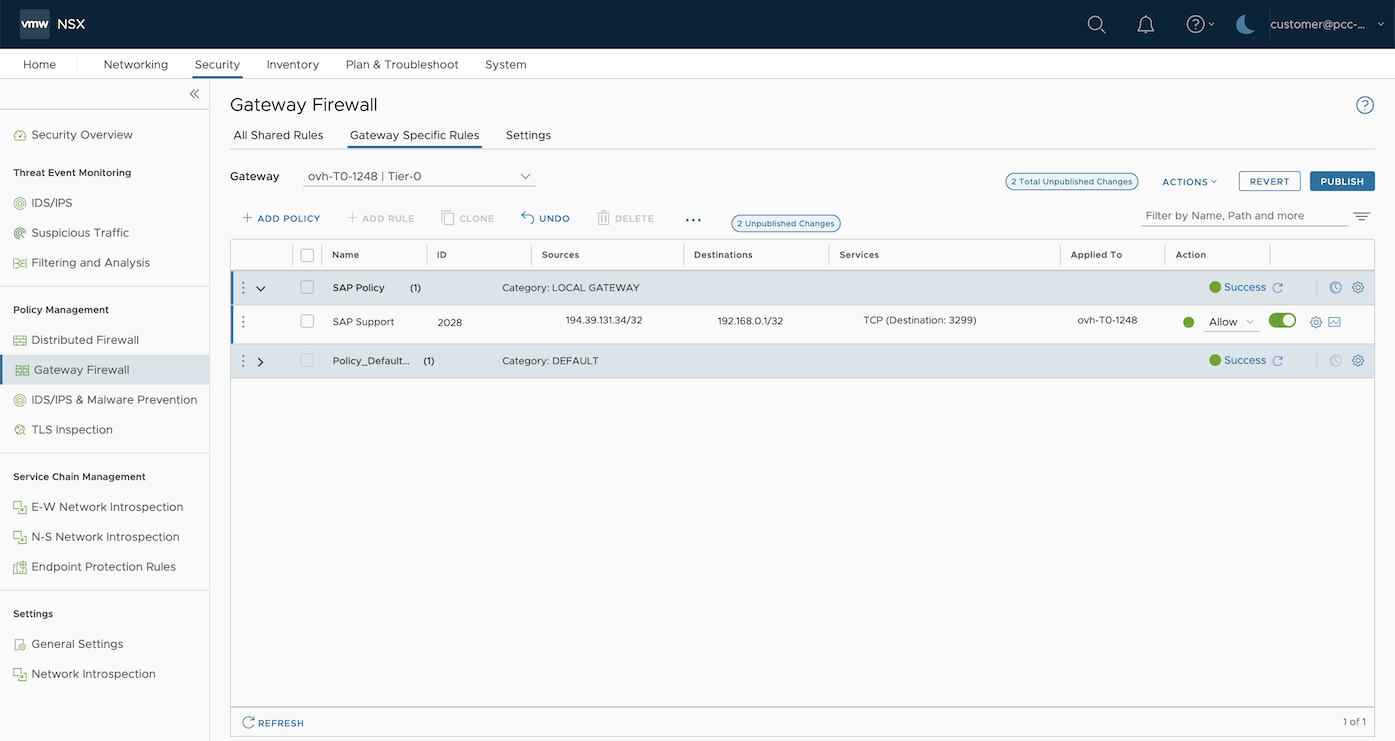
Once the rule has been created, click on Publish to update the configuration on the NSX gateway.
NAT
The SAProuter doesn't have a public IP address. You must apply the configuration to route the traffic on the port tcp/3299 from the public IP address held by your NSX gateway to your SAProuter.
You must create a Destination Network Address Translation (DNAT) rule.
This part shows you the steps to create a DNAT rule on an NSX gateway.
Click on the Networking tab then, in the Network Services category, click on NAT.
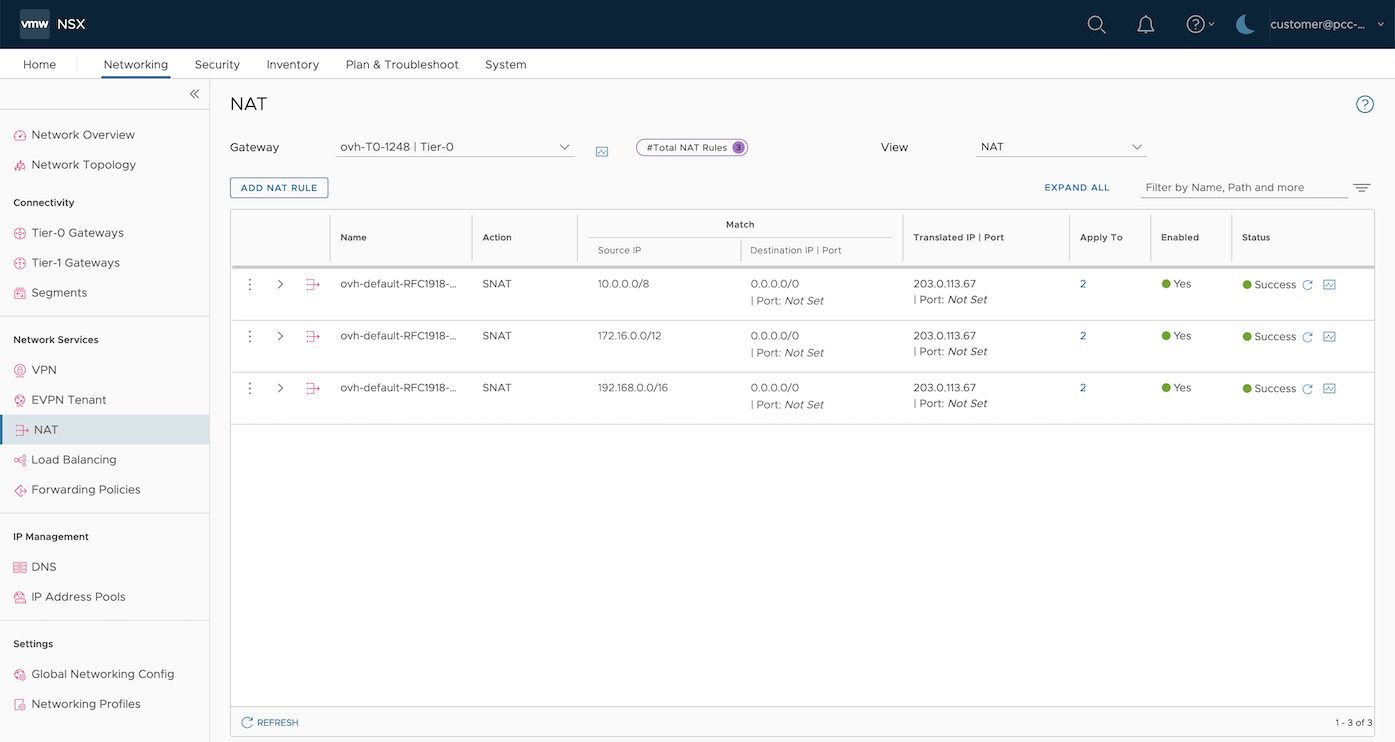
Select your T0 gateway "ovh-T0-xxxx" then click on Add NAT rule.
Set the following parameters:
- Nom: SAP Support
- Action: DNAT
- Source IP : 194.39.131.34/32
- Destination IP | Port : Public IP address of your NSX gateway | 3299
- Translated IP | Port : Private IP address of your SAProuter | Empty
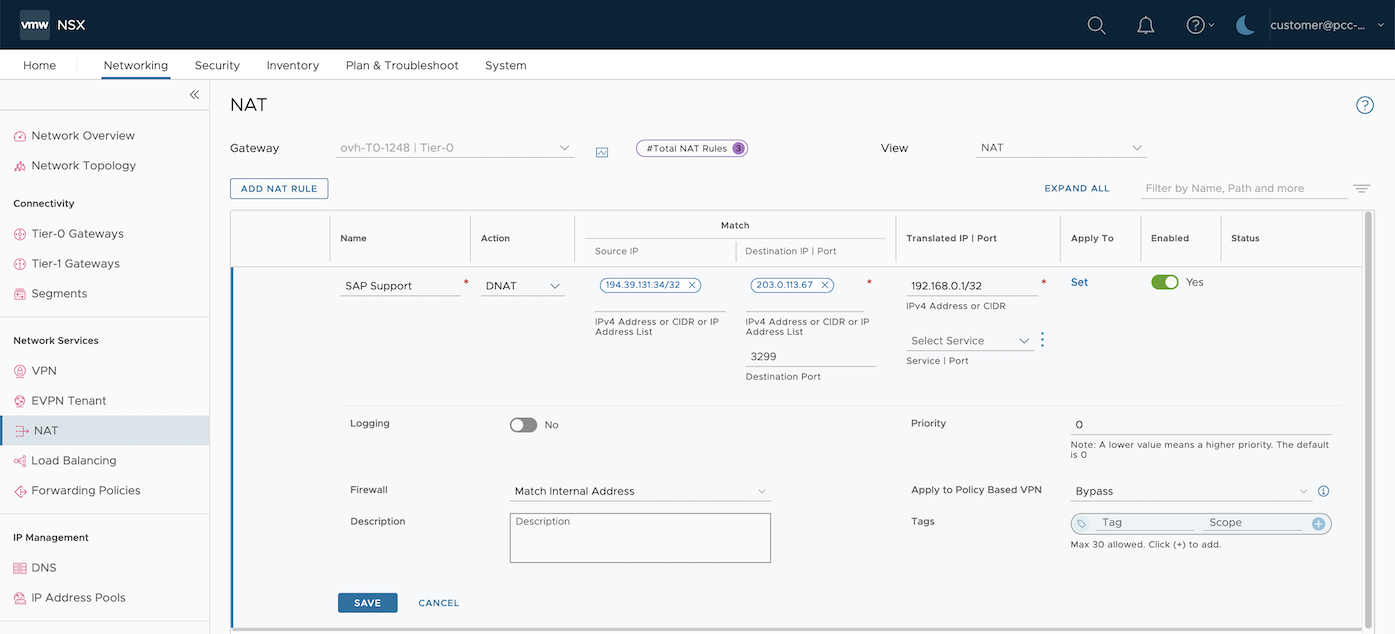
Once the DNAT rule has been created, click on Publish to update the configuration on the NSX gateway.
Now the traffic originating from the public IP address 194.39.131.34/32 held by SAP to your public IP address of your NSX gateway on the tcp/3299 port will be routed to your SAProuter.
SAProuter installation
To install the SAProuter service on your dedicated virtual machine, we recommend following instructions provided by the SAP support. Some steps must be done on your SAP Support Launchpad to secure the connection between SAP support and the SAProuter.
We advise updating your SAProuter as often as you can and deploying it in a monitored and isolated network of your SAP infrastructure. The SAProuter should communicate with your SAP infrastructure on restricted ports.
Find more information about the firewall rule with an NSX gateway in our guide.
Go further
If you need training or technical assistance to implement our solutions, contact your sales representative or click on this link to get a quote and ask our Professional Services experts for assisting you on your specific use case of your project.
Join our community of users on https://community.ovh.com/en/.